Role Hierarchy Structure
A role hierarchy is the data model underlying a Role-Based Access Control system. Understanding the entity relationships helps developers design databases, API schemas, and authorization logic that scales from simple three-role systems to complex multi-tenant enterprise setups with hundreds of roles and thousands of permissions.
A role hierarchy is the data model underlying a Role-Based Access Control system. Understanding the entity relationships helps developers design databases, API schemas, and authorization logic that scales from simple three-role systems to complex multi-tenant enterprise setups with hundreds of roles and thousands of permissions.
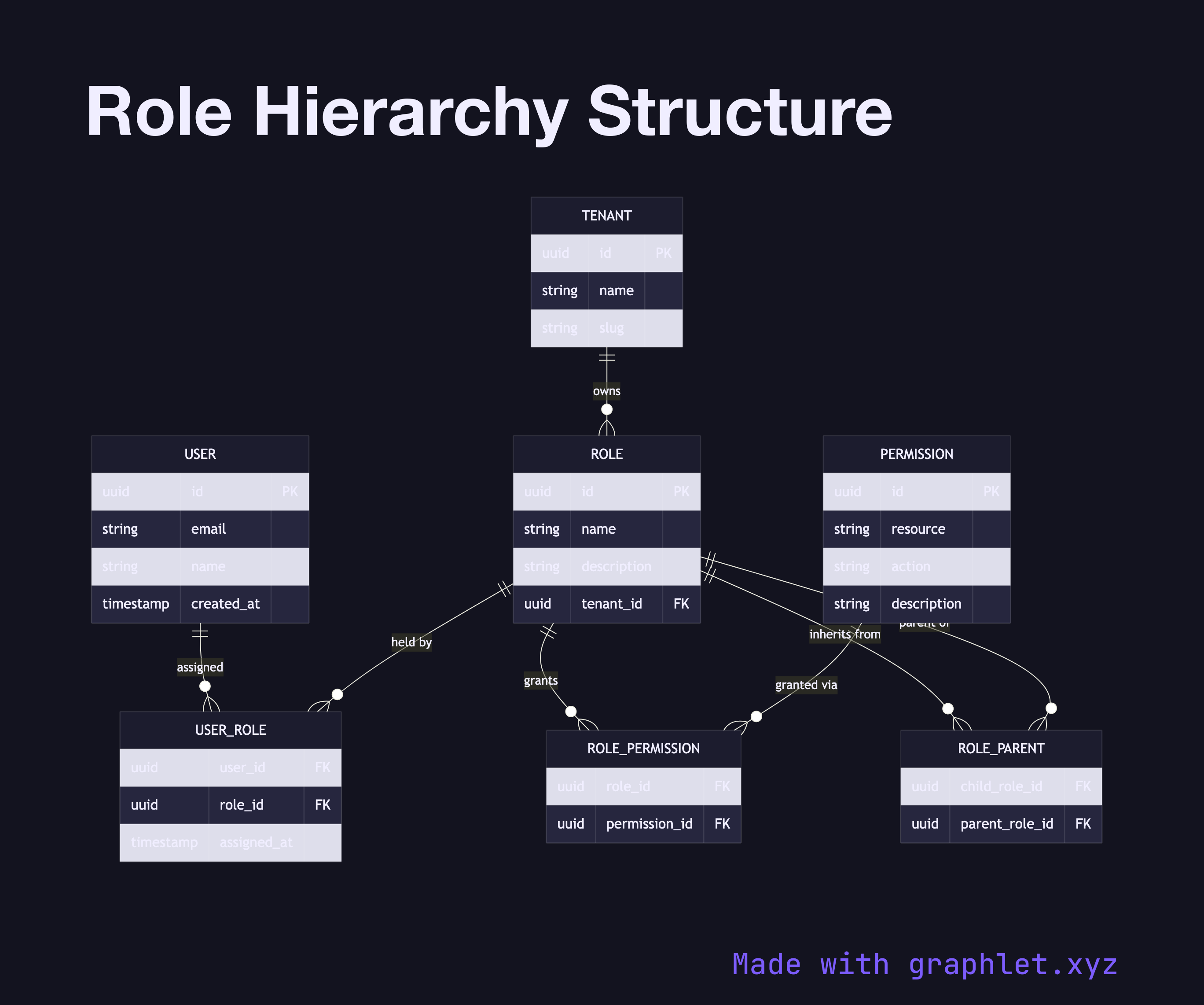
The foundational entities are User, Role, and Permission. The relationship between User and Role is many-to-many: a user can hold multiple roles (e.g., both editor and billing-viewer), and a role can be assigned to many users. This is modeled as a join table (user_roles). Similarly, Role and Permission have a many-to-many relationship modeled as role_permissions.
A permission represents a granular capability, typically expressed as a resource:action pair — invoices:read, invoices:write, admin:access. Grouping permissions into roles allows you to reason about access at a human-meaningful level.
Role hierarchies add another layer: roles can inherit from parent roles. A super-admin role might be defined as a child of admin, automatically inheriting all of admin's permissions plus having additional ones. This inheritance is modeled as a self-referential role_parents relationship on the Role entity, forming a directed acyclic graph.
In multi-tenant systems, a Tenant entity scopes everything: roles are defined per tenant, users belong to tenants, and permission checks always include the tenant context. This prevents one tenant's users from accessing another tenant's resources even if they hold the same role name. The runtime enforcement of this structure is shown in RBAC Authorization Model and Access Control Decision Flow.