Token Based Authentication
Token-based authentication is a stateless authentication mechanism where the server issues a signed token to an authenticated client, and the client presents that token on every subsequent request — eliminating the need for a server-side session store.
Token-based authentication is a stateless authentication mechanism where the server issues a signed token to an authenticated client, and the client presents that token on every subsequent request — eliminating the need for a server-side session store.
The dominant token format is JWT (JSON Web Token), which encodes a JSON payload (claims like user ID, roles, expiry) and a cryptographic signature in a compact base64-encoded string. The server signs the token with either a symmetric secret (HS256) or an asymmetric key pair (RS256, ES256). Any service with the corresponding key can verify the signature without querying a central session store — this is the key scalability advantage.
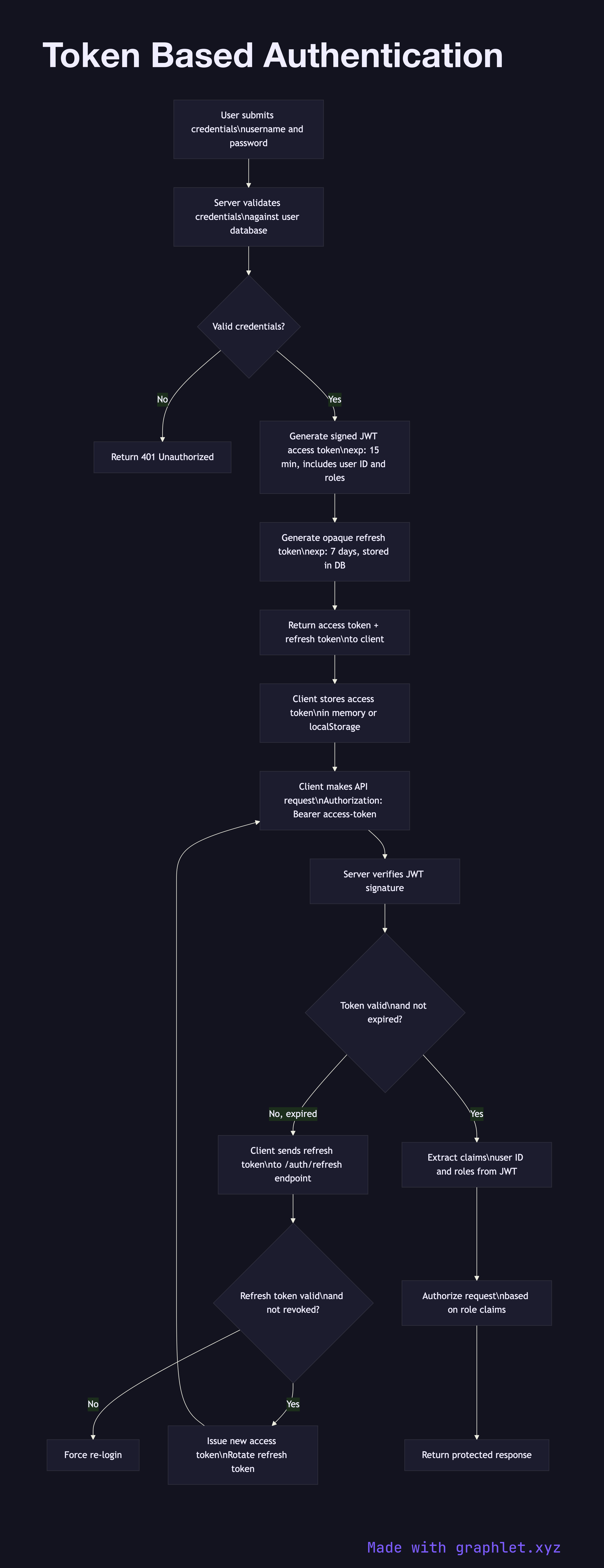
The authentication flow starts with login: the client sends credentials, the server validates them, generates a signed JWT with a short expiry (typically 15 minutes to 1 hour for access tokens), and returns it. The client stores the access token — in memory for SPAs (safest, lost on page reload), or in localStorage/sessionStorage (accessible to JS, XSS risk). The client includes the token in the Authorization: Bearer header on every API request.
A refresh token (long-lived, opaque, stored server-side) is issued alongside the access token. When the access token expires, the client presents the refresh token to a /refresh endpoint to obtain a new access token without re-authenticating. Refresh tokens should be rotated on each use and invalidated on logout.
The server validates each request by verifying the JWT signature, checking the exp claim, and optionally checking a token blocklist for revoked tokens. Unlike sessions, JWTs cannot be invalidated server-side without a blocklist — this is the primary tradeoff. See Secure Session Storage for the session-based alternative, and JWT Authentication Flow for JWT-specific details.