TLS Handshake
The TLS (Transport Layer Security) handshake is the cryptographic negotiation protocol that establishes a secure, authenticated, and encrypted channel between two parties before any application data is exchanged.
The TLS (Transport Layer Security) handshake is the cryptographic negotiation protocol that establishes a secure, authenticated, and encrypted channel between two parties before any application data is exchanged.
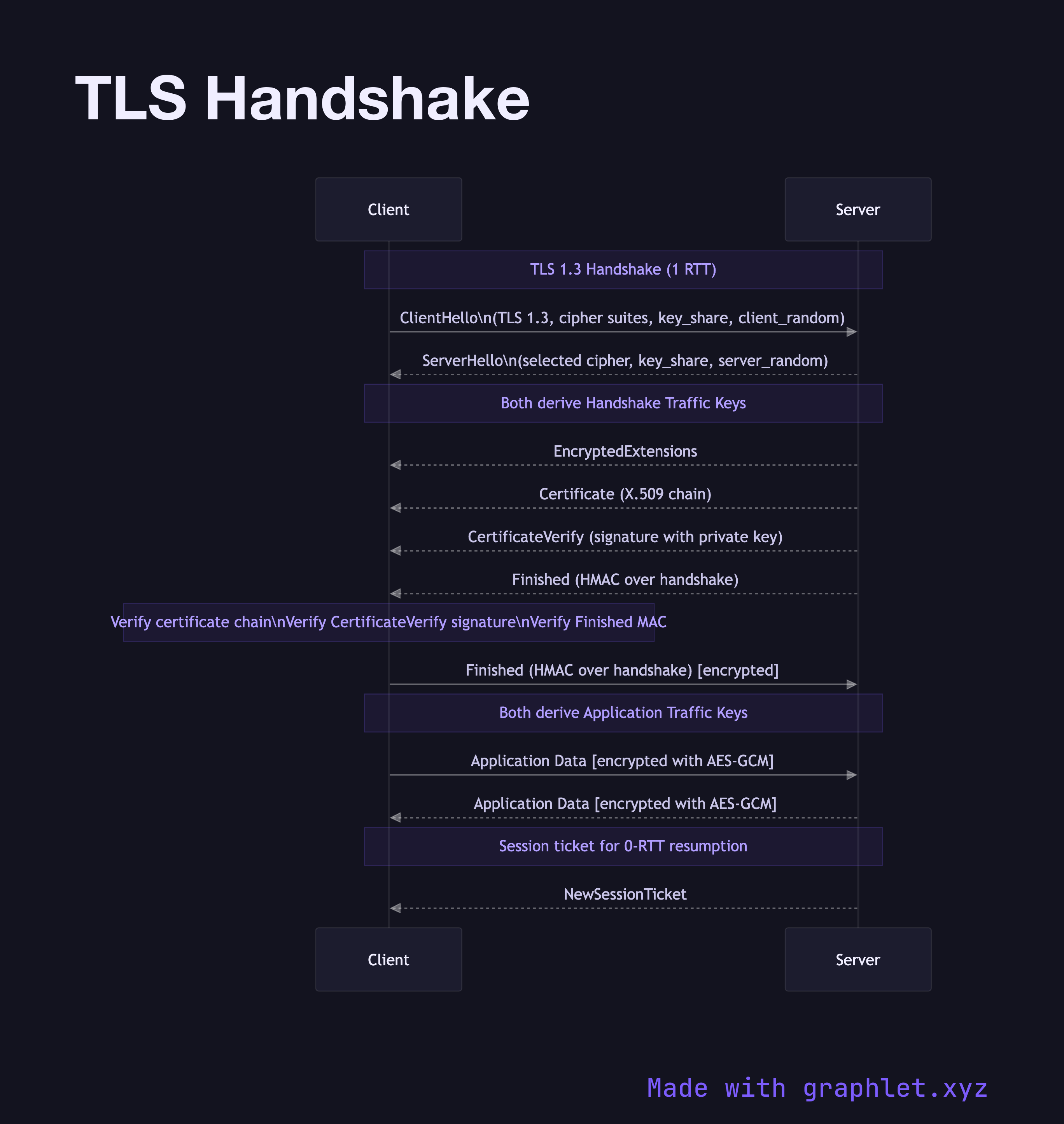
TLS 1.3 (RFC 8446, 2018) significantly simplified and accelerated the handshake compared to TLS 1.2, reducing it from 2 RTTs to 1 RTT for new connections and enabling 0-RTT resumption for returning clients (with replay-attack caveats).
ClientHello: The client initiates the handshake by advertising its supported TLS version (1.3), a list of cipher suites (e.g., TLS_AES_256_GCM_SHA384), and a key share for the expected key agreement algorithm (typically X25519). A random nonce (client_random) is included for key derivation.
ServerHello + Certificate: The server selects the highest mutually supported TLS version and a cipher suite. In TLS 1.3, the server also sends its key share in the same flight, allowing both sides to immediately derive the handshake traffic keys. The server sends its X.509 certificate chain, a CertificateVerify message (a signature proving it holds the certificate's private key), and a Finished MAC.
Client Validation + Finished: The client verifies the certificate chain against trusted root CAs (see TLS Certificate Validation), checks the CertificateVerify signature, and sends its own Finished message. Both sides now derive identical application traffic keys from the shared secret.
Application Data: All subsequent data is encrypted with symmetric keys (AES-GCM or ChaCha20-Poly1305). The asymmetric operations in the handshake are computationally expensive but happen only once per connection.
TLS is layered under both HTTPS and, in modified form, QUIC — the transport behind HTTP/3. The TCP Three-Way Handshake must complete before TLS can begin for TCP-based connections.