IoT Device Authentication
IoT device authentication is the process by which a physical device proves its identity to a cloud platform or gateway before being permitted to publish sensor data, receive commands, or download firmware — typically using X.509 certificates and mutual TLS rather than username/password credentials.
IoT device authentication is the process by which a physical device proves its identity to a cloud platform or gateway before being permitted to publish sensor data, receive commands, or download firmware — typically using X.509 certificates and mutual TLS rather than username/password credentials.
Unlike web applications where a user can be prompted to re-authenticate, IoT devices must authenticate autonomously and continuously. This makes cryptographic identity — where the device holds a private key burned into secure storage during manufacturing — the standard approach.
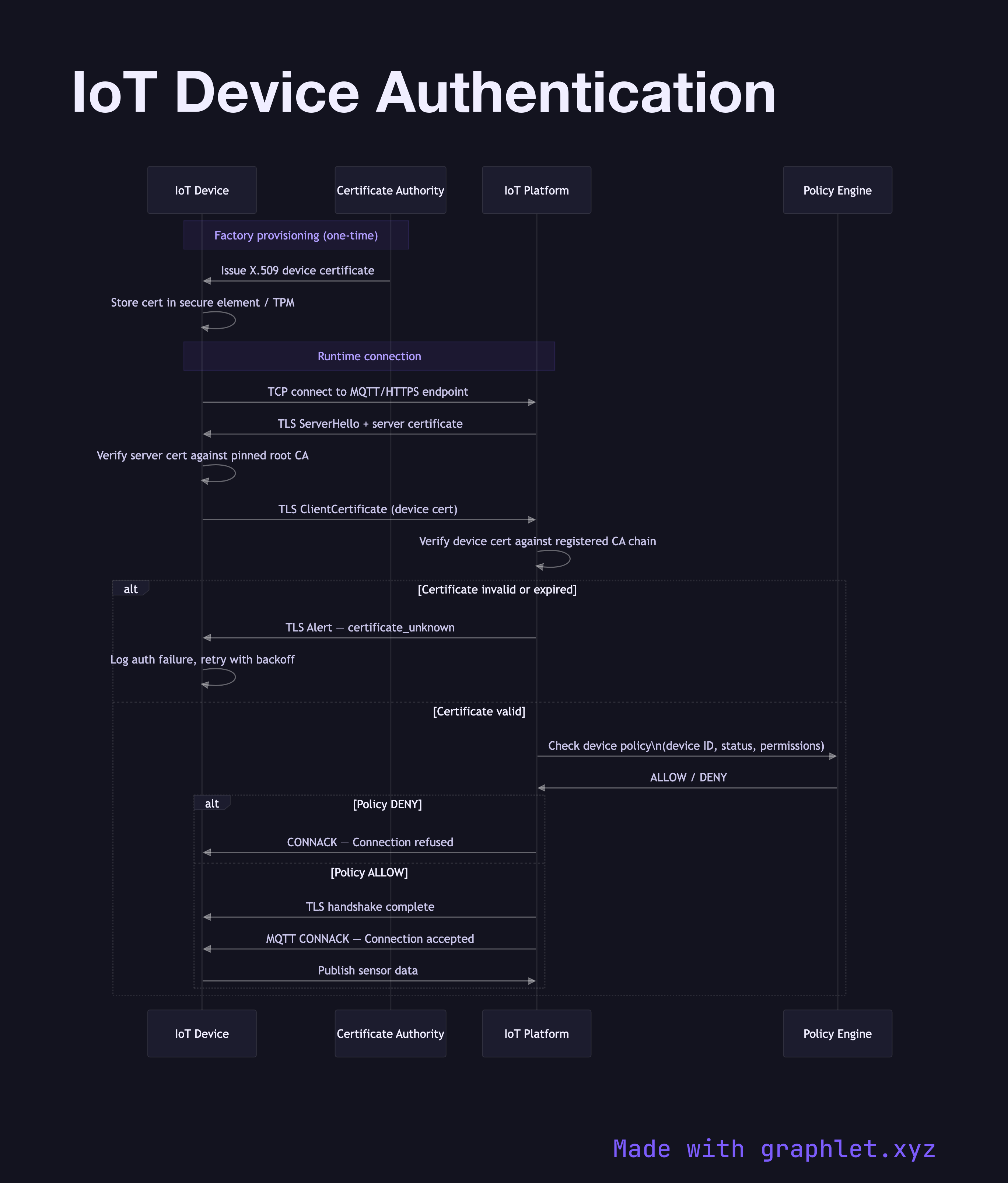
Provisioning happens at the factory or during initial onboarding: a Certificate Authority (CA) operated by the device manufacturer or the cloud platform issues a unique X.509 certificate for each device. The certificate contains the device's serial number as a Common Name and is signed by the CA's private key. The device certificate and the CA's public certificate chain are flashed into the device's secure element or trusted platform module (TPM).
At runtime, the device initiates a mutual TLS (mTLS) handshake with the IoT platform endpoint. During the TLS ClientHello and subsequent handshake, both parties present certificates. The platform verifies the device certificate against the registered CA chain. The device verifies the platform's server certificate against a pinned root CA. If either verification fails, the connection is rejected.
Once the TLS session is established, the cloud platform performs a second-layer policy check: is this specific device ID authorised to connect? Is it suspended, decommissioned, or quarantined? Only if the policy evaluation returns allow does the device receive a session token or MQTT connection acknowledgement and begin publishing data. The sequence diagram captures the full exchange — from initial TCP connect through certificate validation to first data publish. For command delivery over an established session, see IoT Command Control Flow. For the firmware update flow that depends on this authenticated channel, see IoT Firmware Update Flow.