API Request Signing
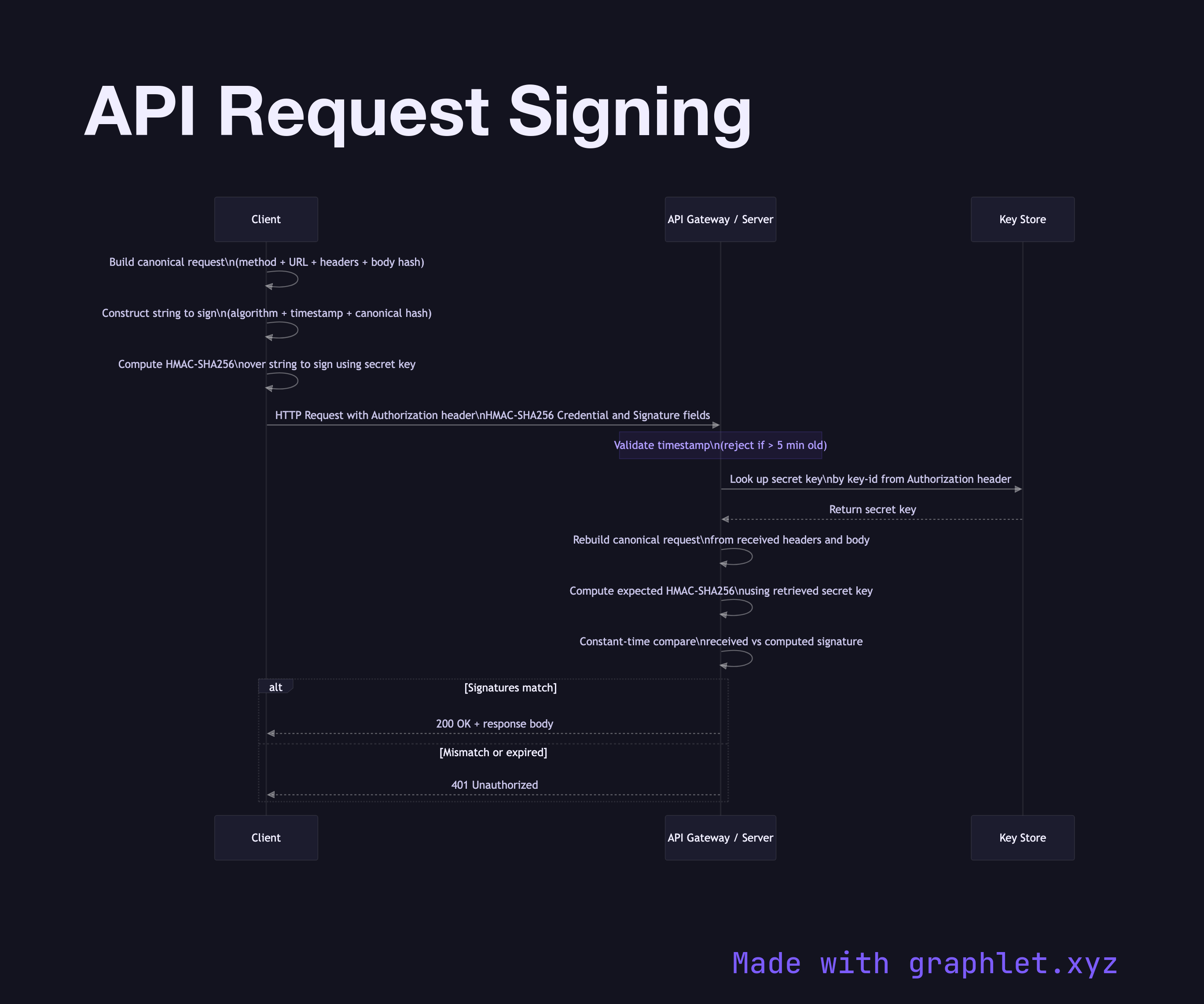
API request signing is a security technique where the client includes a cryptographic signature over the request's components — method, URL, headers, and body — so the server can verify the request's authenticity and integrity and reject replayed or tampered requests.
API request signing is a security technique where the client includes a cryptographic signature over the request's components — method, URL, headers, and body — so the server can verify the request's authenticity and integrity and reject replayed or tampered requests.
The most well-known implementation is AWS Signature Version 4 (SigV4), used by all AWS services. Similar schemes are used by Azure, Google Cloud, and many payment processors. The core principle is always the same: the client constructs a canonical representation of the request, signs it with a secret key (typically via HMAC-SHA256), and includes the signature in the Authorization header.
The signing process involves several steps. First, the client canonicalizes the request: normalizing the URL path, sorting query parameters, lowercasing and sorting header names, and hashing the request body. This produces a deterministic string representation regardless of how the HTTP client orders headers. Second, the client constructs a string to sign that includes the algorithm name, timestamp, and the hash of the canonical request. Third, the client computes an HMAC over this string using its secret key (possibly after a key derivation step as in SigV4).
The server repeats the same canonicalization and signing steps using the client's known secret key, then compares its computed signature to the one in the request. Because the signature covers the timestamp, the server enforces a replay window — typically 5–15 minutes — rejecting requests whose timestamp is too old. This prevents replay attacks where an attacker captures a valid signed request and re-submits it.
Request signing provides stronger security than bearer tokens alone because a stolen signed request only works for a short window, and the signature covers the exact request contents — an attacker cannot modify the payload without invalidating the signature. See HMAC Signing Process for the underlying signature mechanism and Secure API Gateway for the broader API security architecture.