Packet Fragmentation
IP packet fragmentation is the process by which a router or sender splits an IP packet into smaller fragments when the packet exceeds the Maximum Transmission Unit (MTU) of the outgoing link, allowing it to traverse network segments with different MTU limits.
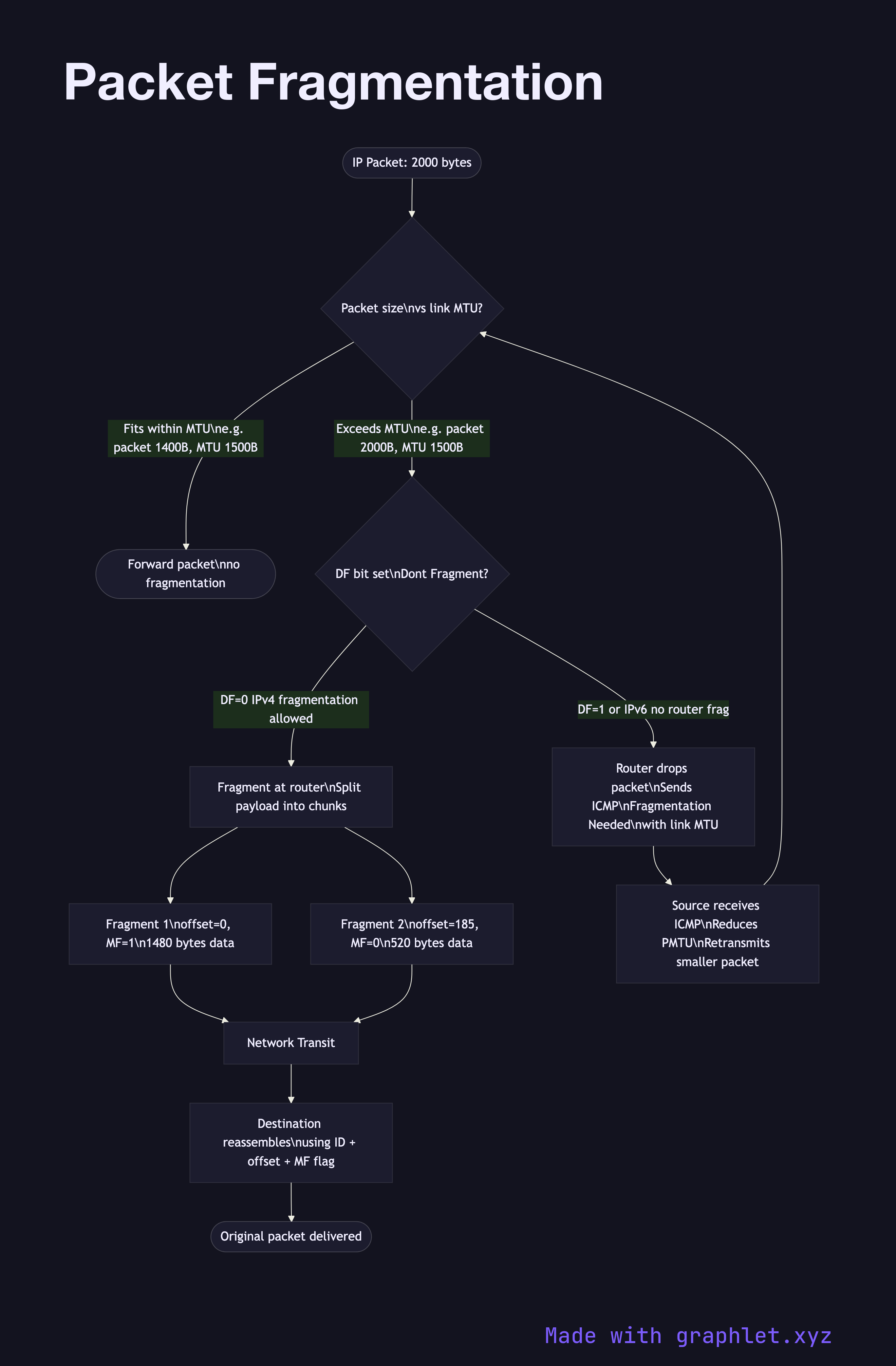
IP packet fragmentation is the process by which a router or sender splits an IP packet into smaller fragments when the packet exceeds the Maximum Transmission Unit (MTU) of the outgoing link, allowing it to traverse network segments with different MTU limits.
Every network link has an MTU — the maximum size of a single frame it can carry. Ethernet's standard MTU is 1500 bytes. VPN tunnels, PPPoE, and some WAN links have smaller effective MTUs. If a packet is larger than the link's MTU, it must be fragmented or dropped.
IPv4 Fragmentation: In IPv4, fragmentation can occur at any router along the path. The IP header contains fragment offset and "More Fragments" flag fields. The router splits the packet body into chunks, creating new IP headers for each fragment with the same identification field, appropriate offsets, and the MF flag set on all but the last fragment. Fragments are reassembled only at the destination.
IPv6 No-Router Fragmentation: IPv6 routers do not fragment packets. If a packet is too large, the router drops it and sends an ICMPv6 "Packet Too Big" message back to the source. The source is responsible for fragmenting using its own Fragment extension header. This simplifies router processing.
PMTUD (Path MTU Discovery): Rather than relying on fragmentation, modern systems use PMTUD to discover the smallest MTU along the path. IPv4 PMTUD works by sending packets with the DF (Don't Fragment) bit set. If a router can't forward the packet due to MTU, it sends an ICMP "Fragmentation Needed" message with the link's MTU. The sender reduces its packet size. IPv6 uses this approach exclusively.
TCP MSS Clamping: TCP uses the Maximum Segment Size (MSS) option during the three-way handshake to negotiate maximum segment sizes that fit within the path MTU, avoiding fragmentation proactively. VPN gateways often clamp MSS to account for tunnel overhead.
Fragmentation issues can cause mysterious connectivity problems: PMTUD works only if ICMP isn't blocked by firewalls.