


Free Mermaid diagrams covering OAuth2, JWT, SSO, SAML, RBAC, MFA and all major authentication patterns.
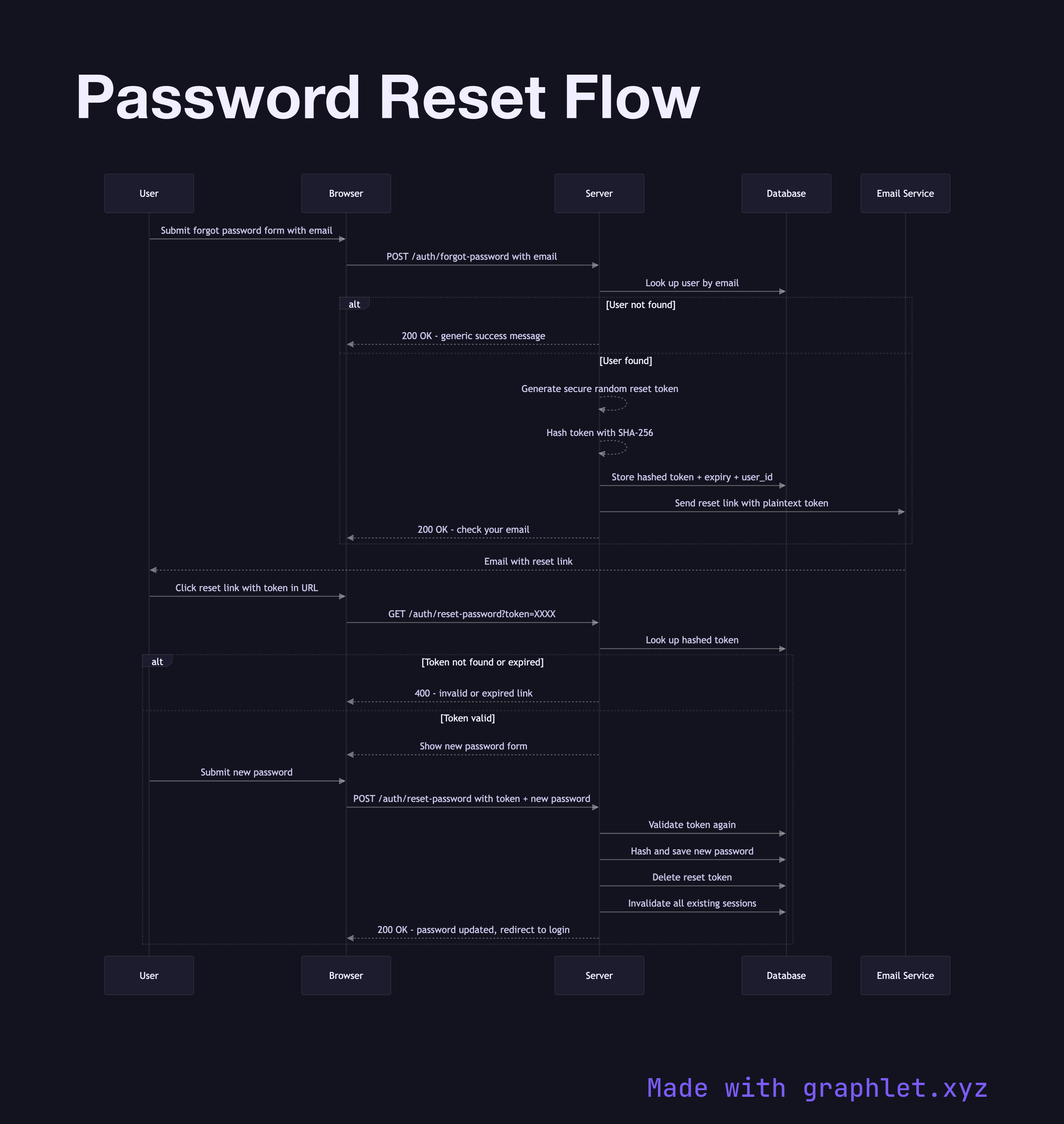
Authentication and authorization are the gatekeepers of every modern application. Whether you're implementing a simple username/password flow or a complex federated identity system spanning multiple