Cloud IAM Permission Model
Cloud Identity and Access Management (IAM) is the system that controls which principals (users, service accounts, roles) are authorized to perform which actions on which resources — enforcing the principle of least privilege across cloud infrastructure.
Cloud Identity and Access Management (IAM) is the system that controls which principals (users, service accounts, roles) are authorized to perform which actions on which resources — enforcing the principle of least privilege across cloud infrastructure.
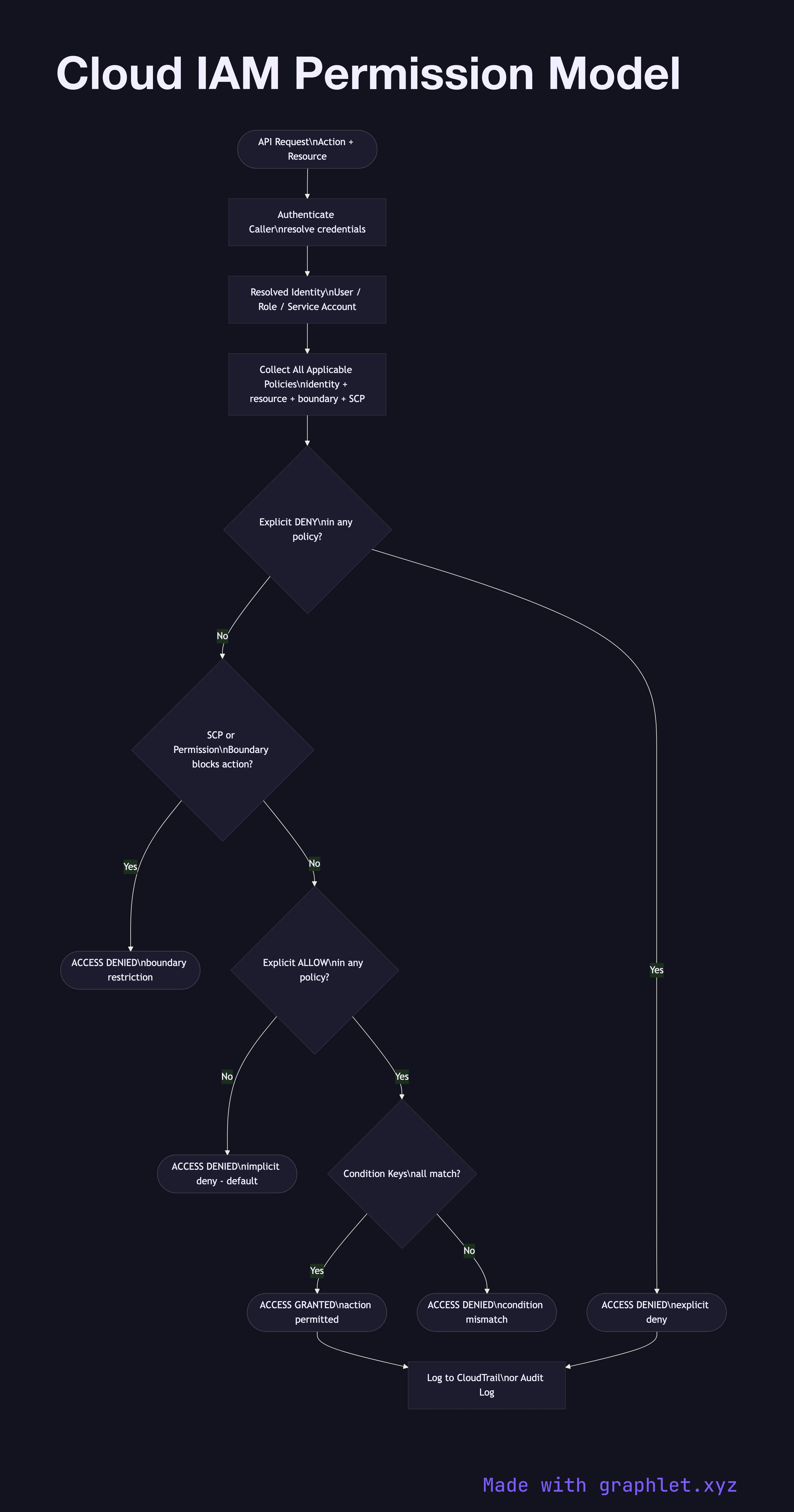
IAM in major cloud providers (AWS IAM, Google Cloud IAM, Azure RBAC) follows a consistent request evaluation model:
1. Identity resolution: The caller presents credentials (access key, OAuth token, instance metadata token). The IAM system resolves these to an identity — an IAM user, role, service account, or federated identity.
2. Policy collection: All policies attached to or applicable to that identity are gathered: identity-based policies (attached to the user/role), resource-based policies (attached to the target resource, e.g., S3 bucket policy), permission boundaries, session policies (for assumed roles), and organization SCPs (Service Control Policies).
3. Evaluation logic: AWS follows the IAM policy evaluation order: explicit Deny always wins over any Allow. If no explicit Deny exists, an explicit Allow in any applicable policy grants access. If neither Deny nor Allow applies, the default is implicit Deny — access is denied.
4. Condition evaluation: Policies may include condition keys (e.g., aws:SourceIp, aws:RequestedRegion, s3:prefix) that must match for the policy statement to apply.
Understanding IAM evaluation order is critical for debugging "access denied" errors. See Cloud Secret Management for how secrets rotate and are scoped to IAM roles, and Serverless Architecture for how Lambda execution roles are granted IAM permissions.