Secure API Gateway
A secure API gateway is a centralized entry point that enforces security policies — authentication, authorization, rate limiting, request validation, and threat detection — before requests reach backend services.
A secure API gateway is a centralized entry point that enforces security policies — authentication, authorization, rate limiting, request validation, and threat detection — before requests reach backend services.
Placing security logic in the gateway centralizes enforcement and keeps backend services focused on business logic. Every request hitting any backend service has already been authenticated and authorized at the gateway, reducing the risk of internal service misconfigurations exposing sensitive data.
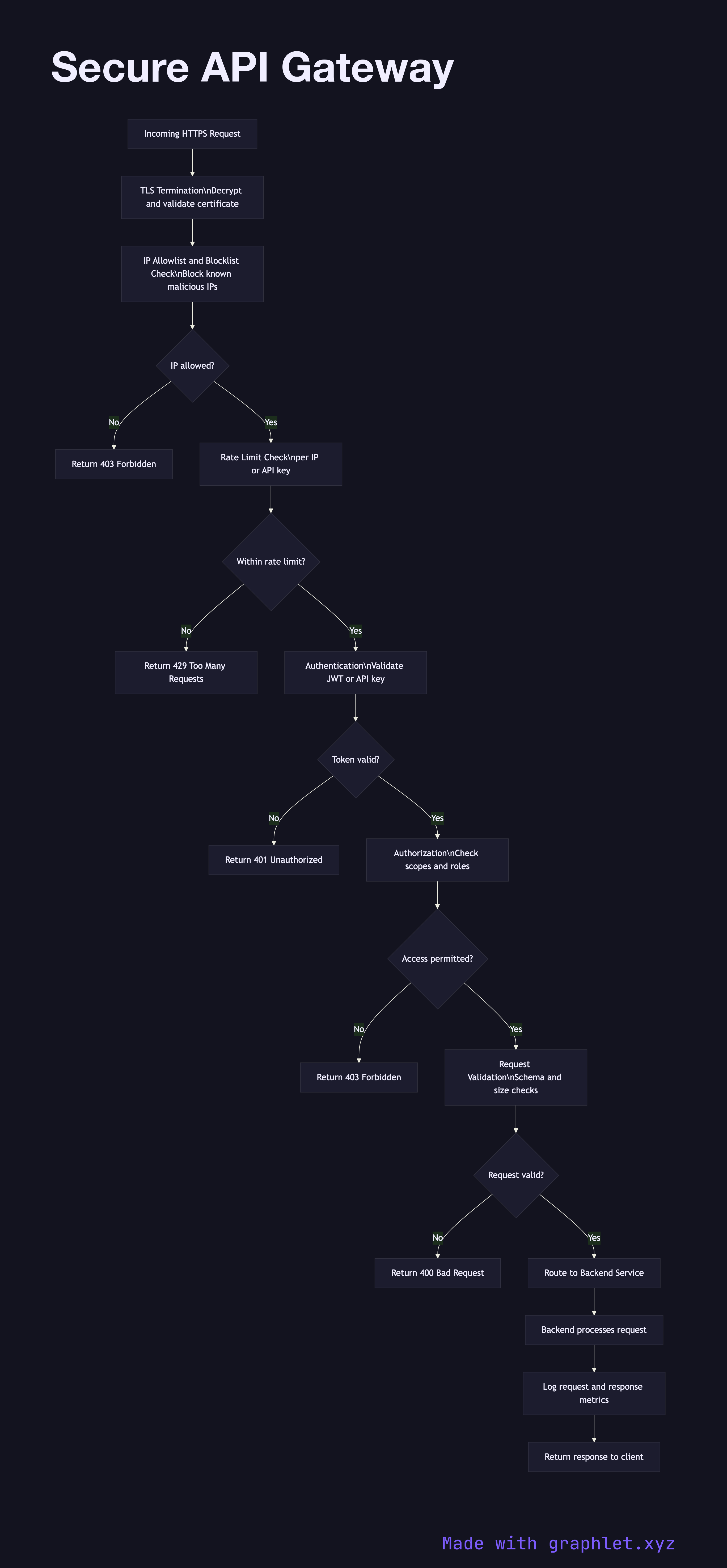
The gateway processes requests through a sequential pipeline. TLS termination is the first step — all external traffic must be HTTPS. Some gateways re-encrypt traffic to the backend (end-to-end TLS); others use trusted internal network for backend communication. Authentication comes next: the gateway validates the token (JWT signature verification, OAuth2 introspection, or API key lookup) and rejects unauthenticated requests immediately.
Rate limiting protects backend services from abuse and DDoS. Limits are applied per client IP, per API key, or per user, with different thresholds for different endpoints. Request validation checks that payloads conform to expected schemas, rejecting malformed or oversized requests before they reach application code. IP filtering blocks known malicious IP ranges and applies geographic restrictions if required.
After security checks, the gateway performs routing — mapping the inbound request to the correct backend service and version. It may also perform request transformation (header injection, protocol translation) and collect metrics and logs for observability. Responses from the backend are optionally transformed and returned to the client.
Common implementations include AWS API Gateway, Kong, Envoy, Nginx with auth modules, and Traefik. See Firewall Rule Processing for lower-level packet filtering, and API Request Signing for request-level authentication mechanisms.