services, understanding the underlying protocols prevents security vulnerabilities and reduces integration friction.
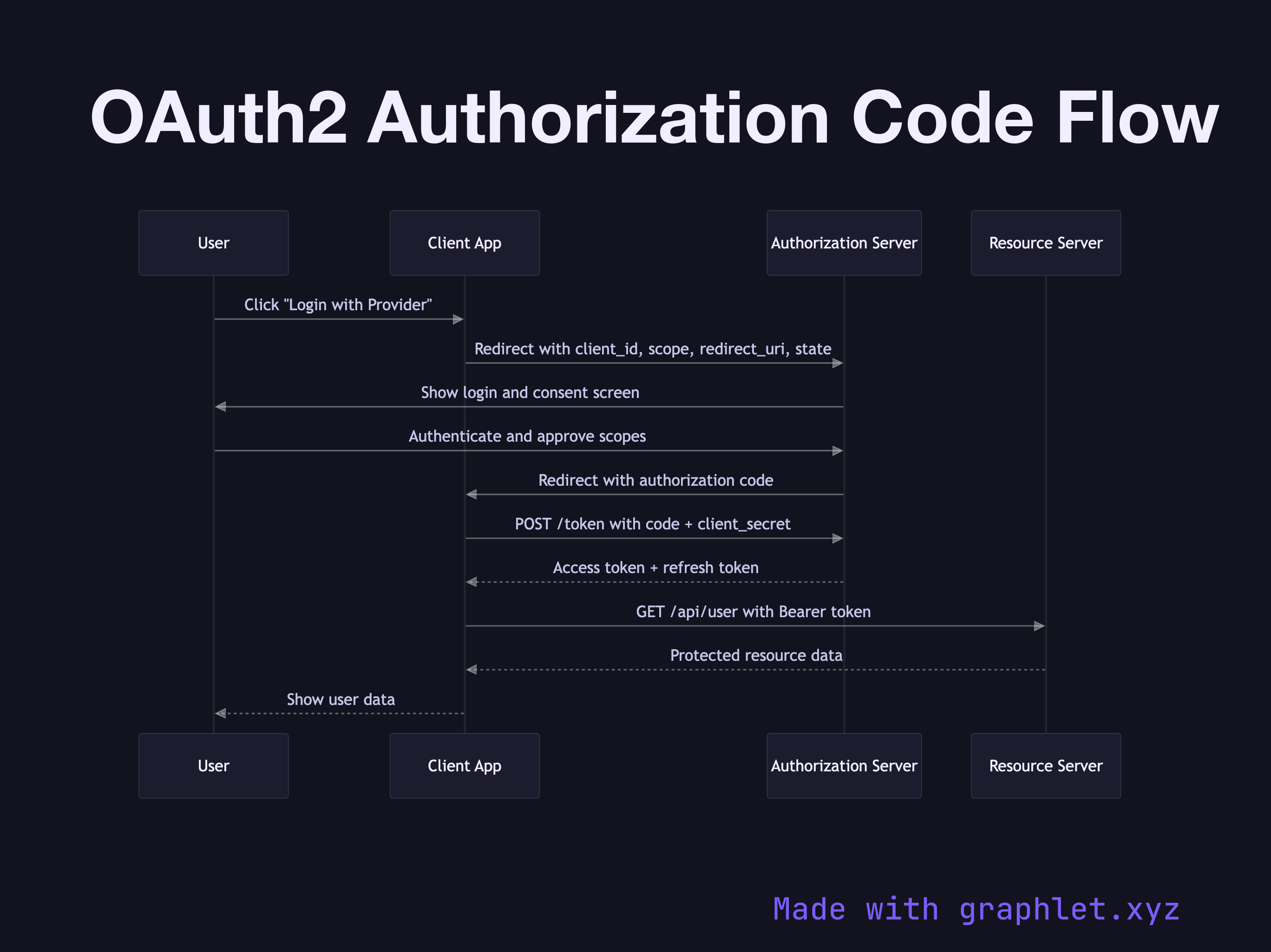
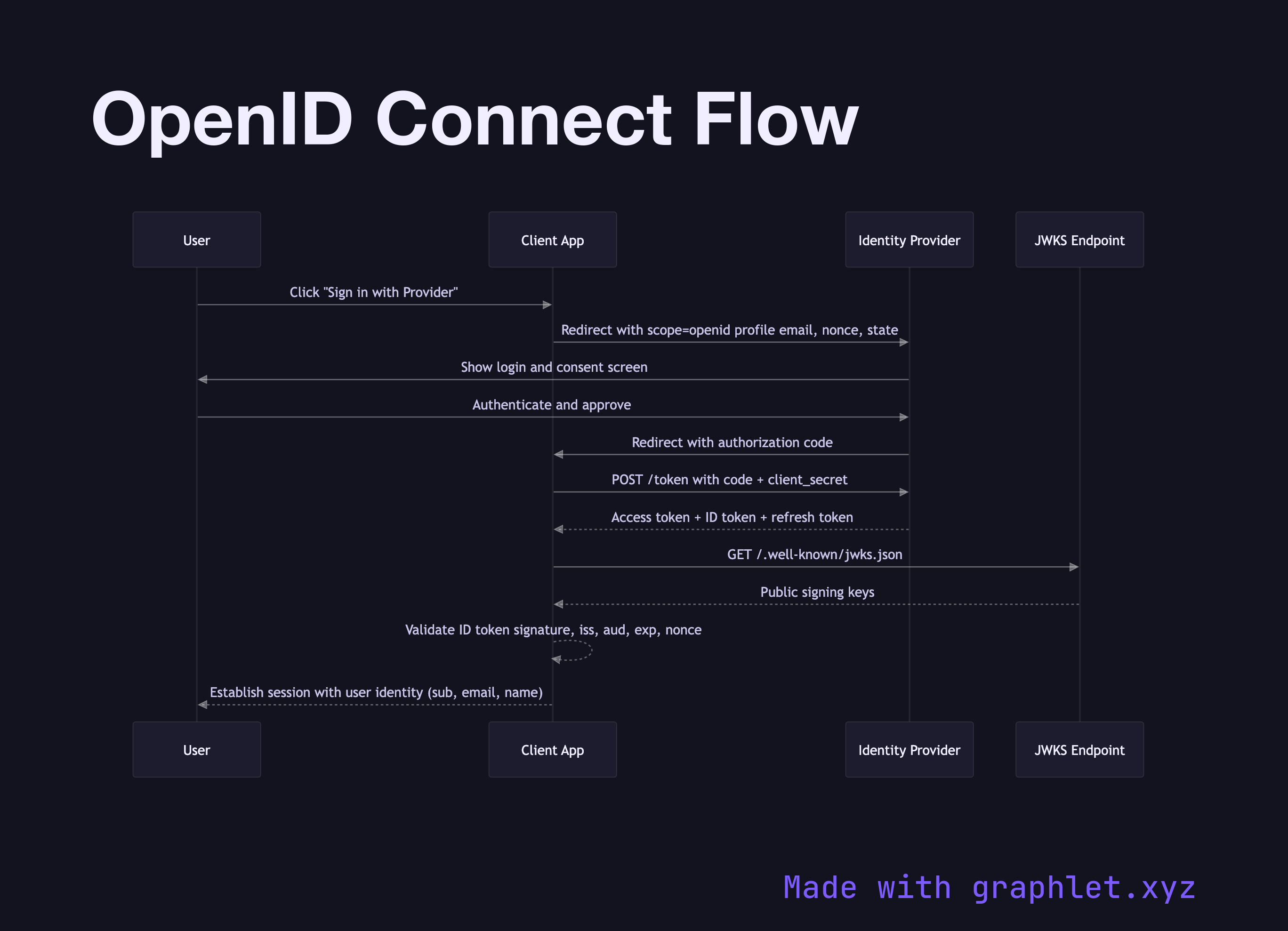
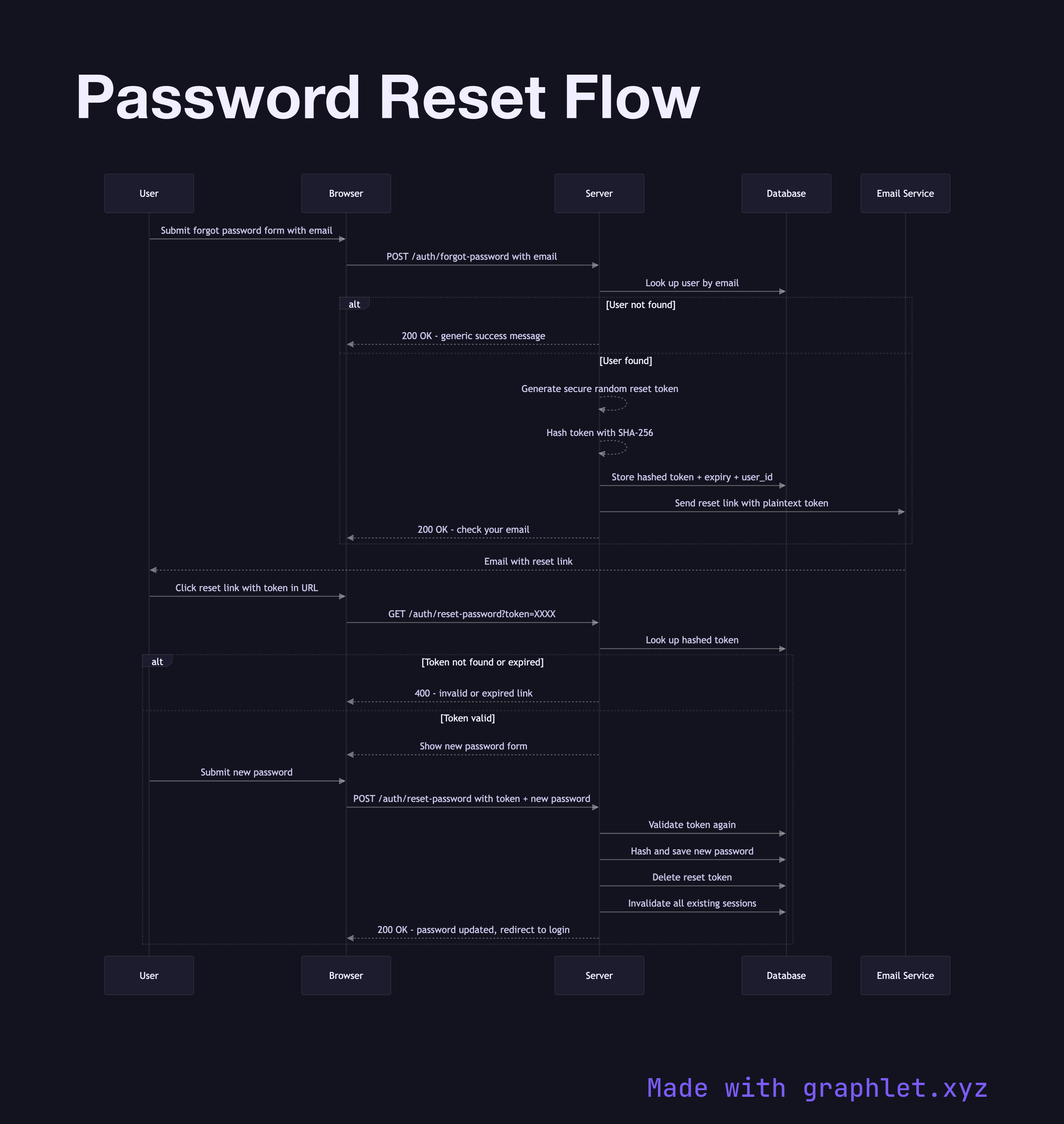
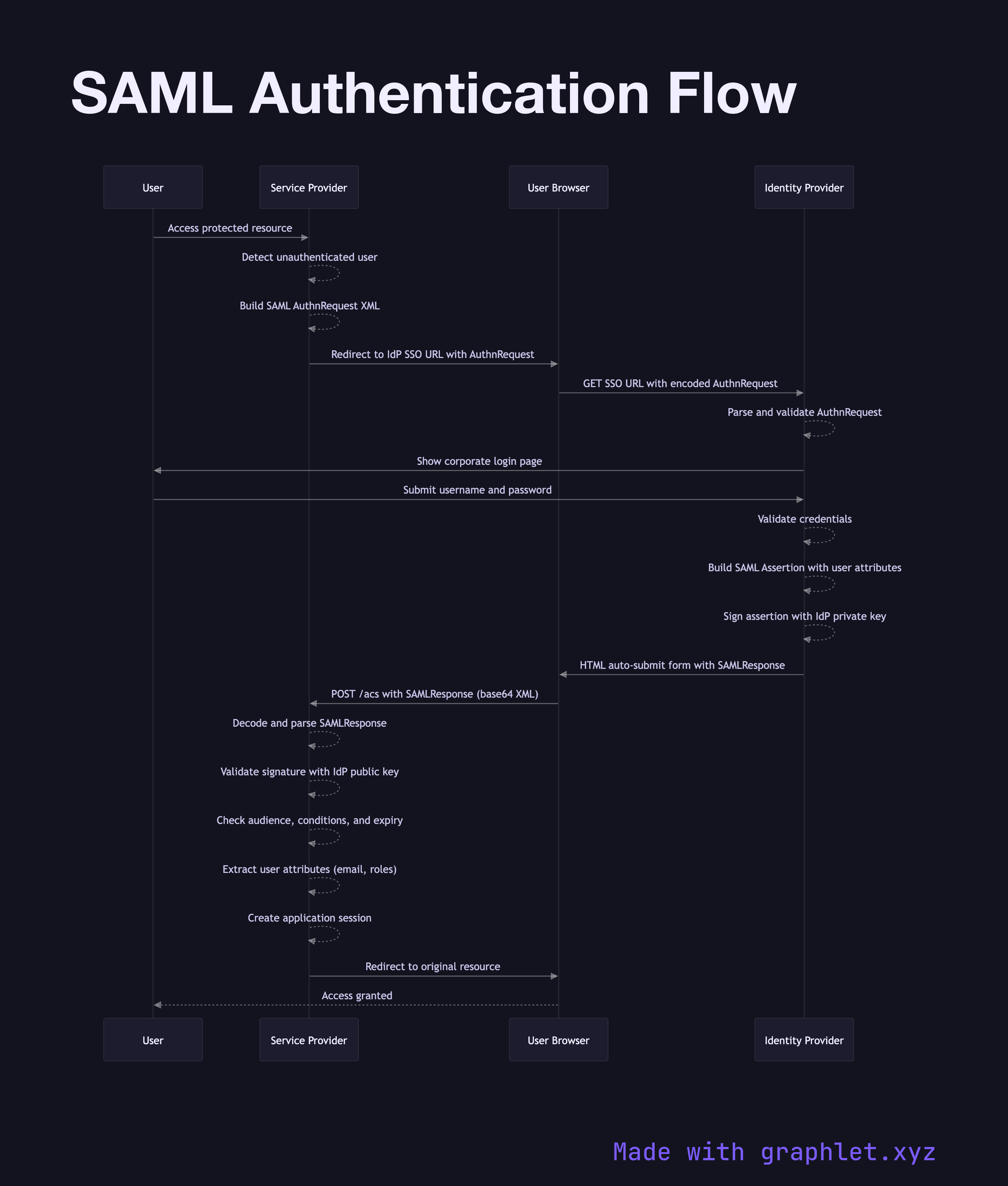
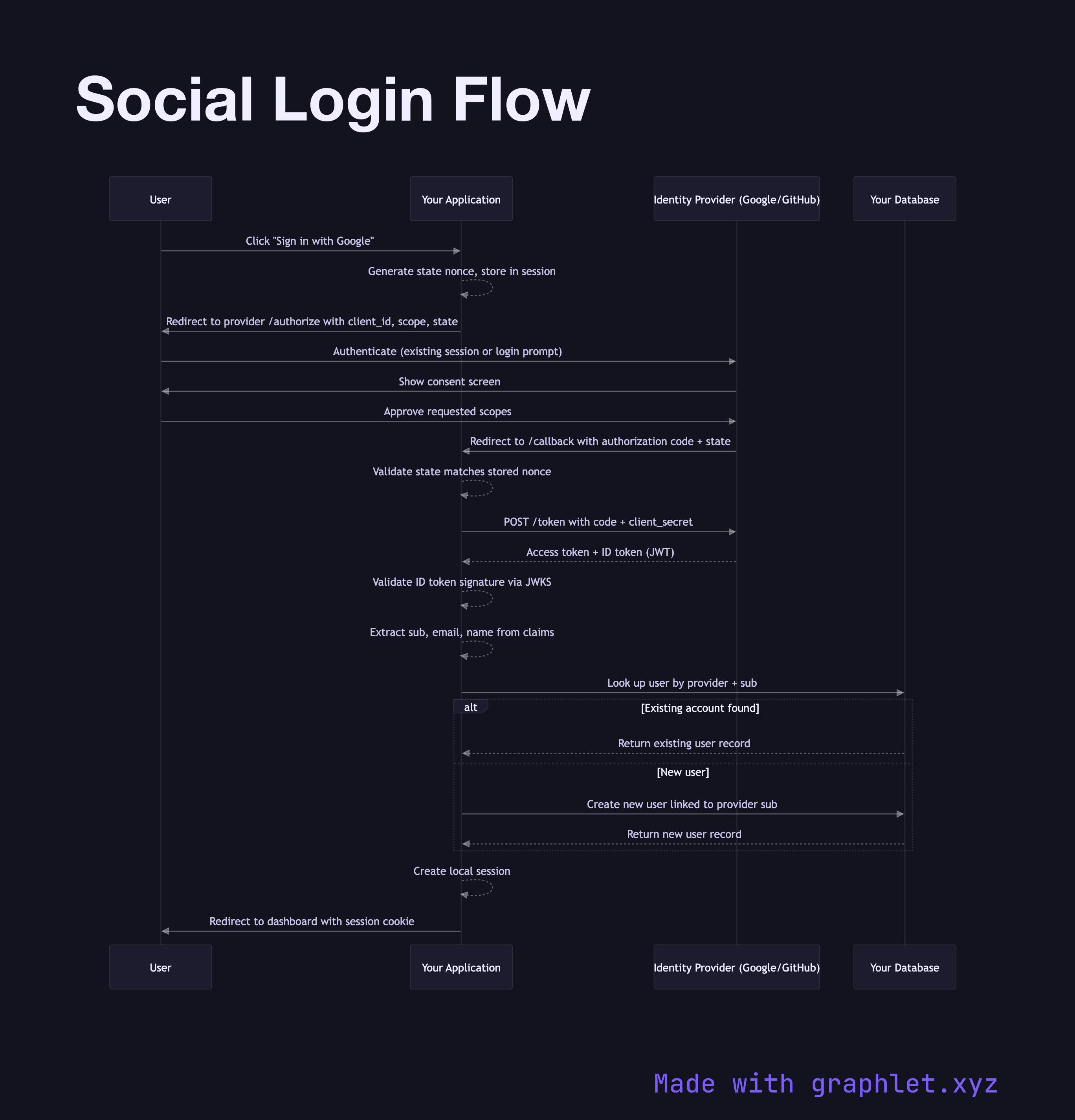
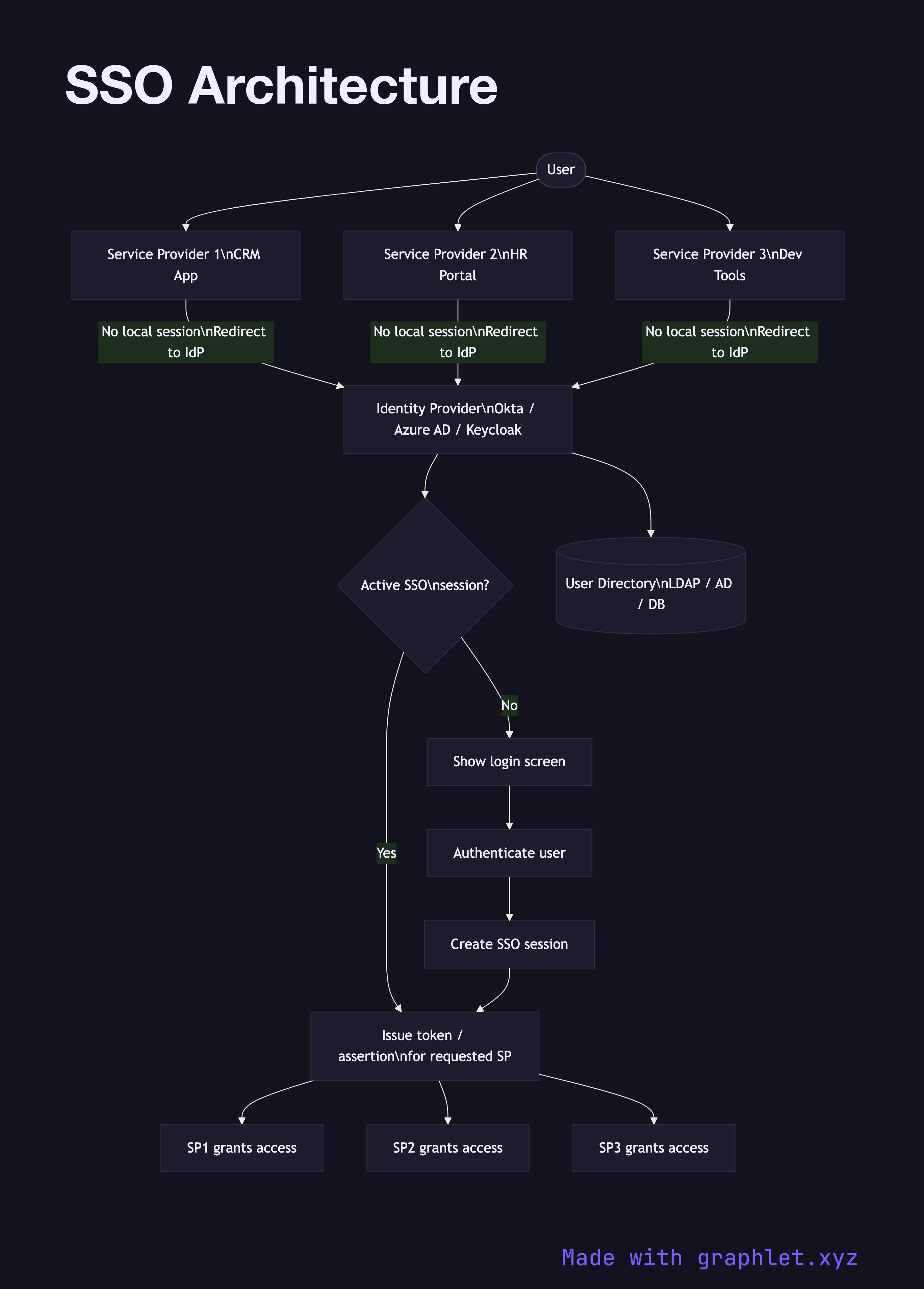
