QUIC Handshake
QUIC is a modern transport protocol developed by Google and standardized in RFC 9000, designed to eliminate the layered handshake latency of TCP+TLS by combining connection establishment and cryptographic negotiation into a single 1-RTT exchange over UDP.
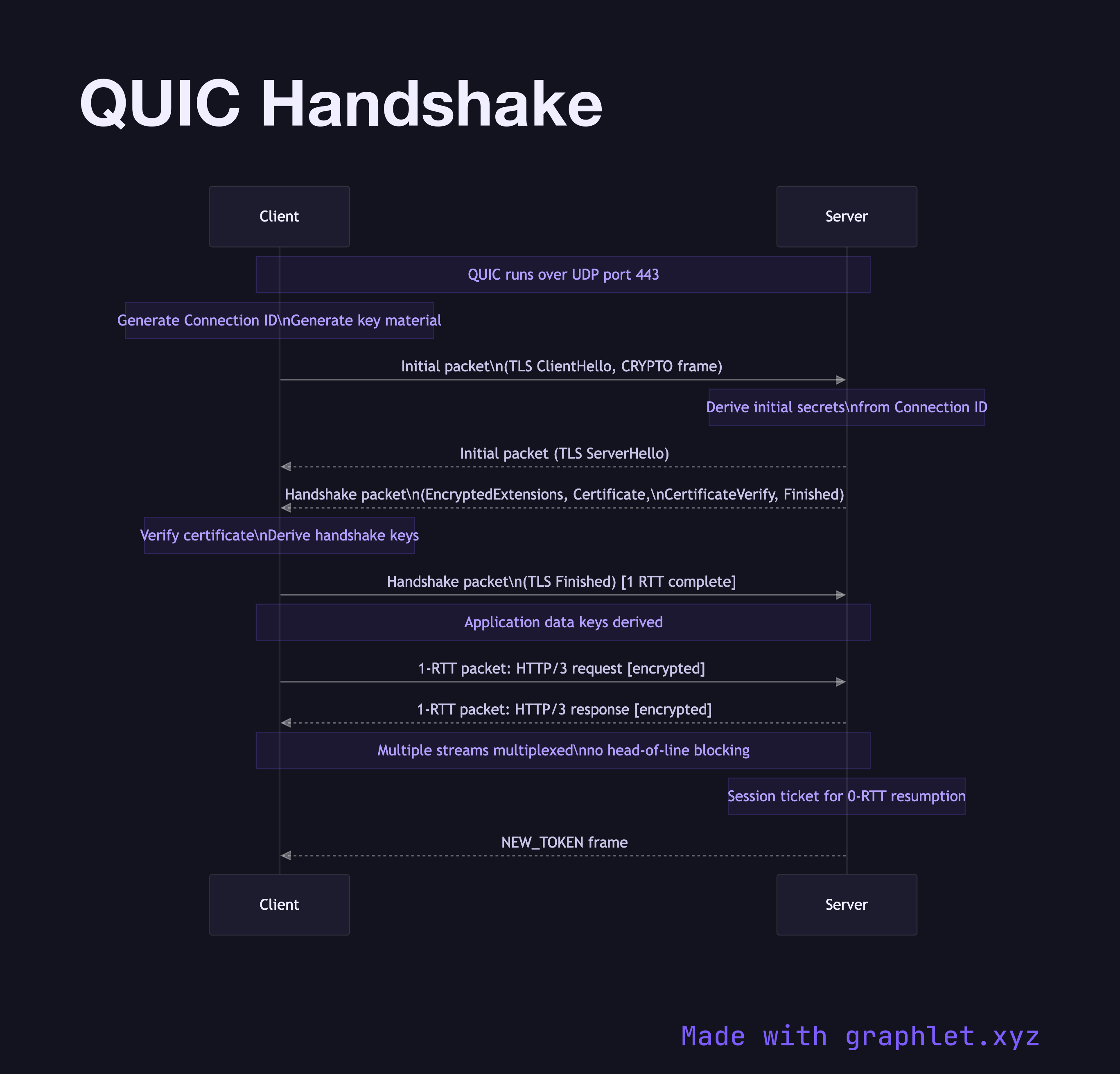
QUIC is a modern transport protocol developed by Google and standardized in RFC 9000, designed to eliminate the layered handshake latency of TCP+TLS by combining connection establishment and cryptographic negotiation into a single 1-RTT exchange over UDP.
The fundamental problem QUIC solves is handshake latency stacking. A traditional HTTPS connection requires: 1 RTT for TCP handshake + 1 RTT for TLS 1.3 handshake = 2 RTTs before the first byte of application data can be sent. QUIC collapses this to 1 RTT for a new connection and 0 RTTs for session resumption (0-RTT data).
Why UDP?: QUIC runs over UDP (port 443 by default) rather than TCP to bypass kernel TCP implementations that can't be updated. This lets QUIC evolve faster and deploy improvements via application updates rather than OS upgrades. The protocol implements its own reliability, ordering, and congestion control.
Initial Packet: The client sends a QUIC Initial packet containing a TLS ClientHello. QUIC wraps TLS 1.3 messages directly in its packet format. The Initial packet uses well-known encryption derived from the connection ID (providing minimal protection against off-path attackers).
Server Response: The server responds with its own QUIC packets containing the TLS ServerHello, EncryptedExtensions, Certificate, CertificateVerify, and Finished — all in a single flight. The server also sends HANDSHAKE level packets with further data.
Handshake Complete: After the client verifies the certificate and sends its Finished, both sides can immediately exchange application data. QUIC streams are multiplexed within the connection with no head-of-line blocking between streams (unlike TCP, where one lost packet stalls all streams). This is the foundation of HTTP/3.