Firewall Packet Filtering
A firewall is a network security device (hardware or software) that monitors and controls incoming and outgoing network traffic based on a defined set of security rules, deciding whether to allow or block each packet.
A firewall is a network security device (hardware or software) that monitors and controls incoming and outgoing network traffic based on a defined set of security rules, deciding whether to allow or block each packet.
Firewalls are the primary enforcement mechanism for network security policies. Modern firewalls operate in layers, from simple packet filters to full deep packet inspection.
Stateless Packet Filtering: The simplest mode. Each packet is evaluated independently against a ruleset (ACL) based on: source IP, destination IP, protocol (TCP/UDP/ICMP), source port, and destination port. No connection state is maintained. Fast but limited — can't distinguish response traffic from new connections.
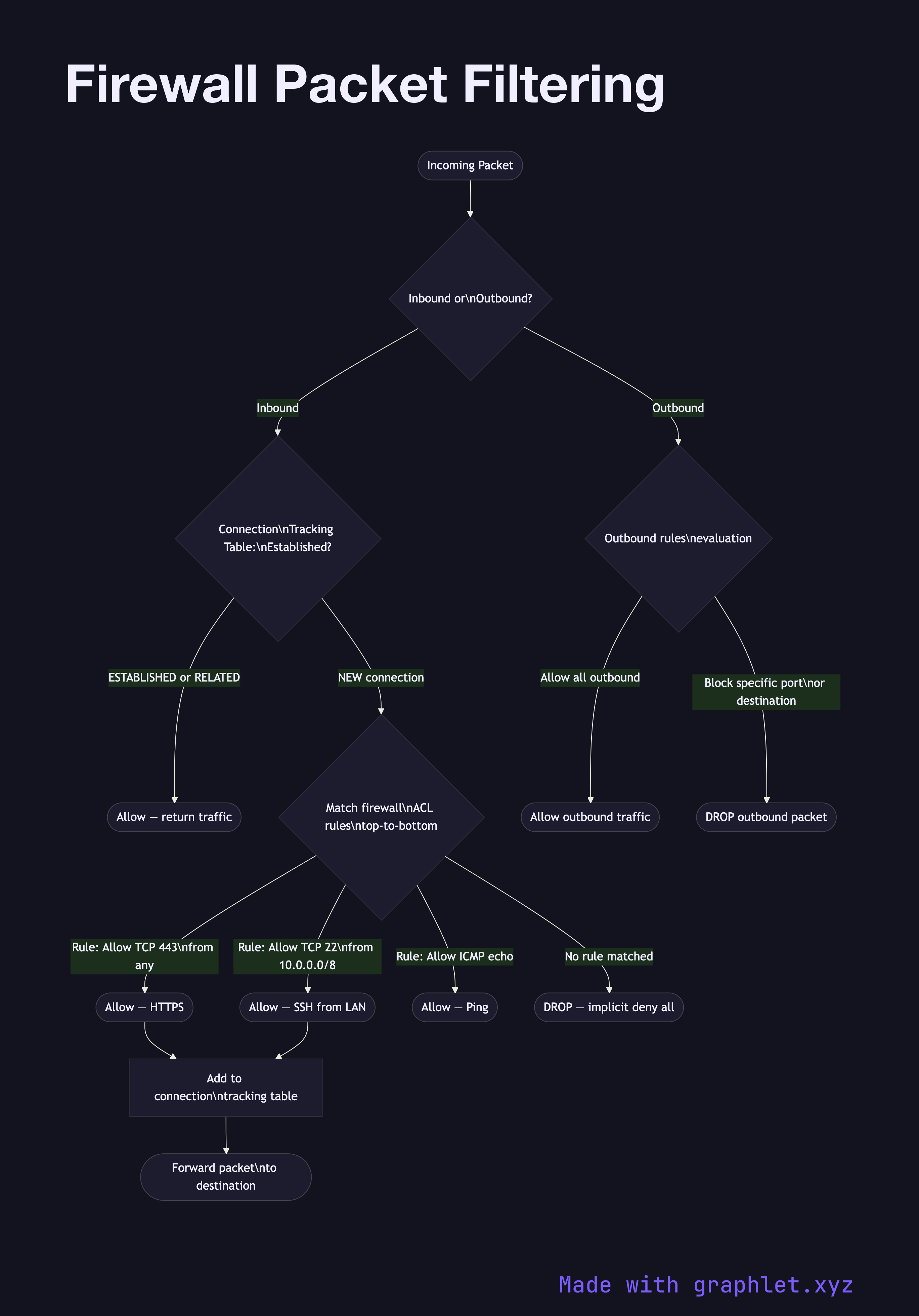
Stateful Packet Filtering: The firewall tracks the state of active connections in a connection tracking table. Packets that are part of established or related connections are automatically permitted without matching explicit inbound rules. This allows a single outbound rule to cover both the request and the reply.
Rule Evaluation: Rules are evaluated top-to-bottom, first match wins. A typical ruleset allows specific inbound ports (e.g., TCP 443, TCP 80), permits all established/related traffic, then drops everything else with an implicit deny-all rule.
Application-Layer Inspection: Next-generation firewalls (NGFW) inspect application-layer content — identifying application types, decrypting TLS (using MITM certificates), and enforcing policies at the HTTP, DNS, or protocol level.
Security Groups / Cloud Firewalls: AWS Security Groups, GCP firewall rules, and Azure NSGs are software-defined stateful firewalls applied per network interface. They use the same stateful filtering model: explicitly allow inbound ports; all outbound is permitted by default; return traffic is automatically allowed.