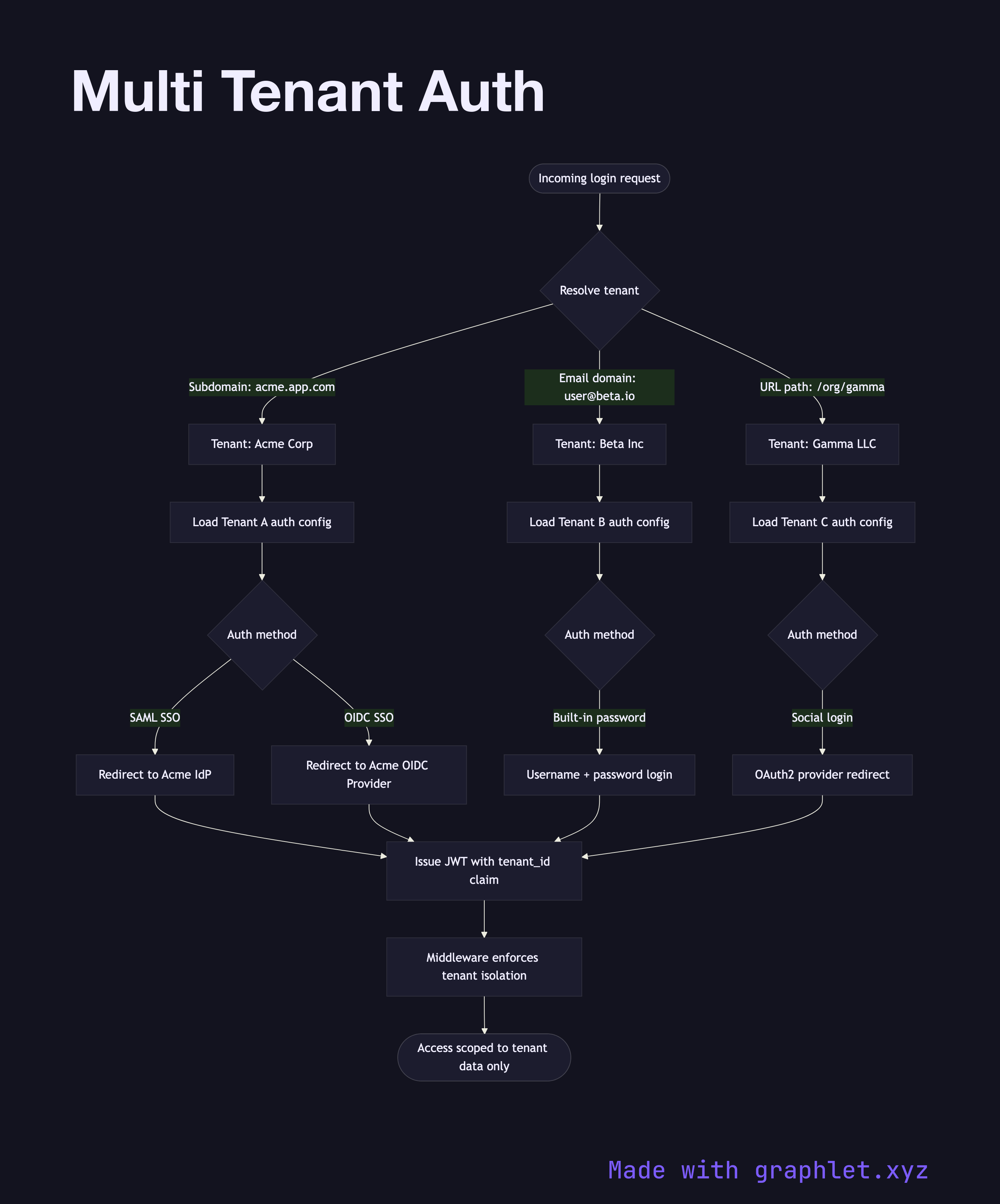
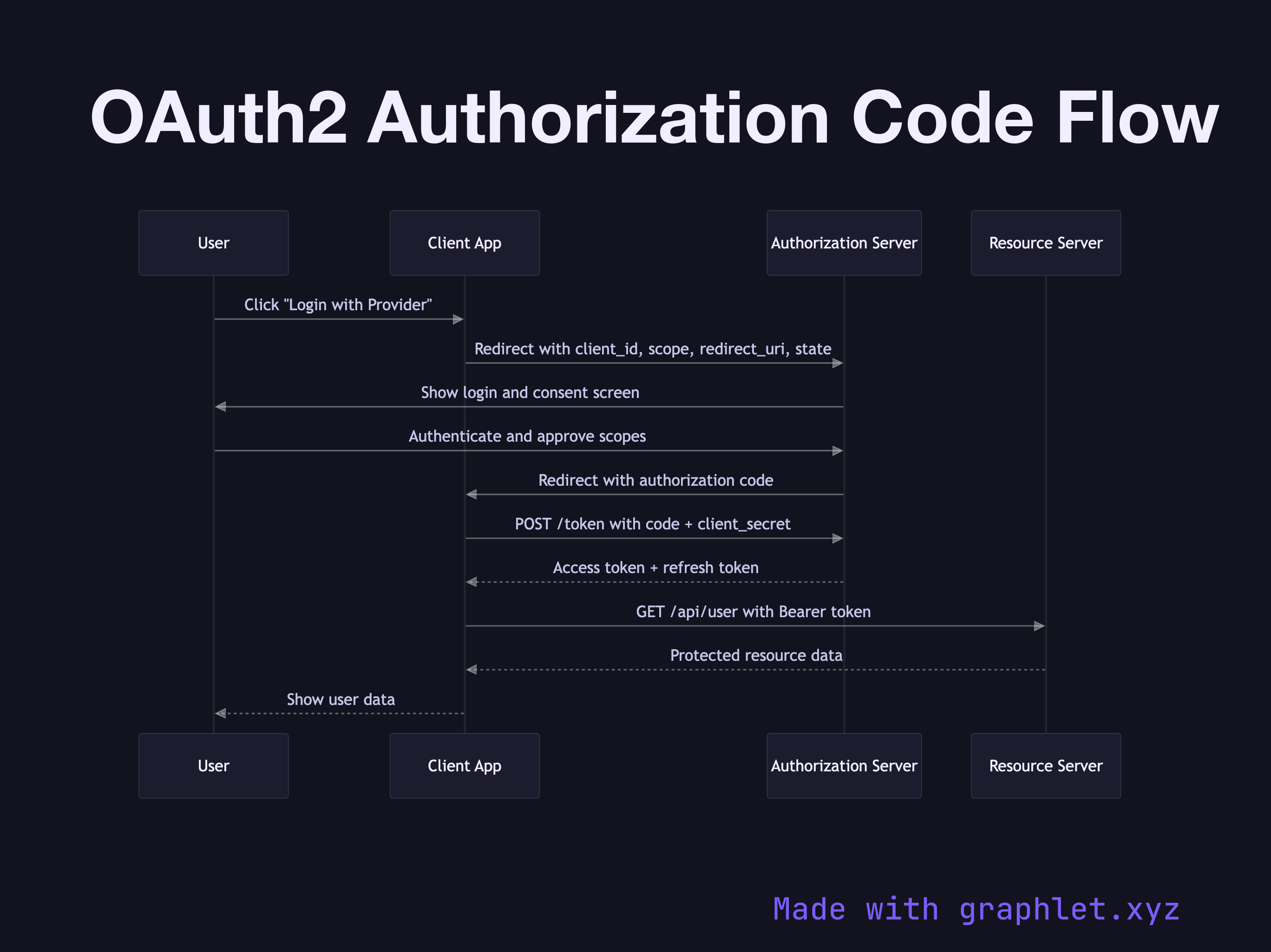
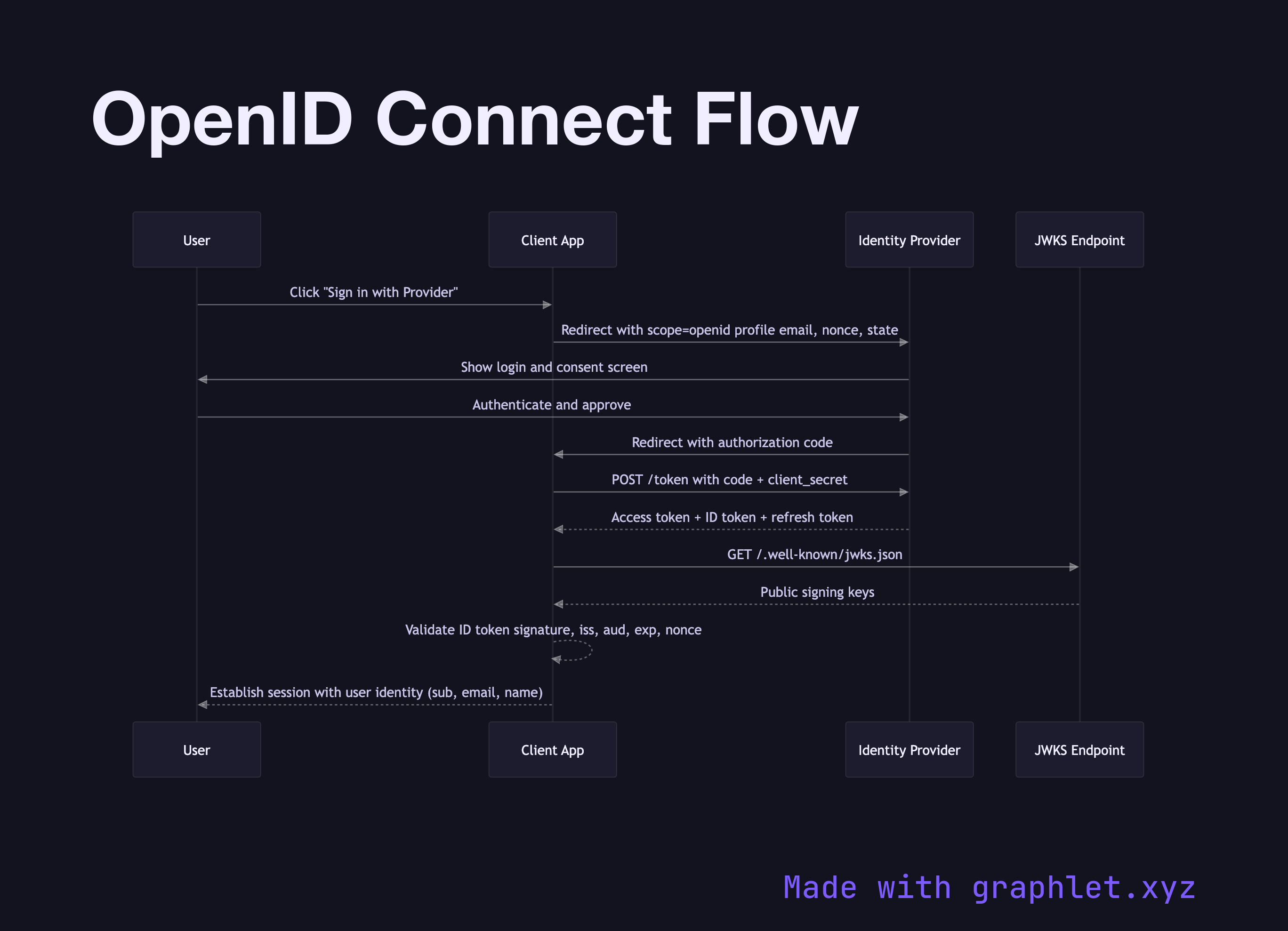
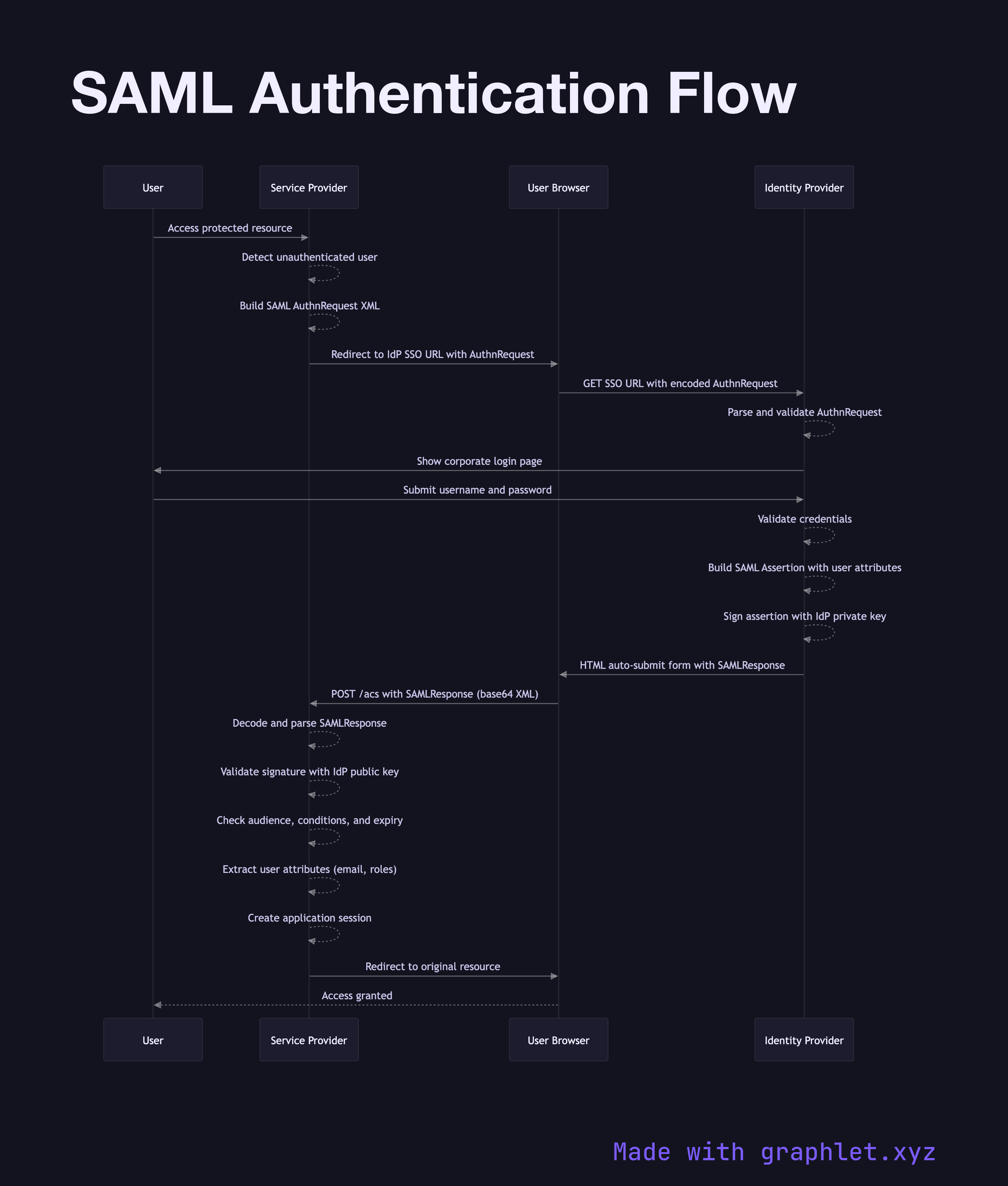
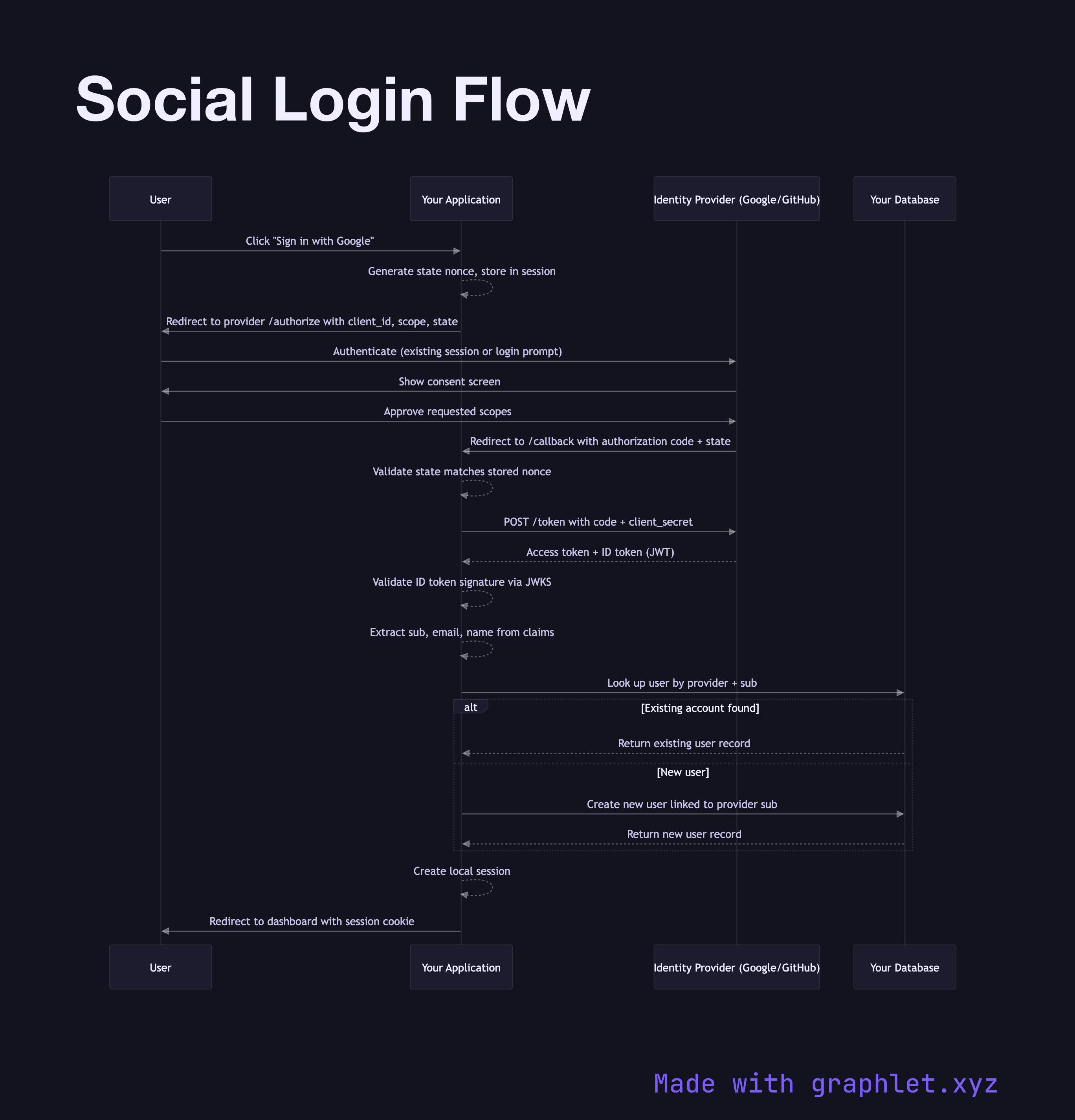
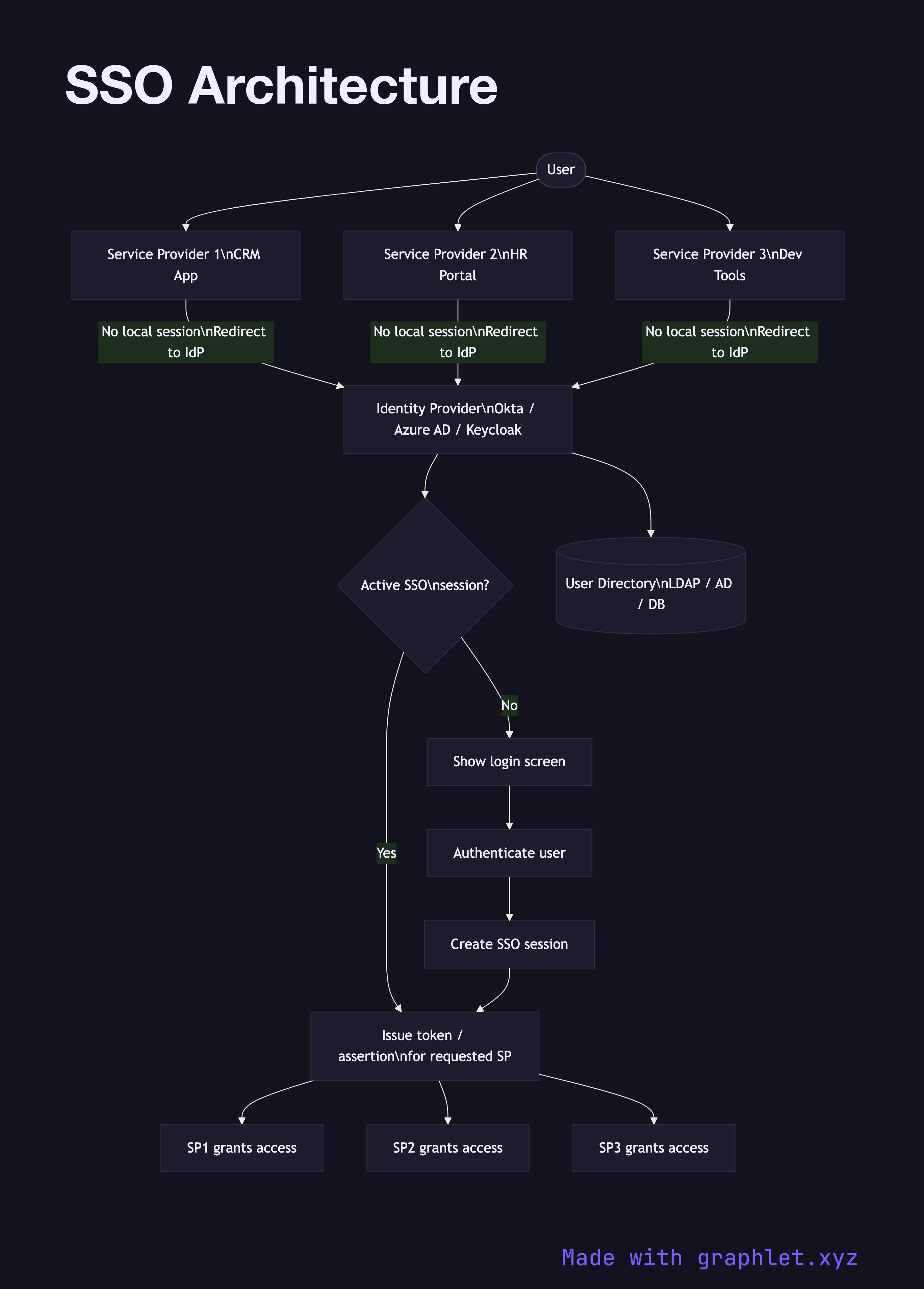
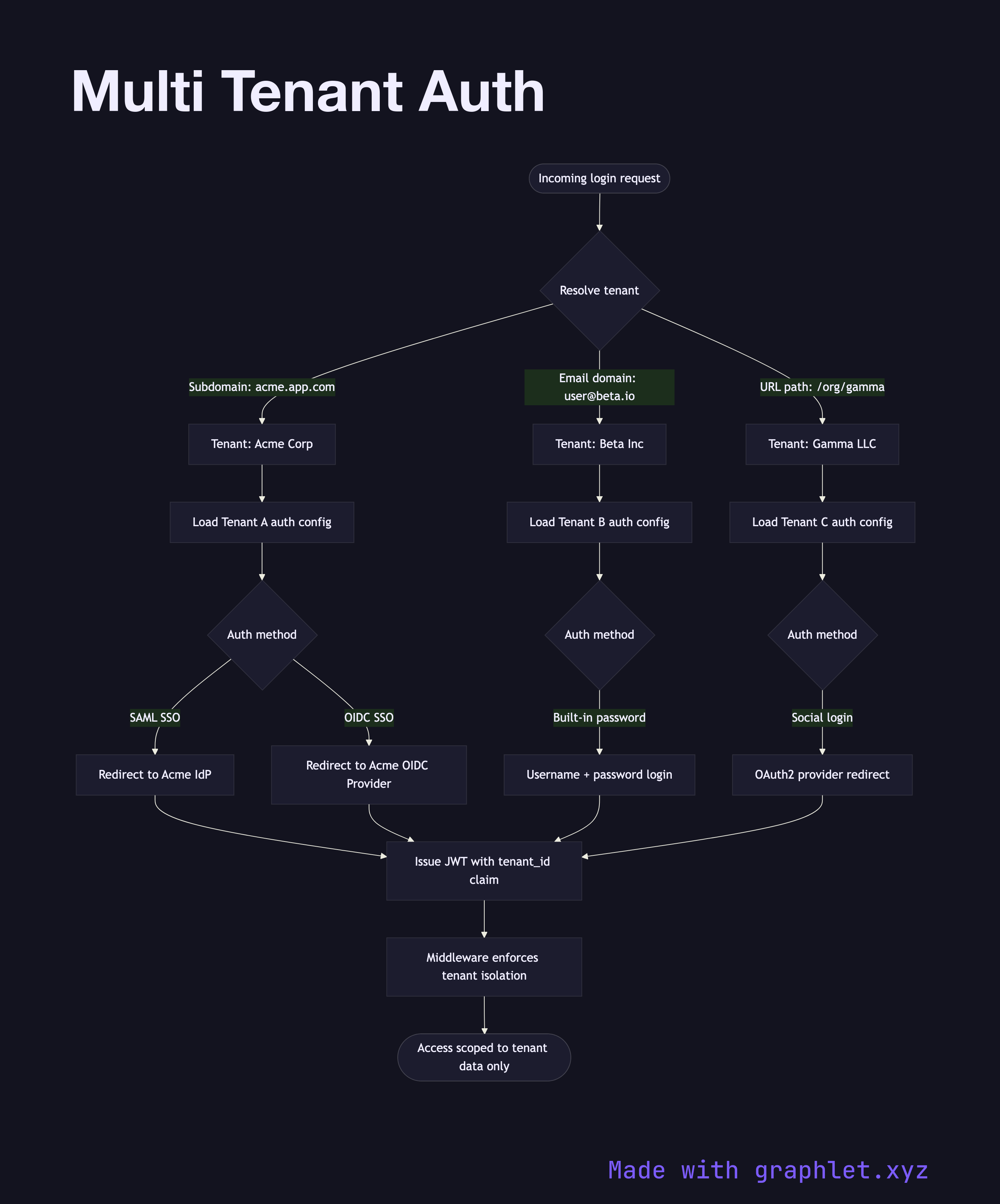
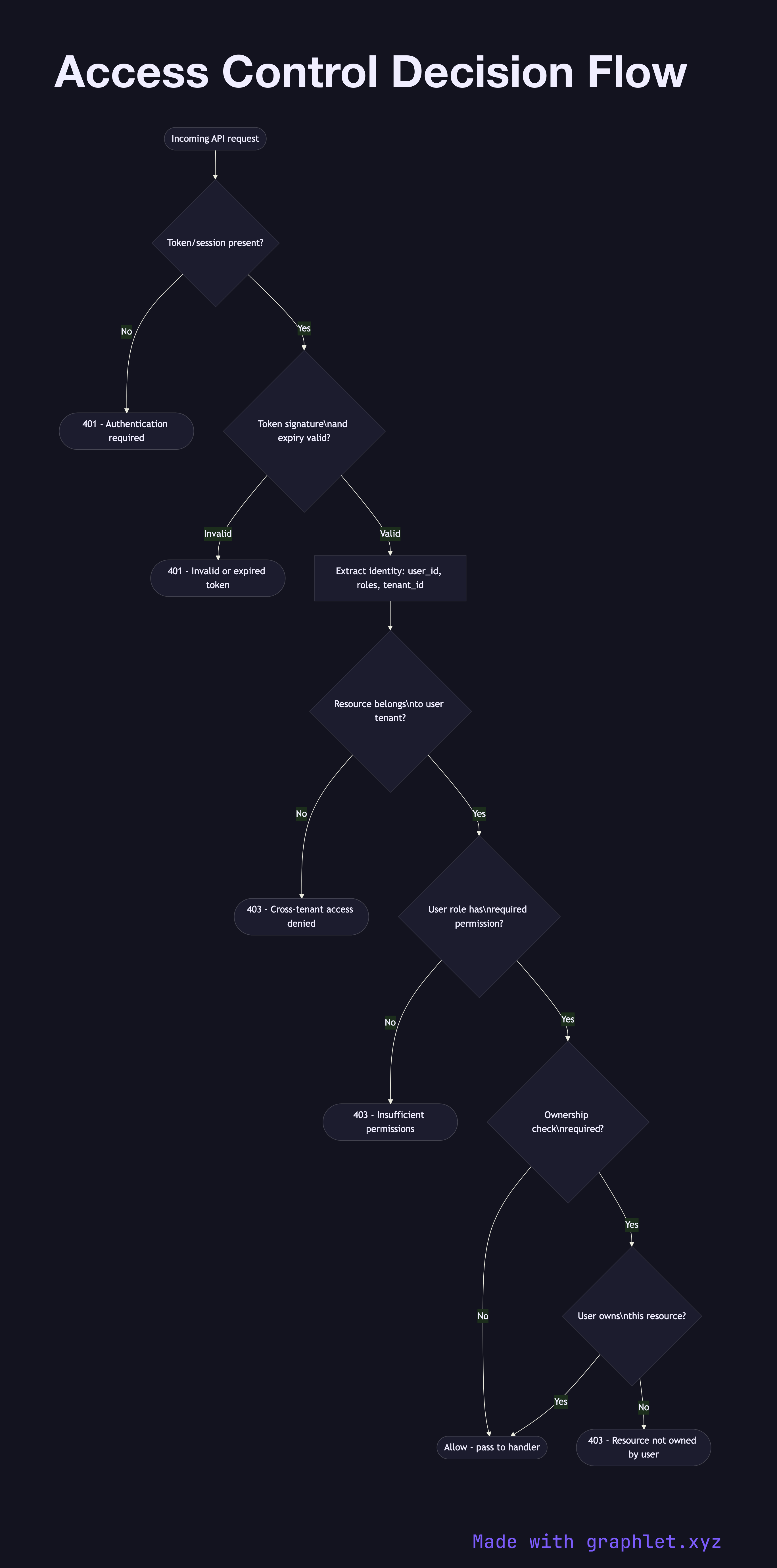
