Token Revocation Flow
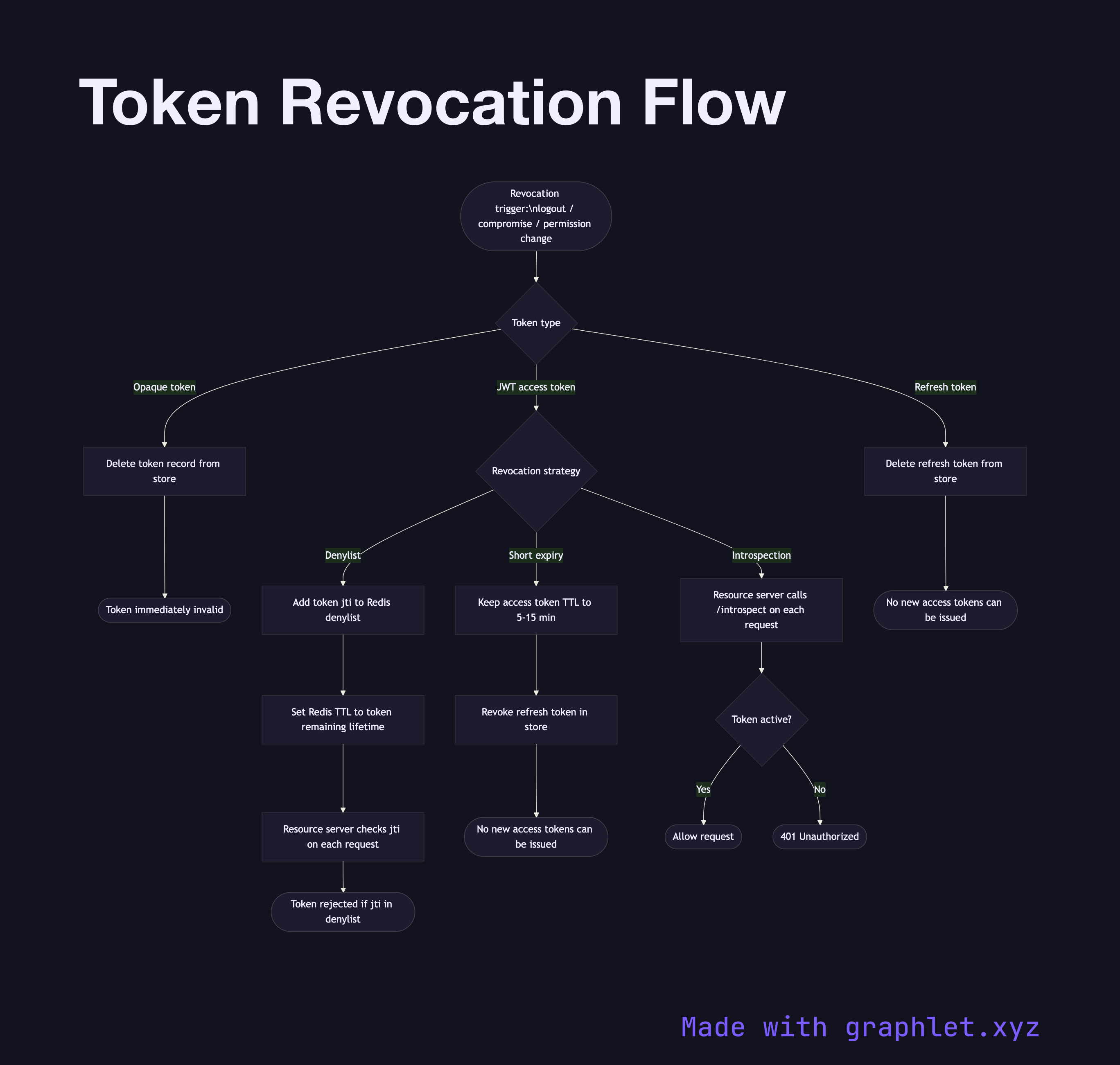
Token revocation is the process of immediately invalidating an issued token before it naturally expires. It is a critical operational capability for handling logout, account compromise, permission changes, and security incidents.
Token revocation is the process of immediately invalidating an issued token before it naturally expires. It is a critical operational capability for handling logout, account compromise, permission changes, and security incidents.
For opaque tokens (random strings validated by database lookup), revocation is straightforward: delete the record from the token store. Any subsequent request presenting that token will fail the lookup and be rejected. This is one reason session-based and opaque-token systems are easier to secure against active threats.
JWT revocation is fundamentally harder because JWTs are self-contained and stateless — the resource server validates them by checking the signature and expiry, without querying any database. A revoked JWT is still cryptographically valid until its exp timestamp passes. There are two main strategies. The first is a token denylist: when a token is revoked, its jti (JWT ID) claim is added to a denylist (typically backed by Redis with TTL set to the token's remaining lifetime). The resource server checks every incoming token's jti against the denylist. This reintroduces a centralized store lookup, partially defeating the statefulness advantage. The second strategy is short expiry: keep access token lifetimes so short (5–15 minutes) that the damage window of a compromised token is limited. Combine this with Refresh Token Rotation — when a refresh token is revoked, no new access tokens can be obtained.
A third approach uses token introspection (RFC 7662): the resource server calls the authorization server's /introspect endpoint on every request to check the token's current status. This is accurate but adds latency and load. Session Based Authentication avoids these trade-offs by design — revocation is instant and free.