Access Control Decision Flow
The access control decision flow is the sequence of checks an application performs on every incoming request to determine whether to allow or deny it. It combines authentication (who are you?) and authorization (are you allowed to do this?) into a layered enforcement pipeline.
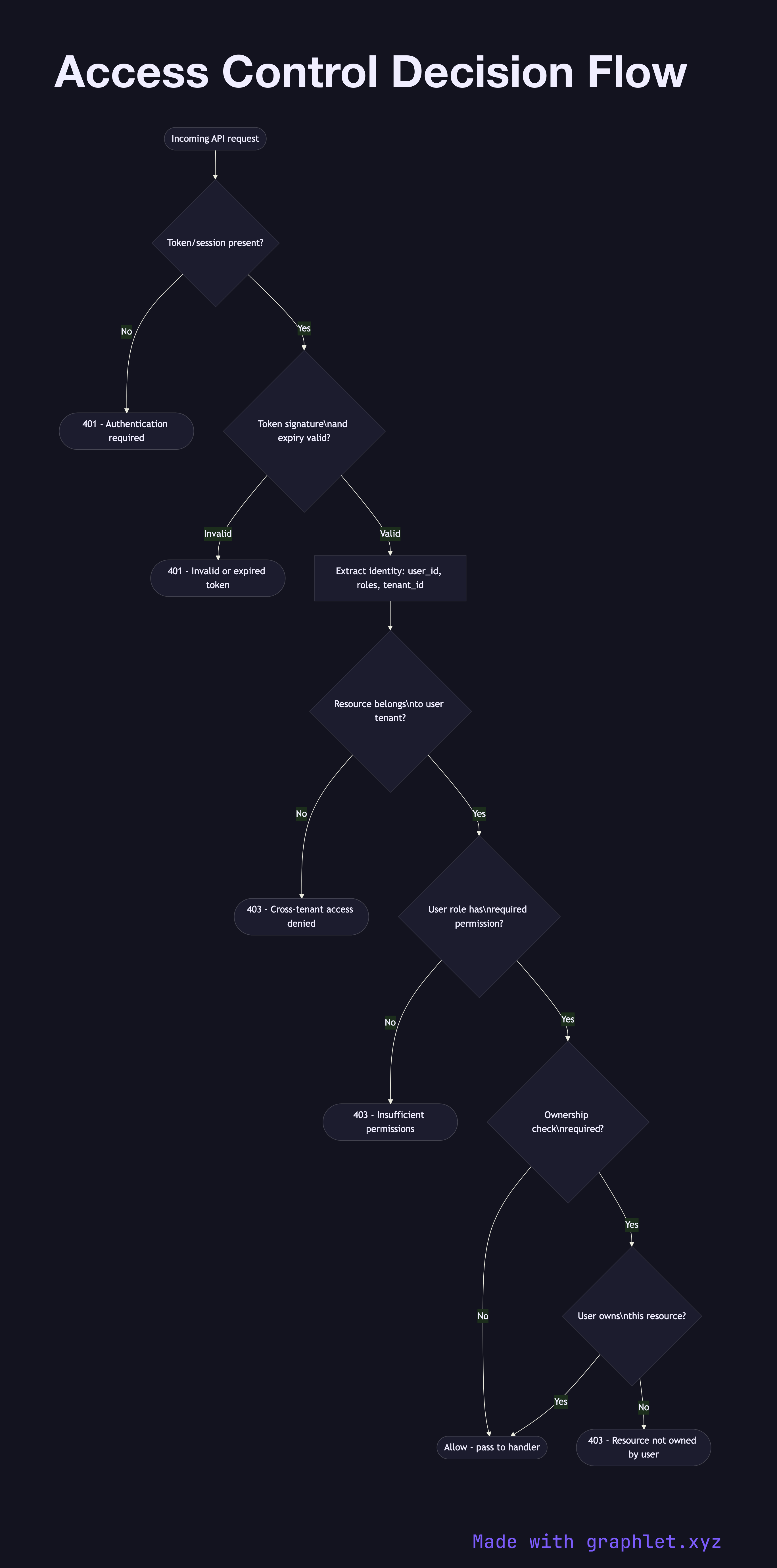
The access control decision flow is the sequence of checks an application performs on every incoming request to determine whether to allow or deny it. It combines authentication (who are you?) and authorization (are you allowed to do this?) into a layered enforcement pipeline.
The first gate is authentication validation. For JWT-based systems, this means extracting the Authorization: Bearer header, verifying the token's signature, and checking that it hasn't expired. If any of these fail, the request is rejected with a 401 Unauthorized response before any application logic runs. For session-based systems, the session cookie is validated against the session store.
Once the caller's identity is established, tenant context is extracted (in multi-tenant systems) and verified — confirming that the resource being requested belongs to the same tenant as the authenticated user. This prevents cross-tenant data access even with valid tokens.
The next layer is authorization: given who the user is, can they perform the requested action on the requested resource? This typically involves loading the user's roles and expanding them to permissions (RBAC), or evaluating attribute-based policies (ABAC). The required permission for the route is compared against the user's effective permissions.
Some systems add resource ownership checks after the role check — for example, confirming that a user with the editor role is only editing their own posts, not other users' posts. This is the hybrid RBAC + ABAC approach common in practice.
If all checks pass, the request proceeds to the handler. If any check fails, the appropriate HTTP error is returned: 401 for unauthenticated, 403 for authenticated but unauthorized. This layered approach ensures security failures are caught at the earliest possible point. See RBAC Authorization Model and ABAC Authorization Model for the underlying permission structures.