This collection covers the full spectrum of auth patterns developers encounter. The delegation-focused flows begin with OAuth2 Authorization Code Flow — the standard for user-facing apps — and OAuth2 Client Credentials Flow for machine-to-machine communication. OpenID Connect Flow layers identity on top of OAuth2, while SAML Authentication Flow covers the enterprise SSO standard still prevalent in large organizations.
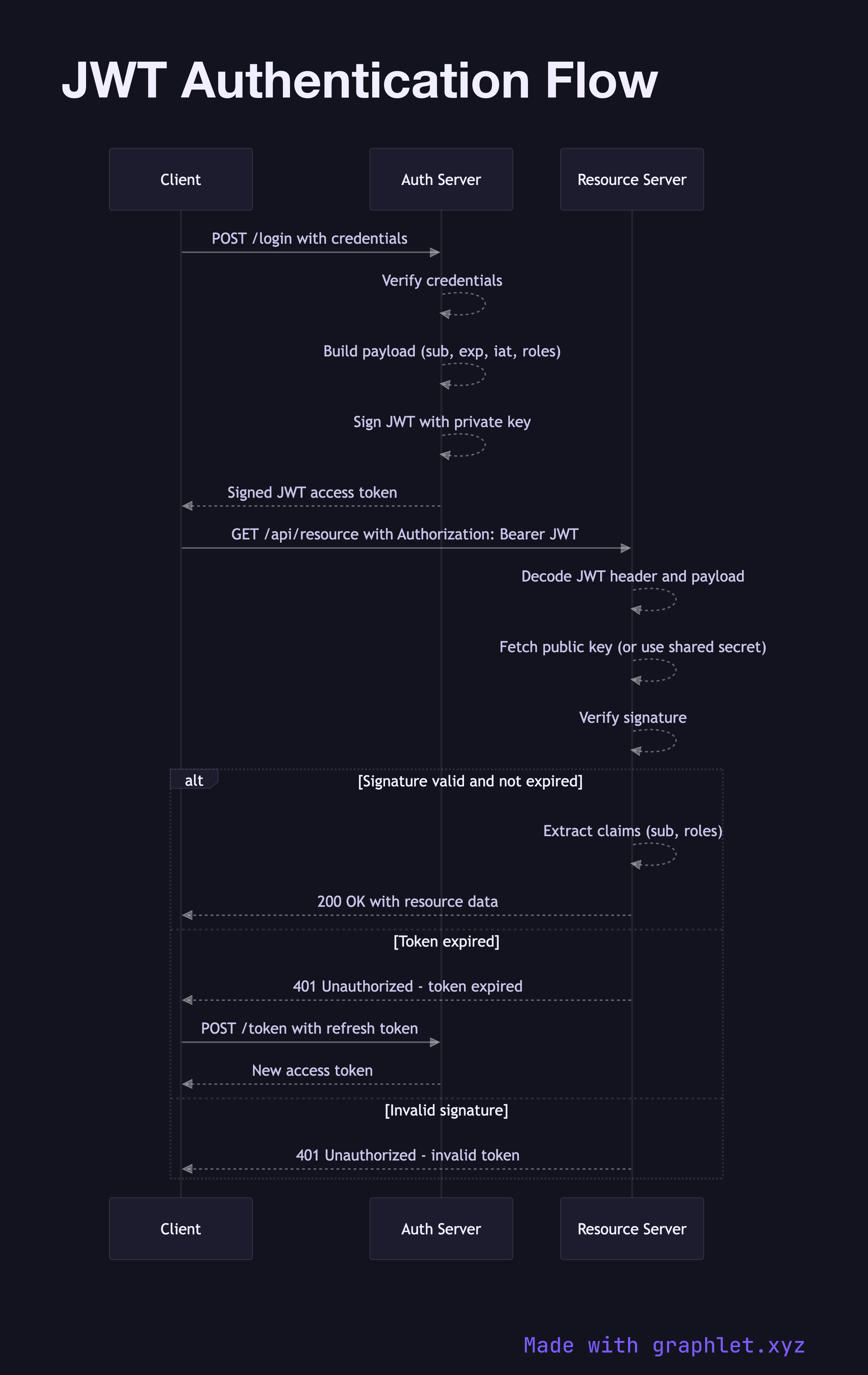
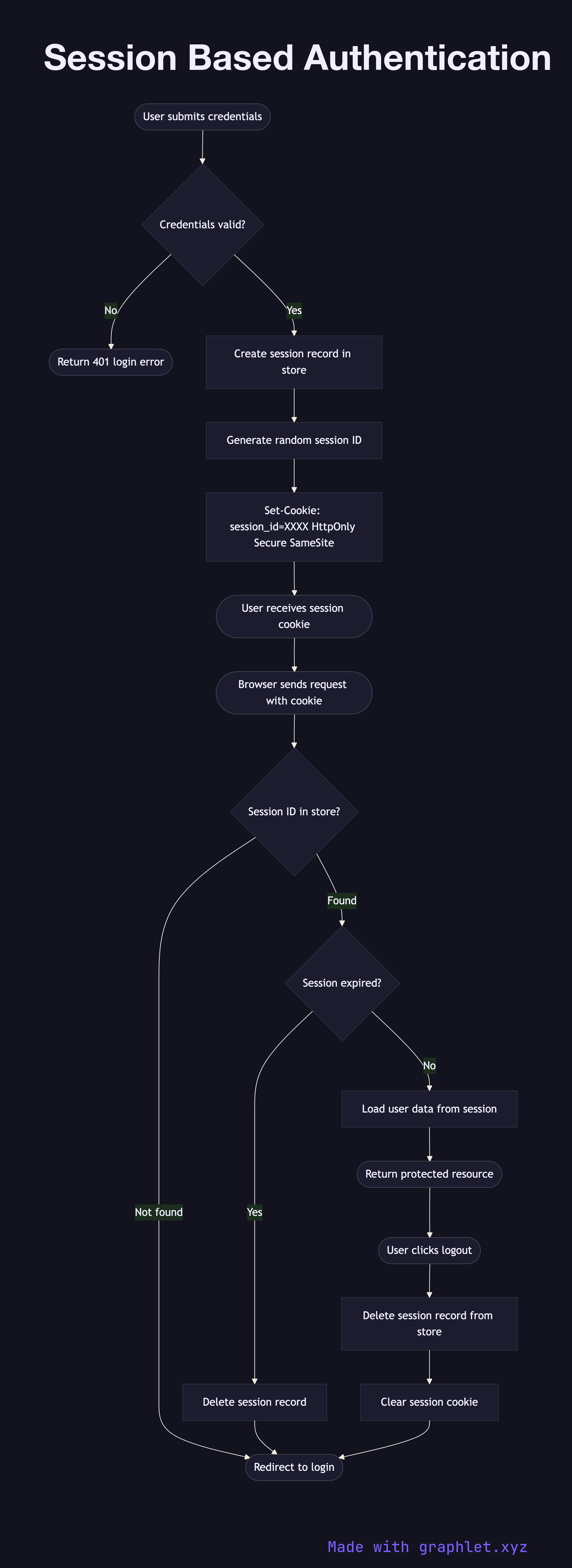
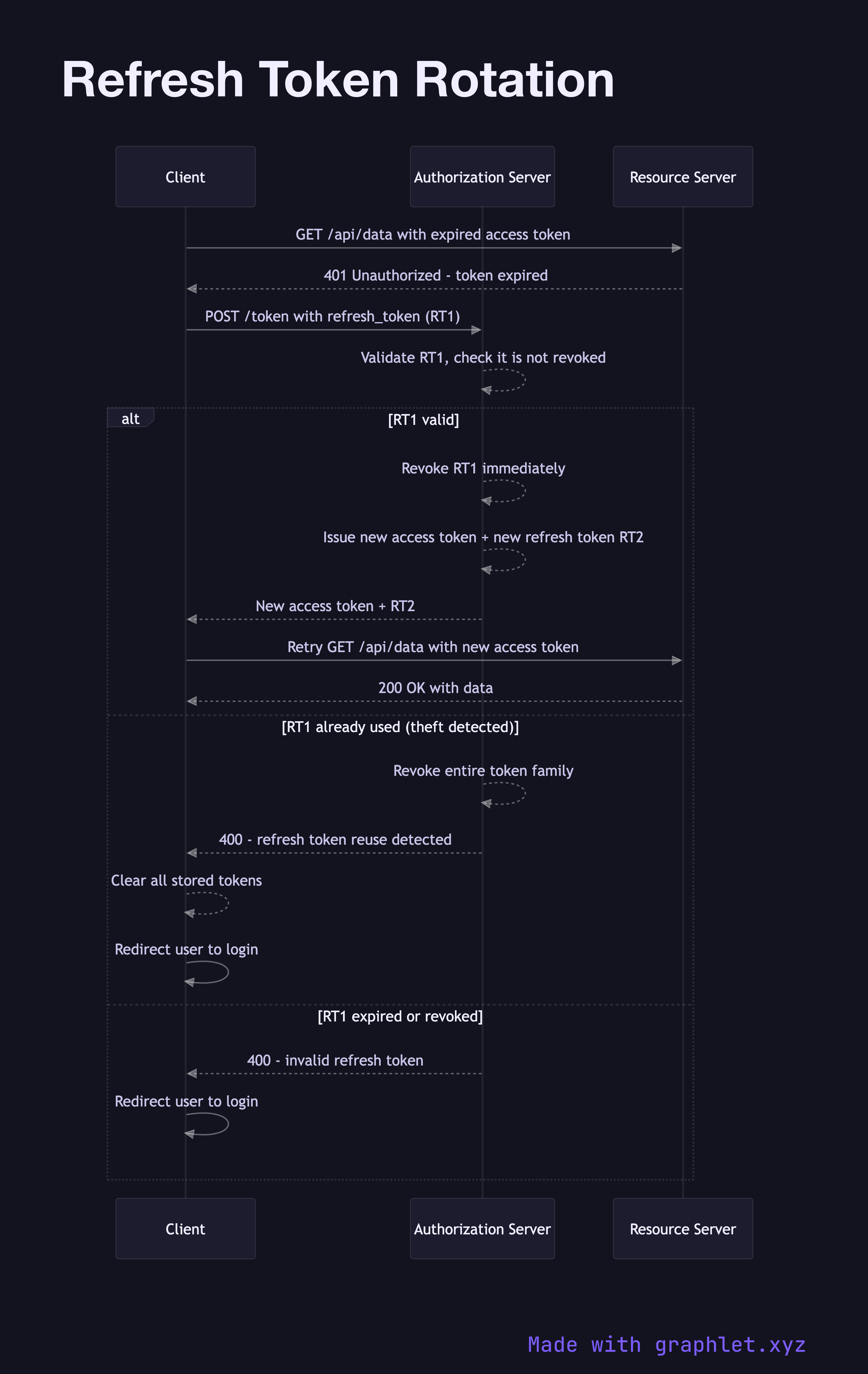
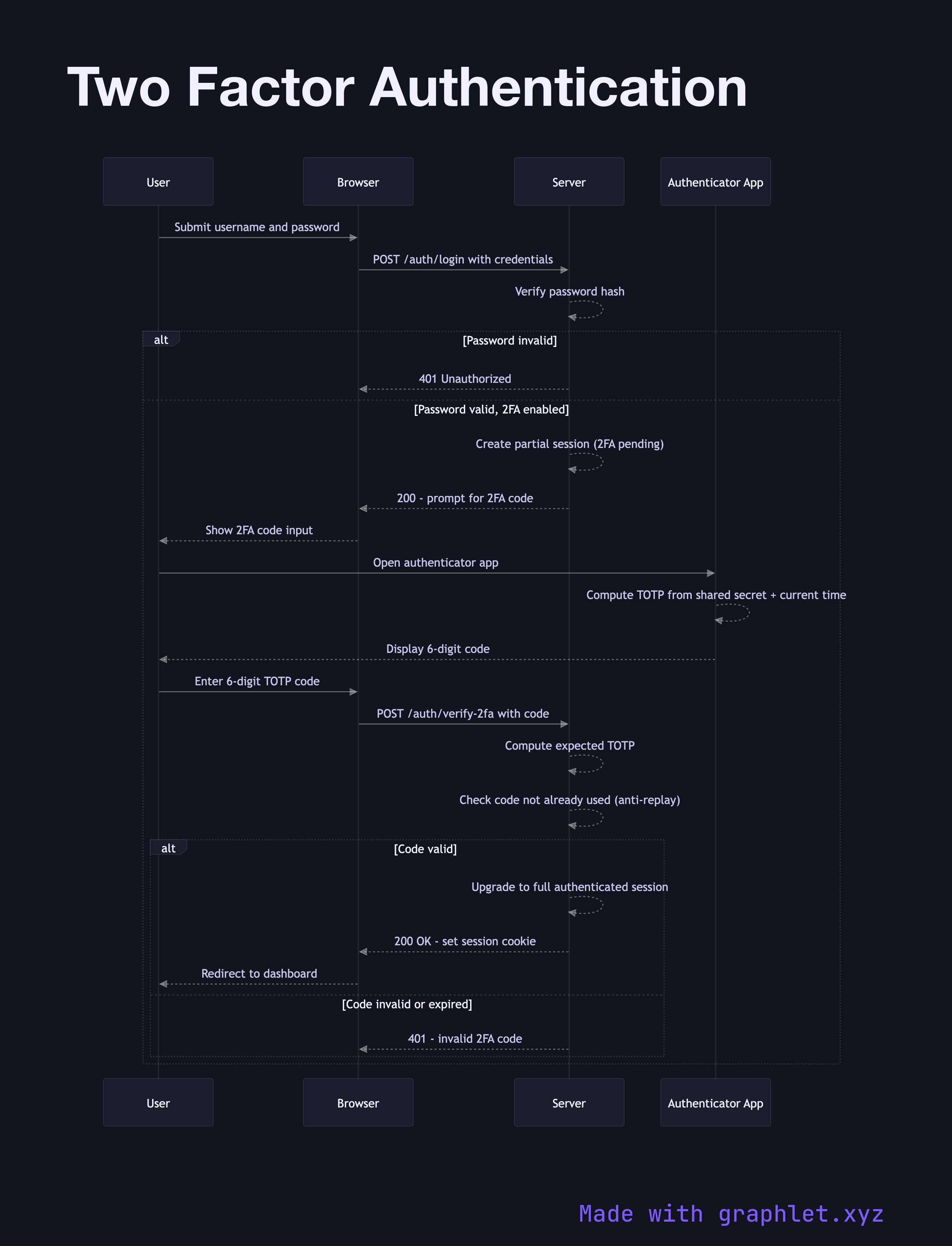
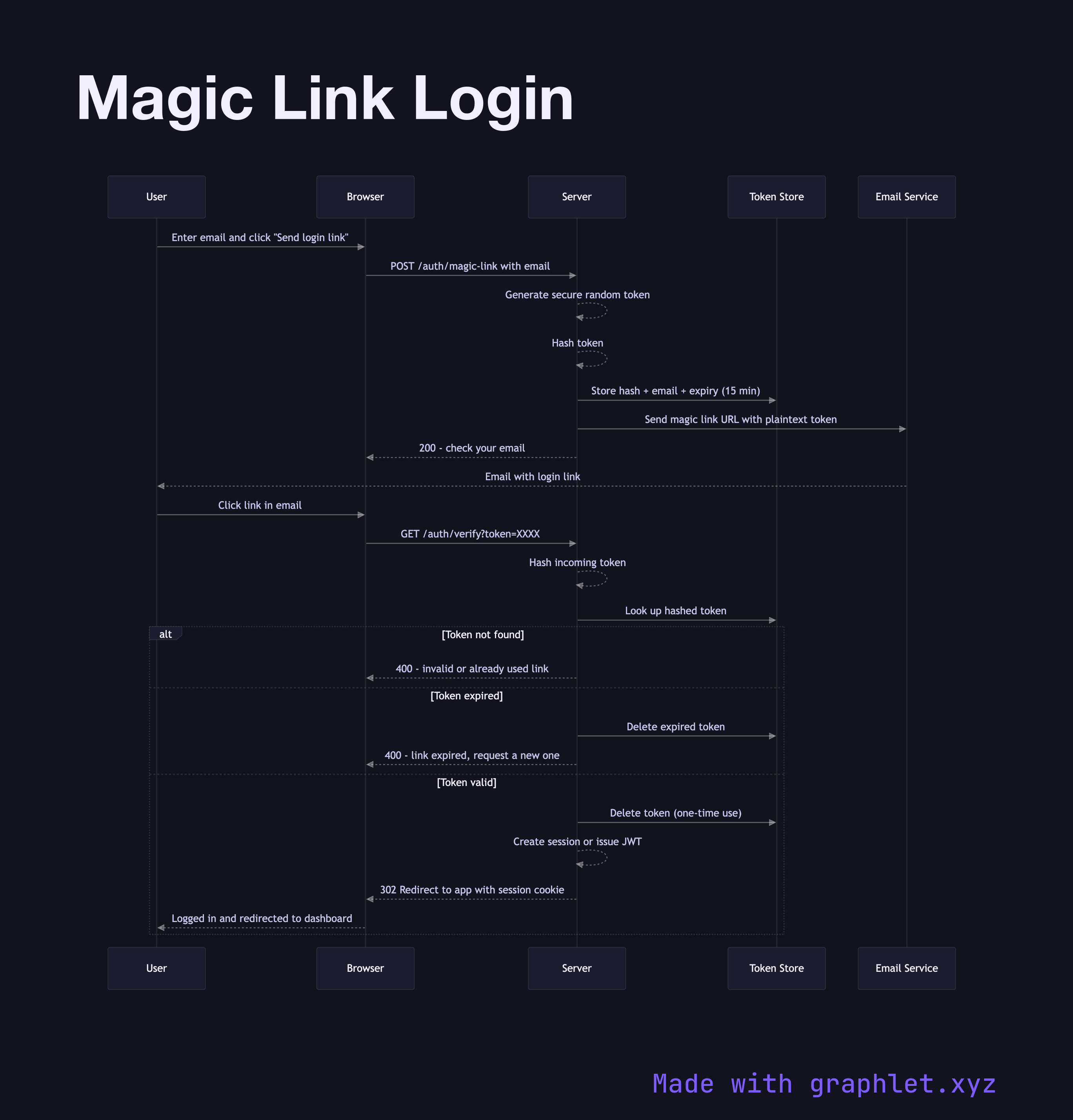
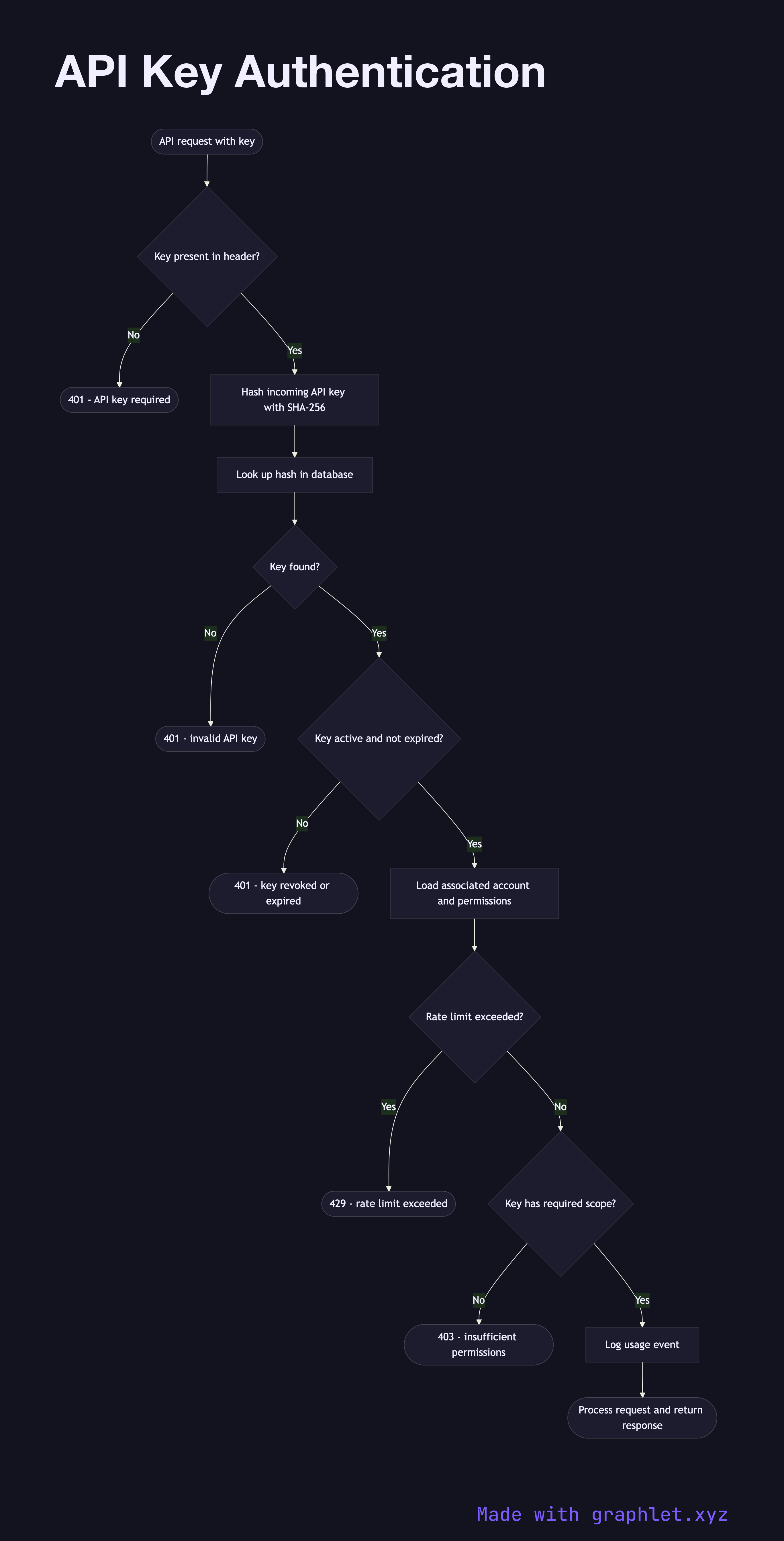
