HTTPS Handshake
The HTTPS handshake is the full connection establishment sequence for a secure web request, combining TCP connection setup, TLS negotiation, and the first encrypted HTTP exchange into a single observable flow.
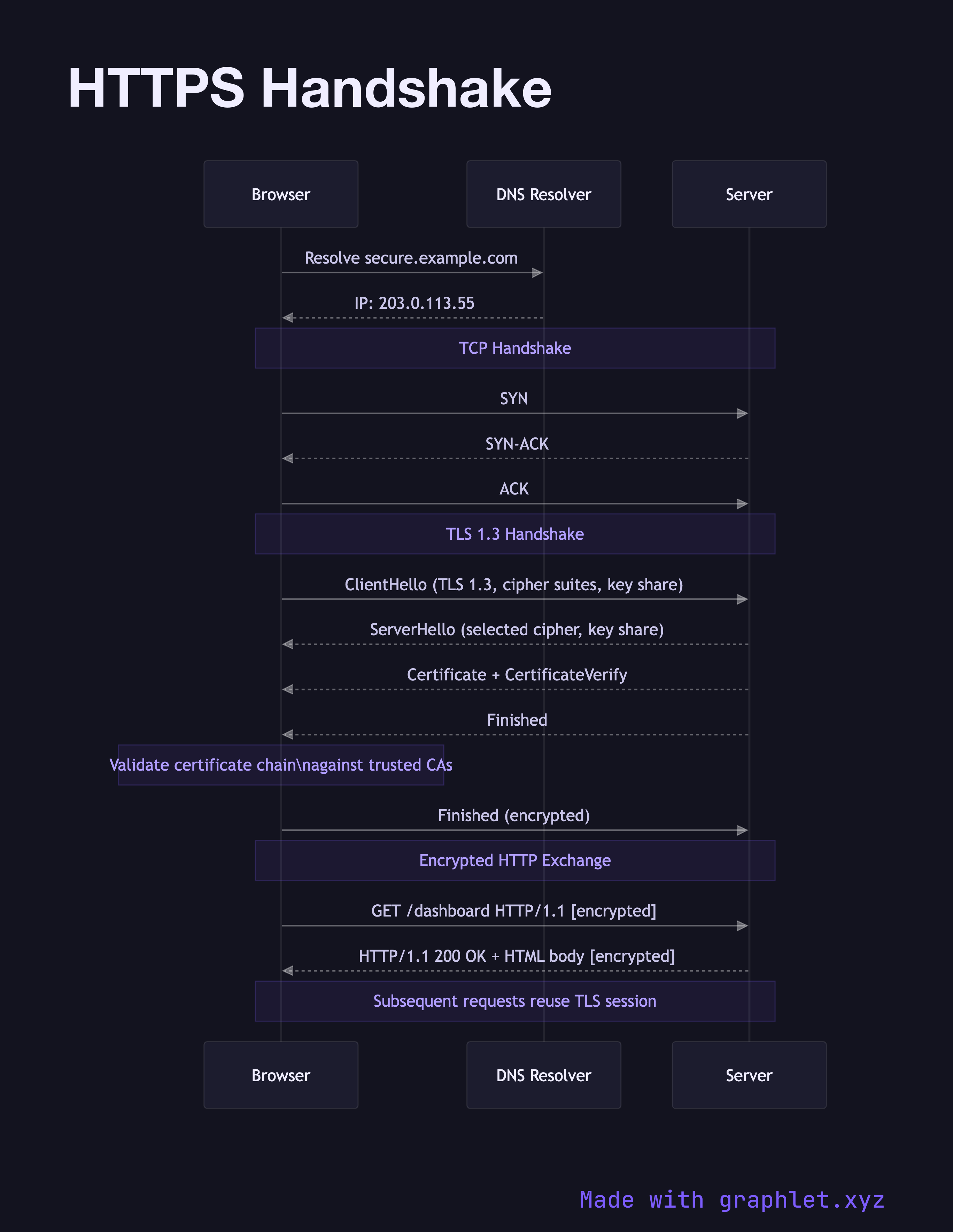
The HTTPS handshake is the full connection establishment sequence for a secure web request, combining TCP connection setup, TLS negotiation, and the first encrypted HTTP exchange into a single observable flow.
HTTPS is HTTP layered on top of TLS (Transport Layer Security). Understanding the complete handshake helps developers reason about latency, certificate errors, and the security properties of each step.
DNS Resolution happens first — the browser resolves the hostname to an IP via the DNS system. This can be a significant source of latency on first visit; CDNs and DNS prefetching () help here.
TCP Connection: A TCP socket is opened with the standard three-way handshake (SYN/SYN-ACK/ACK). This establishes a reliable, ordered byte stream between client and server.
TLS Negotiation (see also TLS Handshake for the deep-dive) begins immediately after TCP is established. The client sends a ClientHello advertising supported cipher suites and TLS versions. The server responds with ServerHello selecting a cipher suite and sends its X.509 certificate. The client validates the certificate against trusted CAs (see TLS Certificate Validation), then performs key exchange. Both sides derive symmetric session keys and confirm with Finished messages.
Encrypted HTTP begins once the TLS handshake completes. All HTTP request and response data — headers, body, cookies, and even the URL path — is encrypted at this point. An observer on the network can see the destination IP and SNI hostname from the TLS handshake, but nothing about the specific request content.
HTTP Strict Transport Security (HSTS) allows servers to instruct browsers to always use HTTPS for a domain, preventing protocol downgrade attacks. With TLS 1.3, the full handshake (TCP + TLS) completes in 2 RTTs for a new connection and 1 RTT for session resumption.