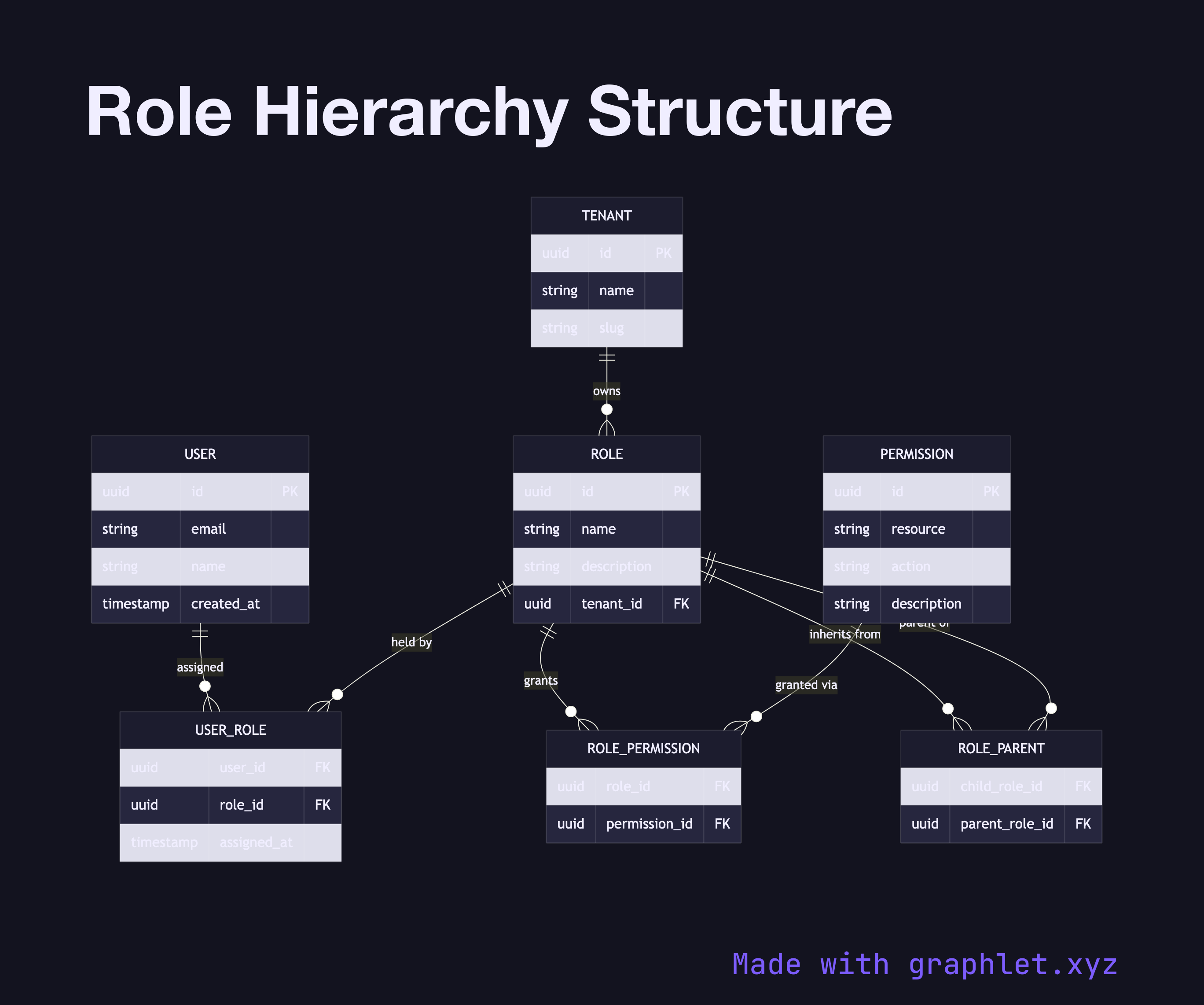
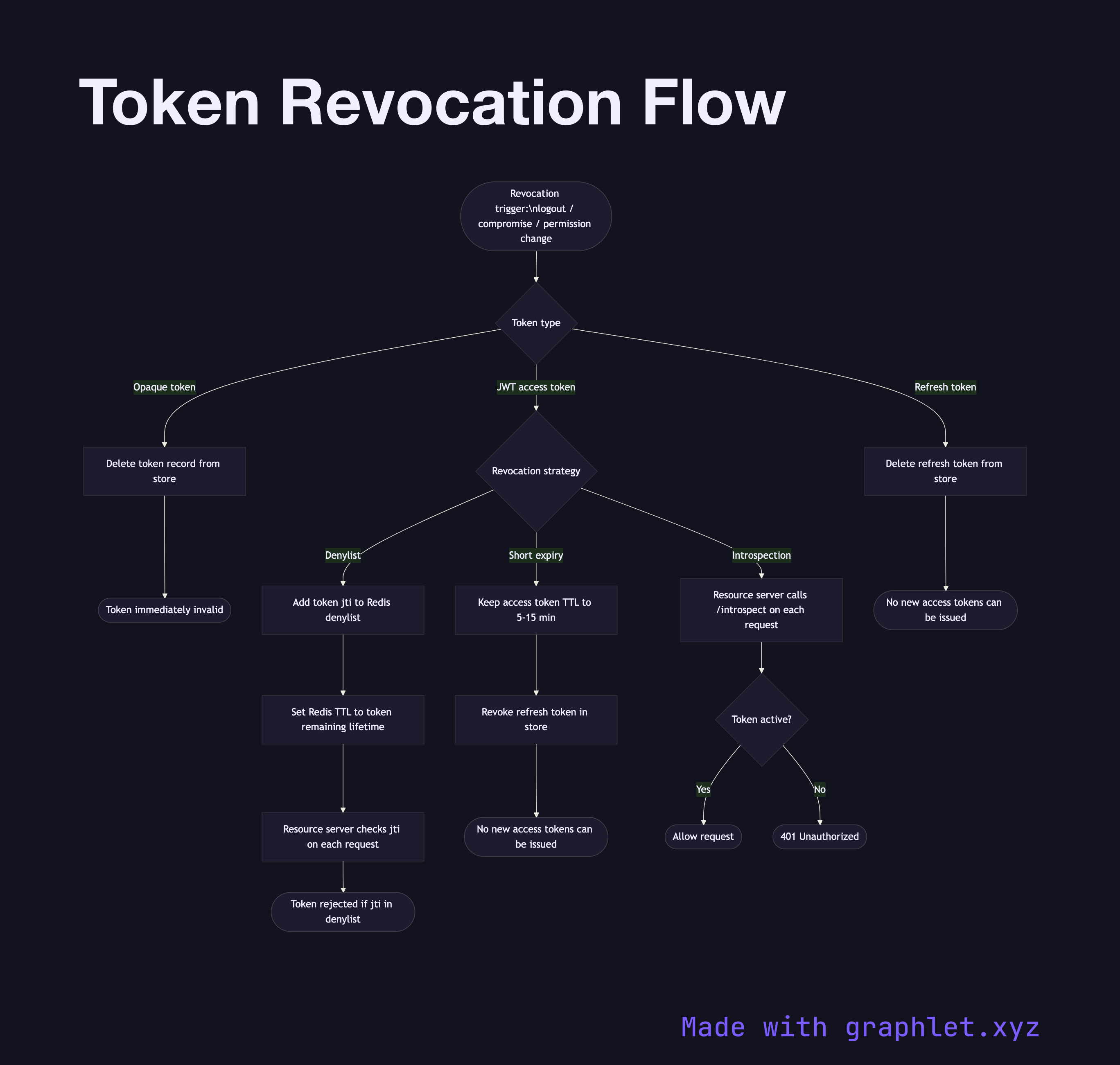
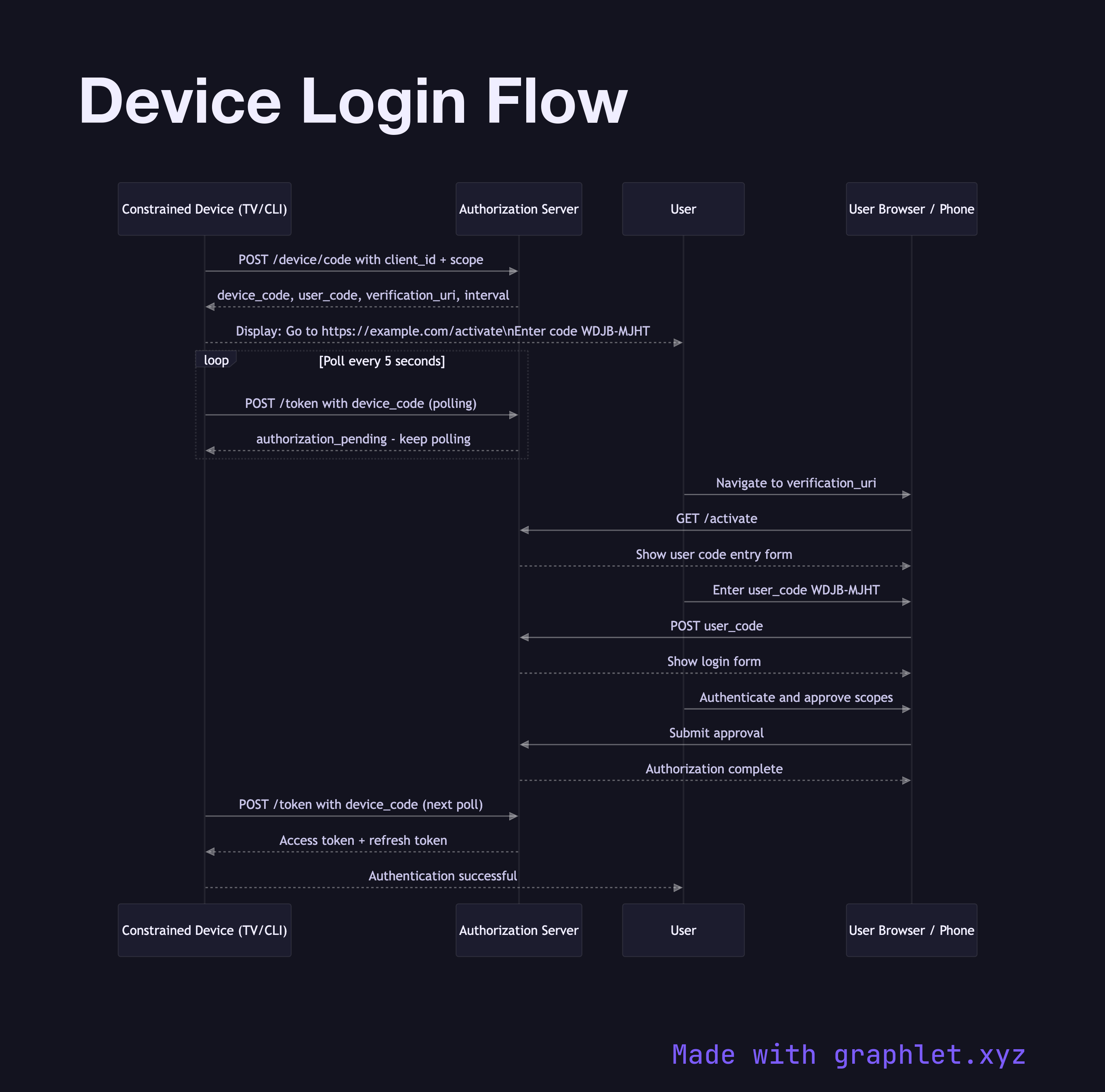
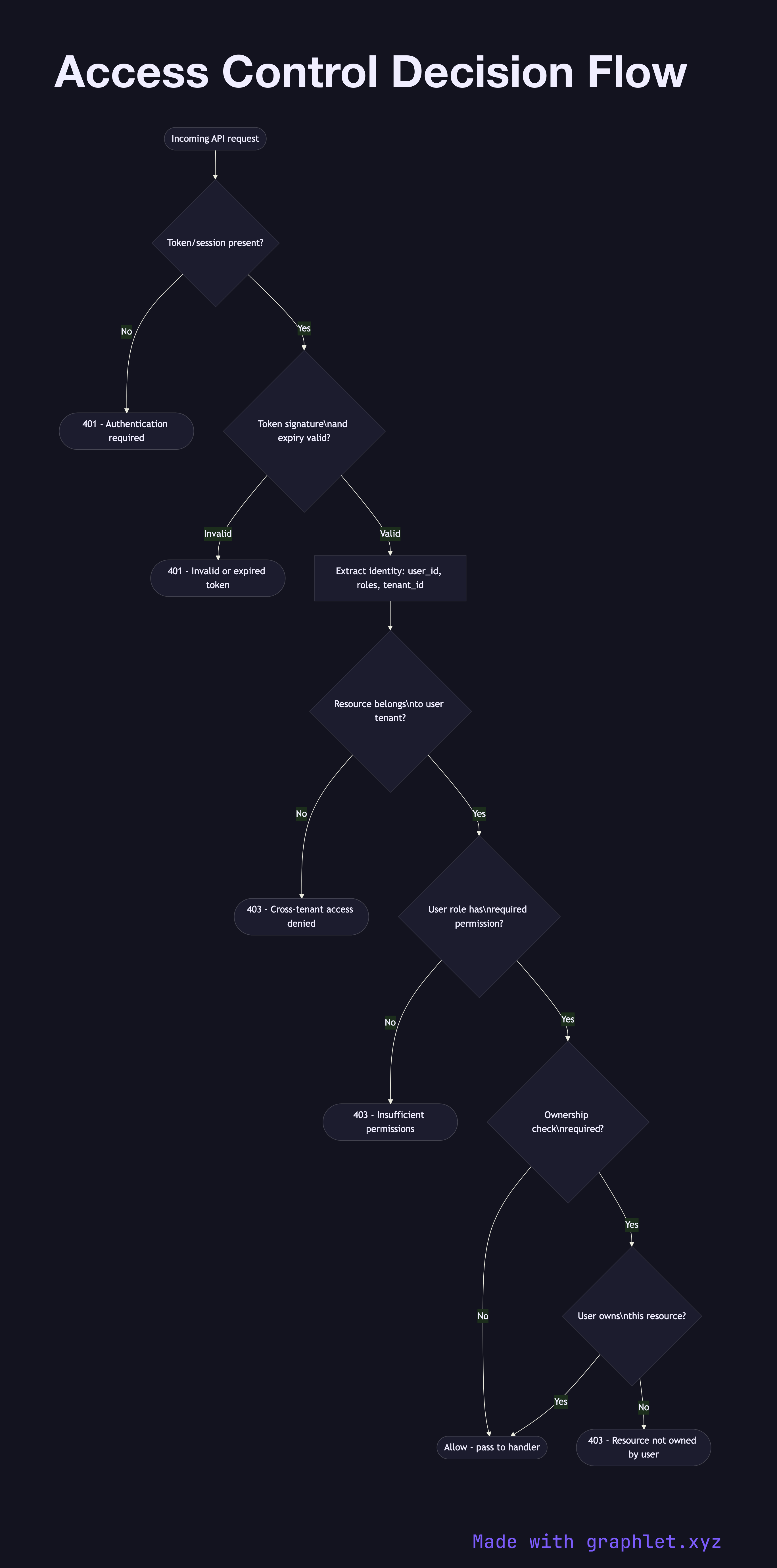
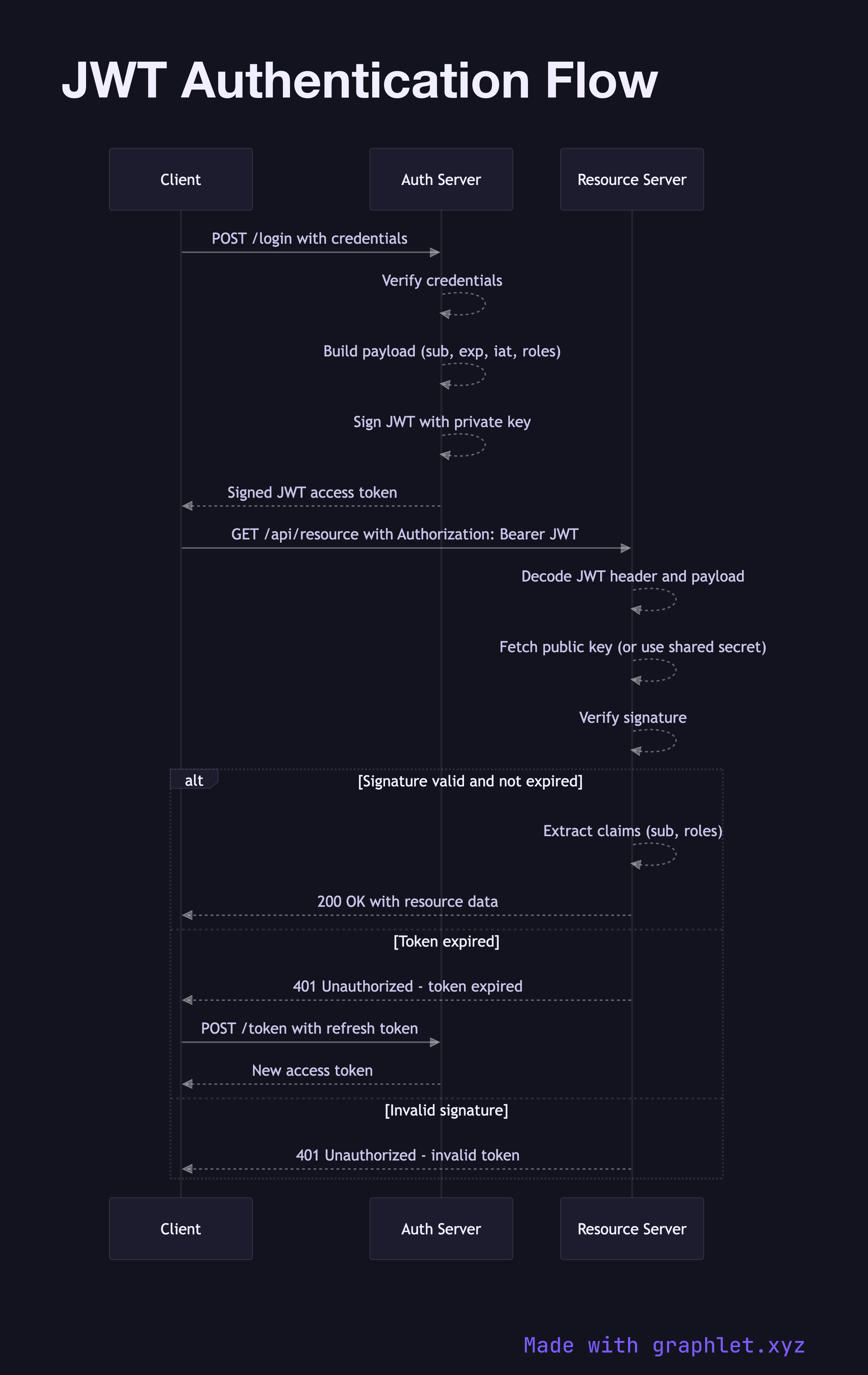
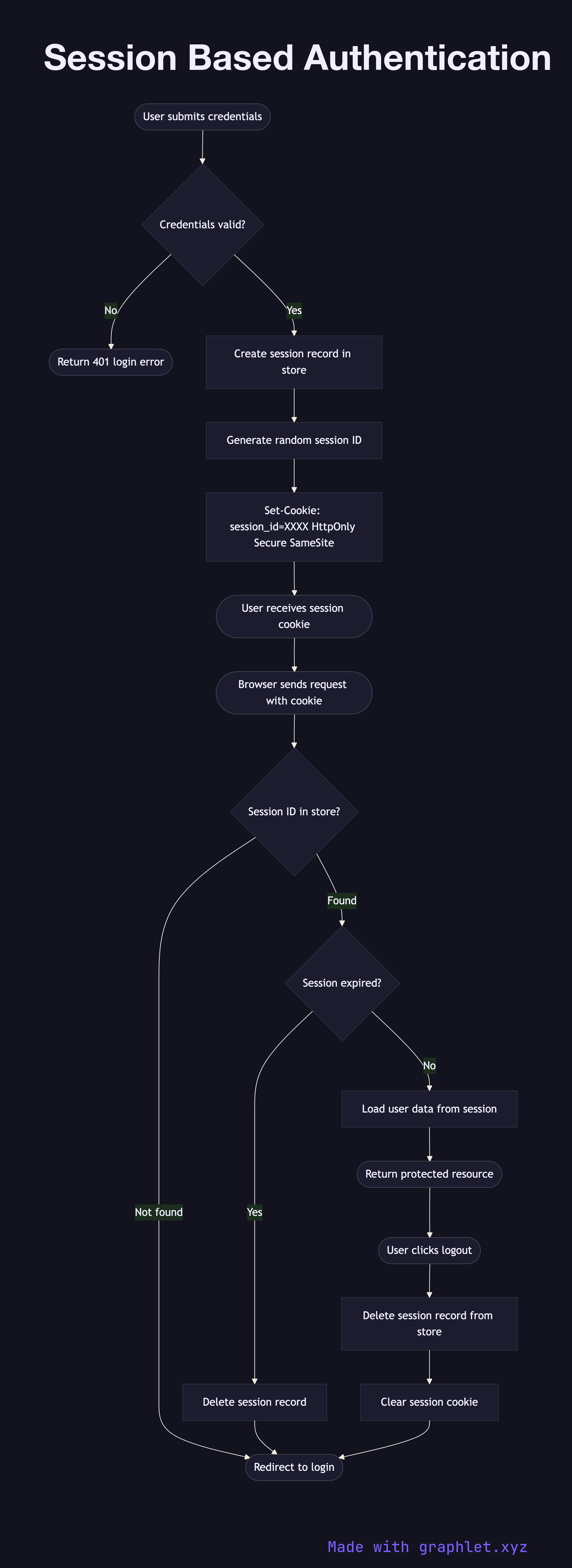
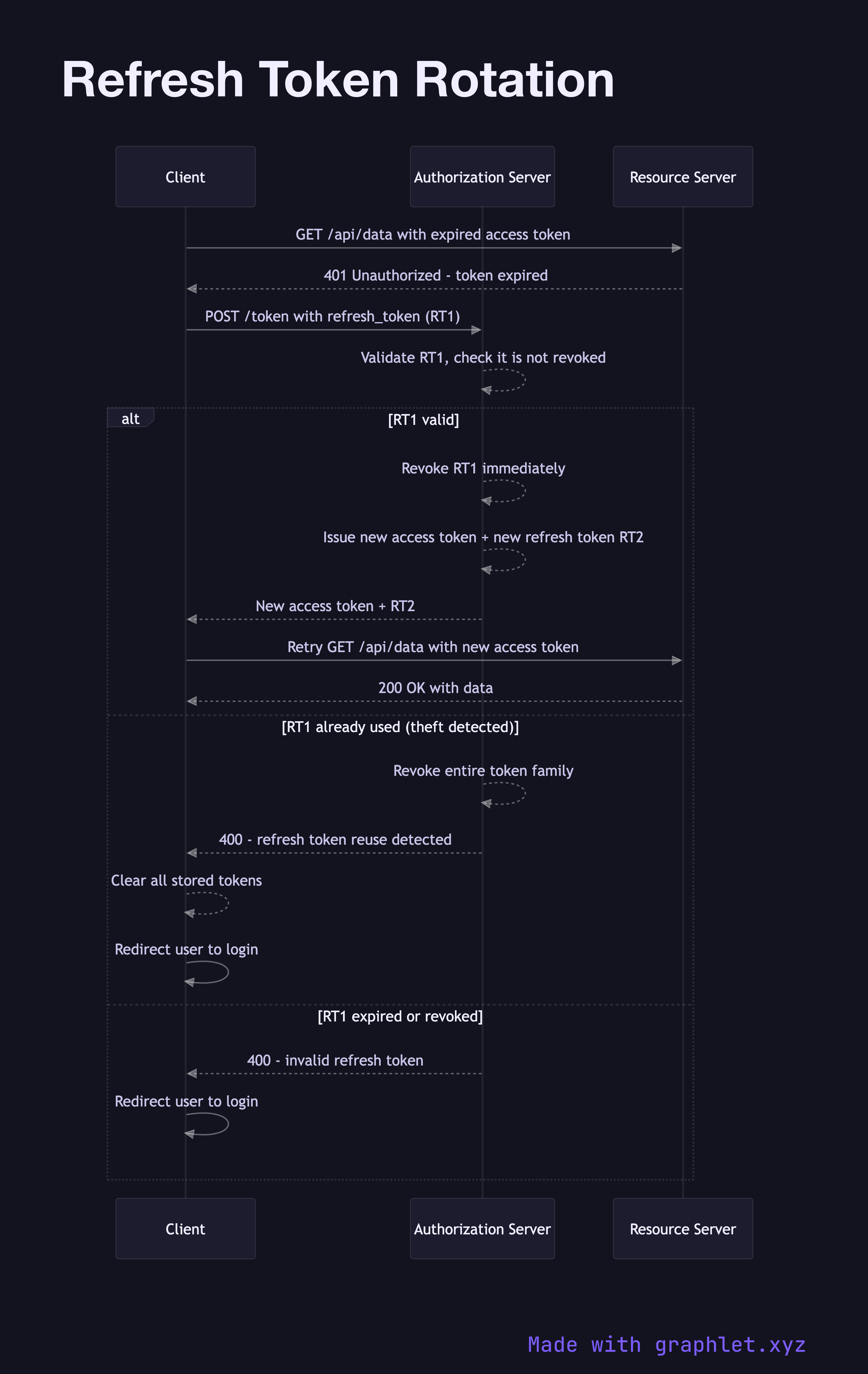
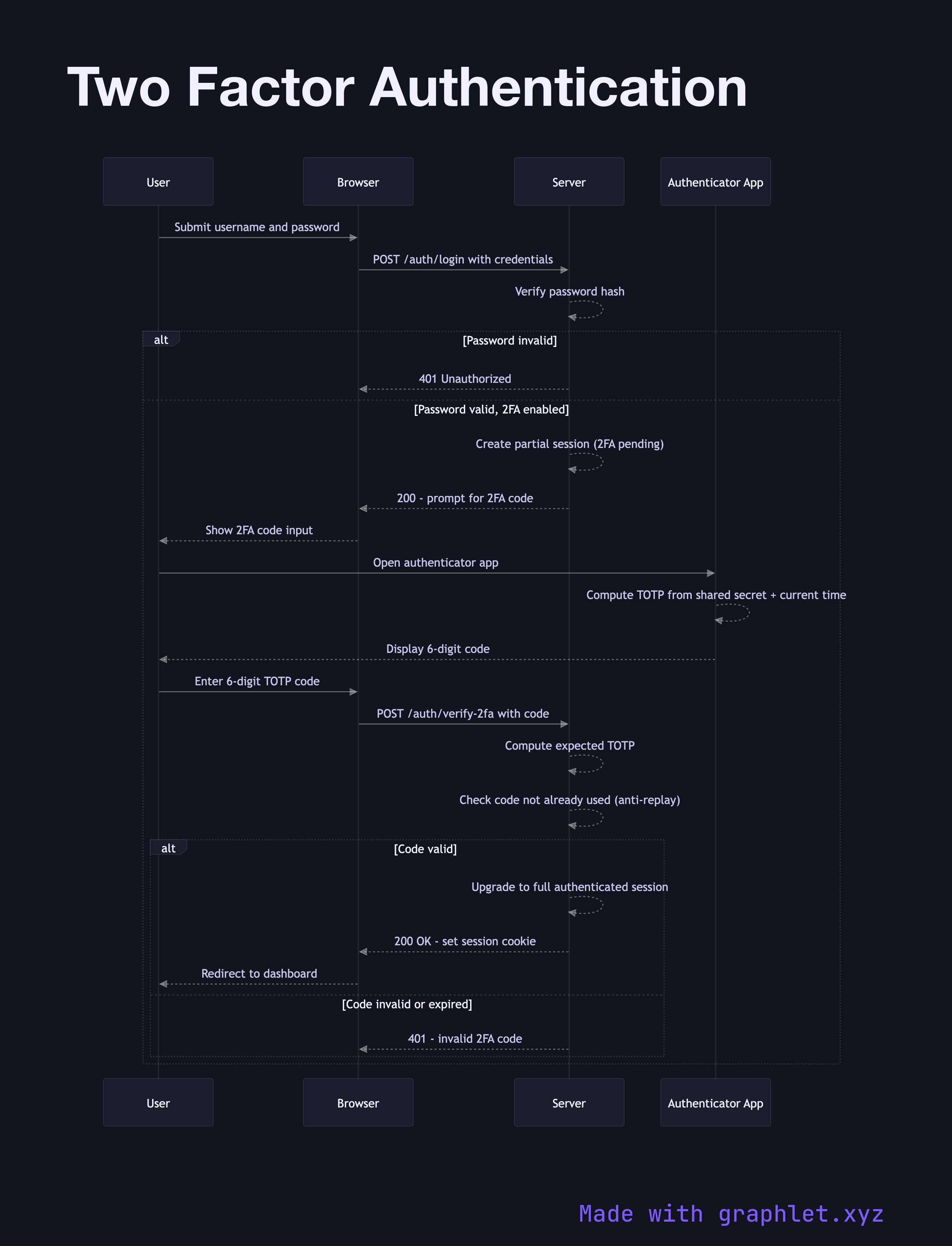
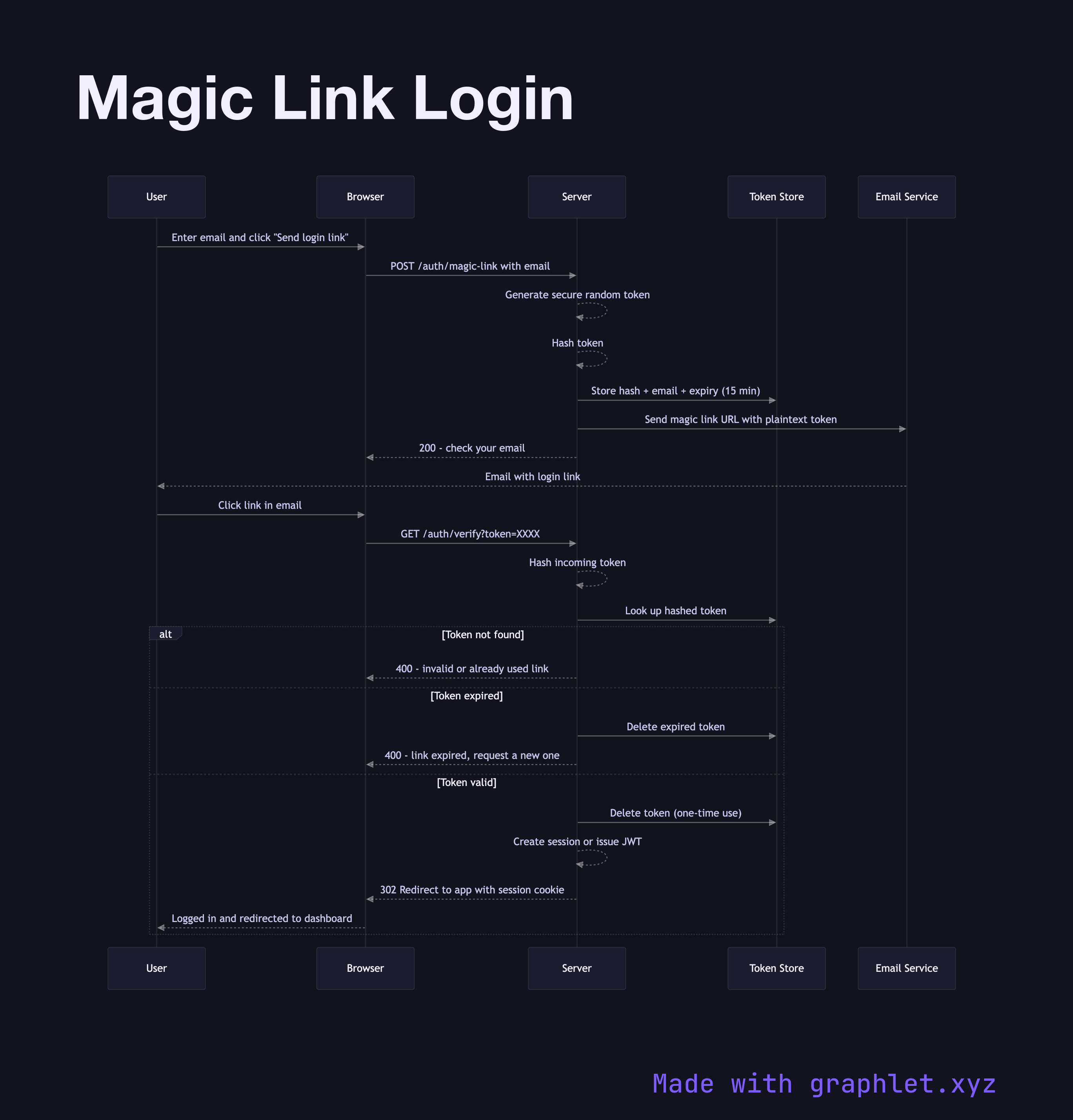
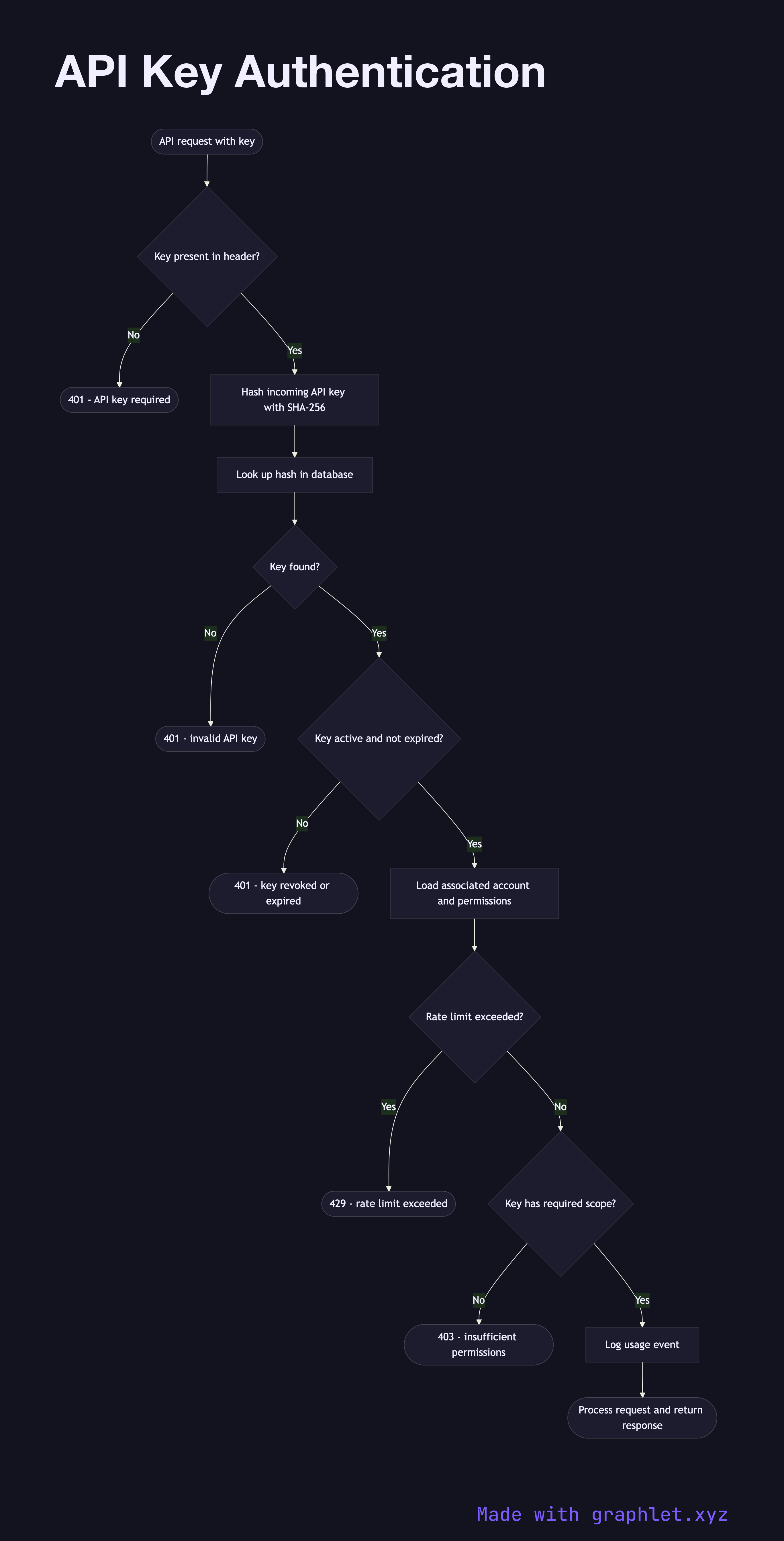
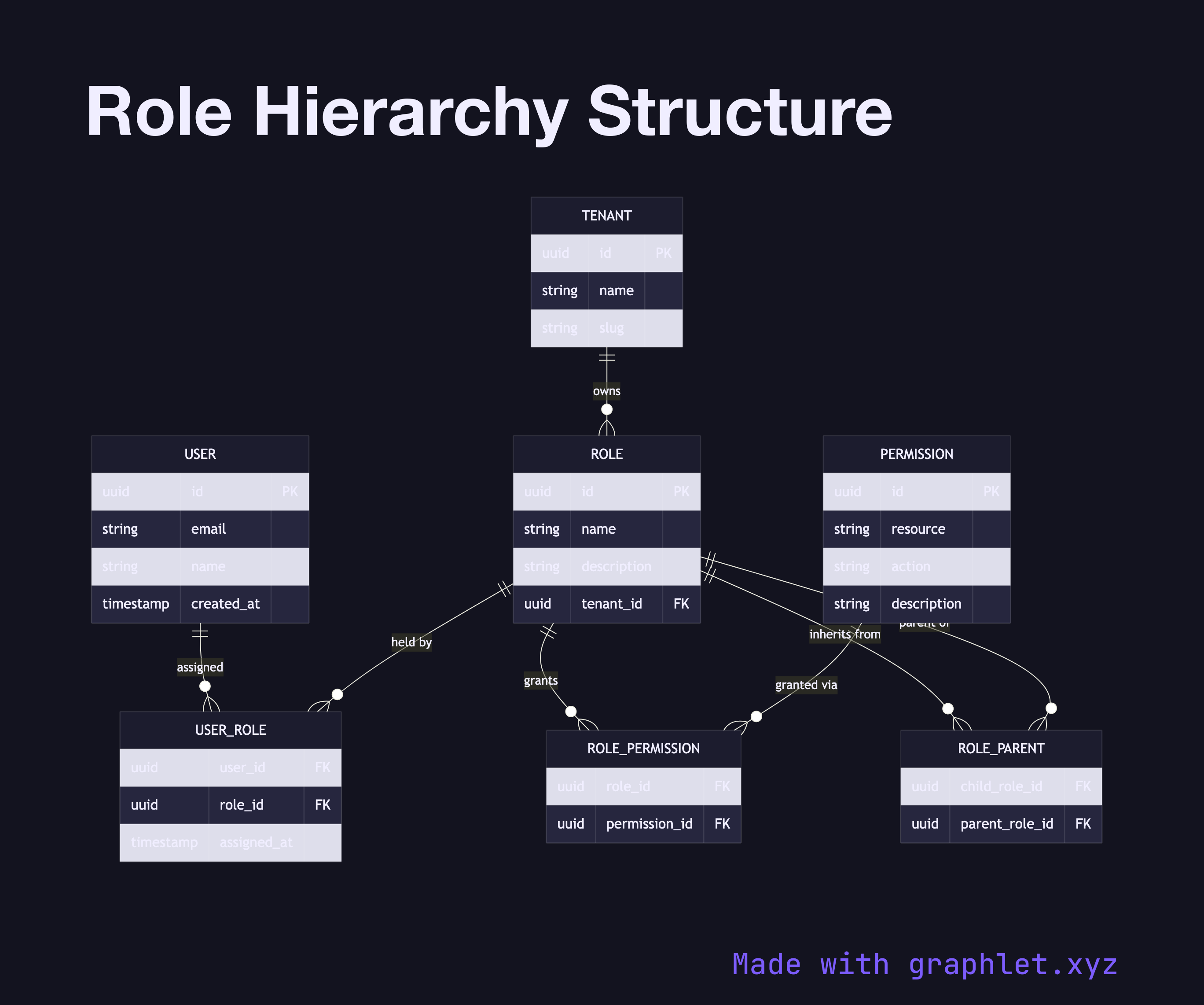
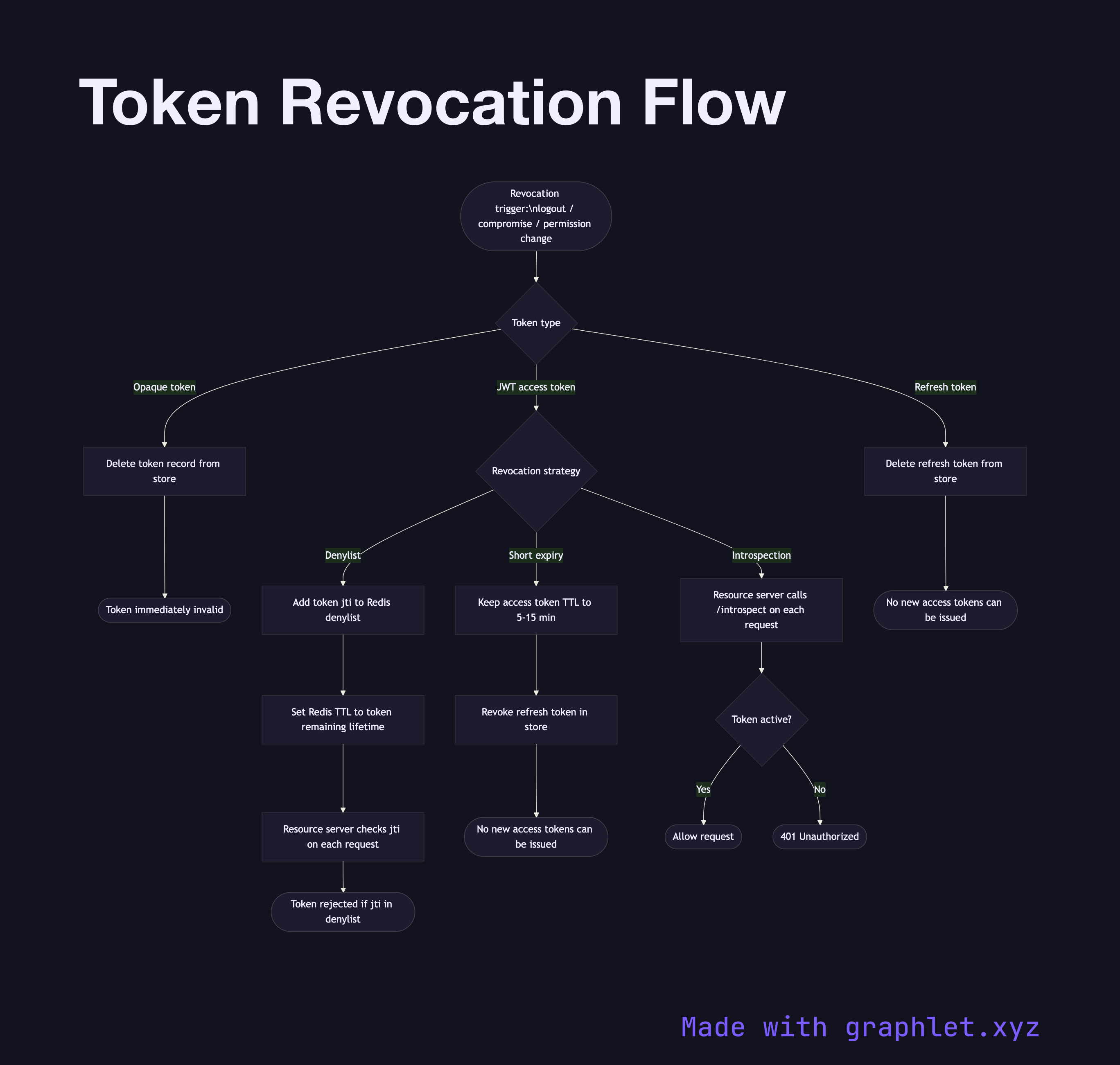
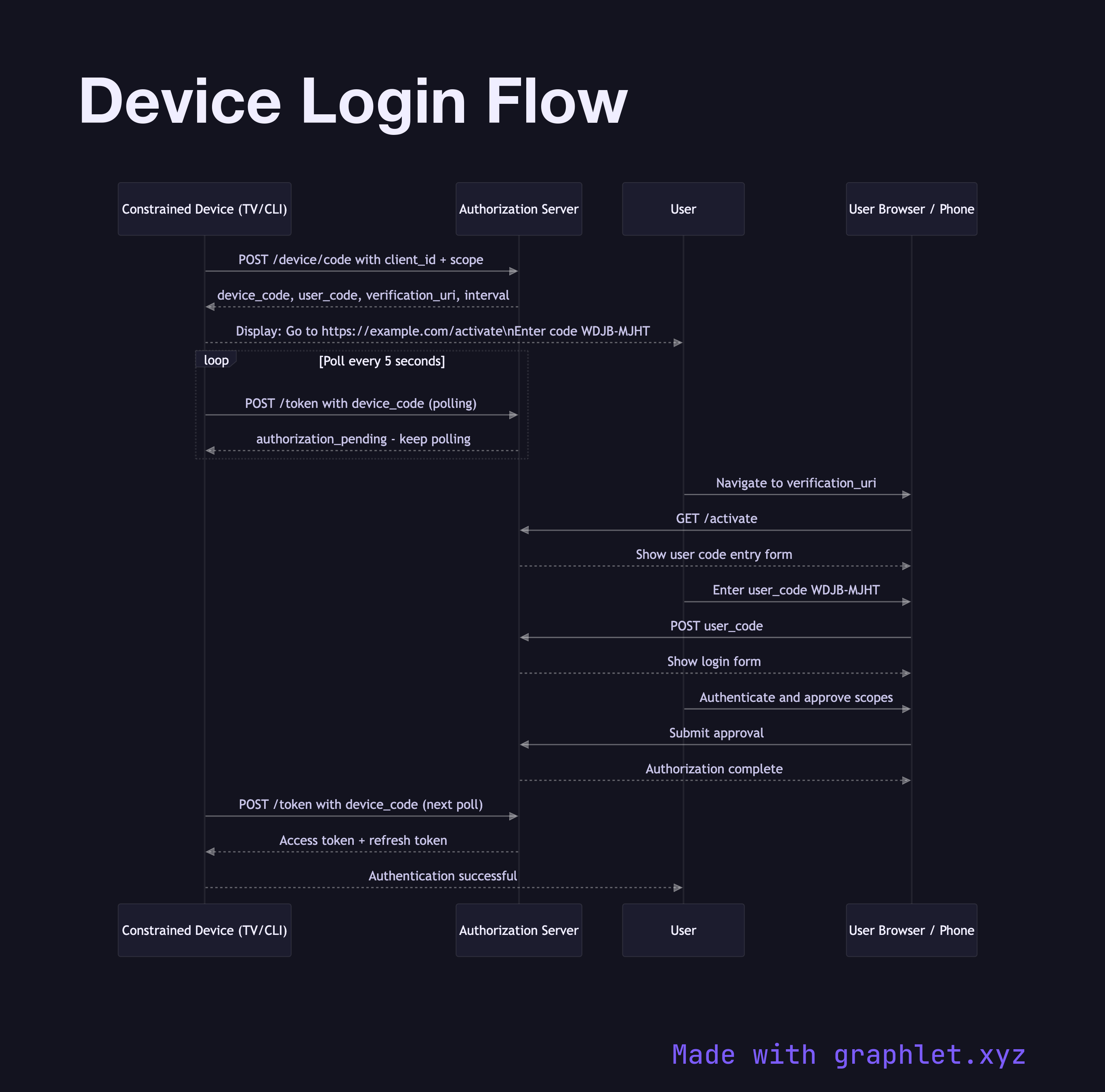
Token mechanics are examined in depth: JWT Authentication Flow shows how stateless tokens are issued and verified, and Refresh Token Rotation explains the security strategy for long-lived sessions. Access control models including RBAC Authorization Model and ABAC Authorization Model show how permissions are structured and evaluated. Usability-focused patterns like Magic Link Login, Two Factor Authentication, and Device Login Flow round out the collection. Every diagram is free to edit and export directly in Graphlet.