



Free Mermaid diagrams covering TLS, encryption, CORS, CSRF, XSS, SQL injection, API security and more.
Web and application security is a layered discipline that spans cryptography, protocol design, threat modeling, and defensive coding practices. Understanding how attacks work — and how defenses are structured — is essential for every developer shipping code to production.
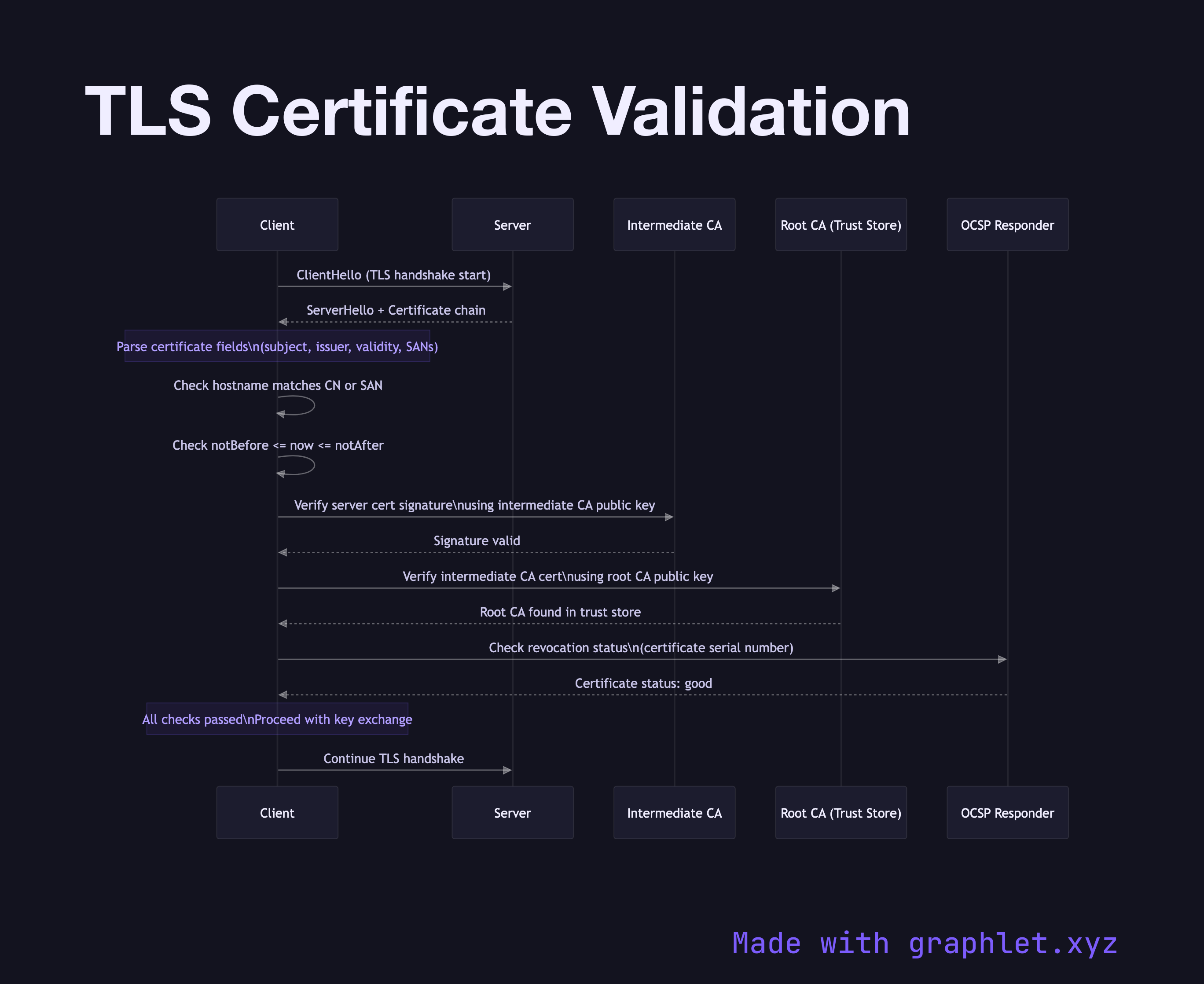
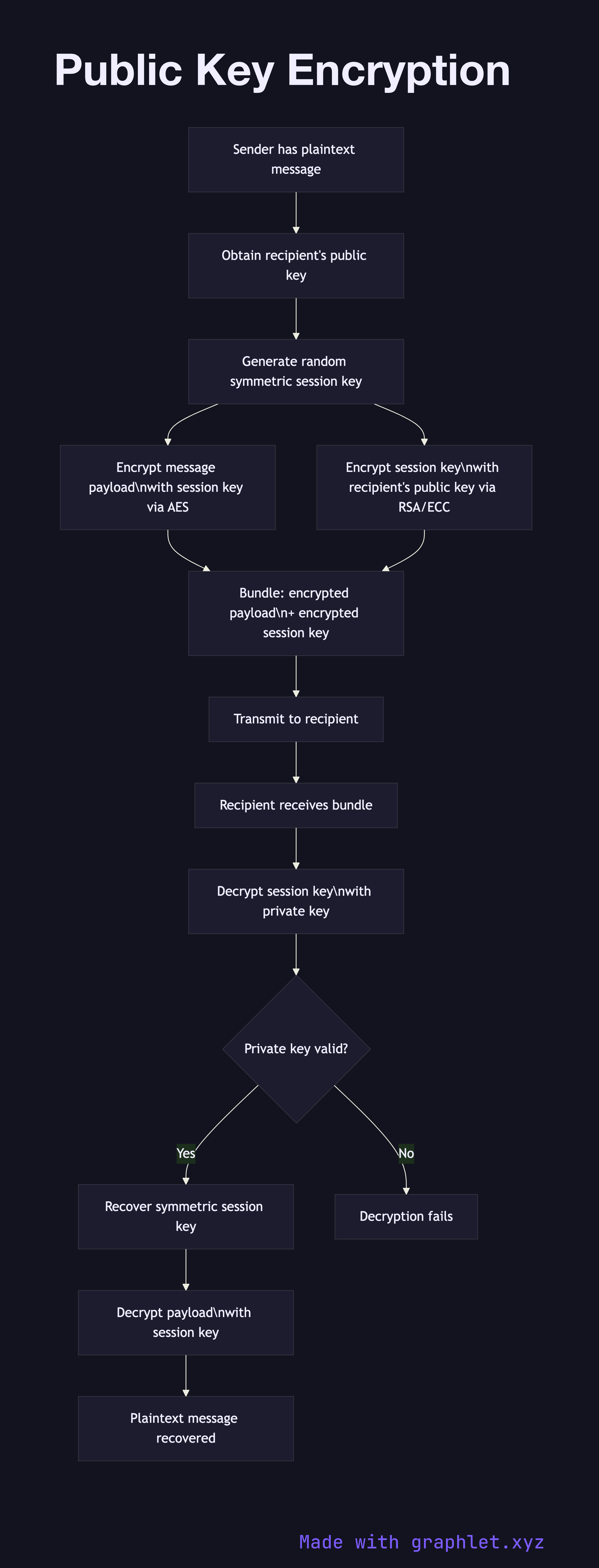
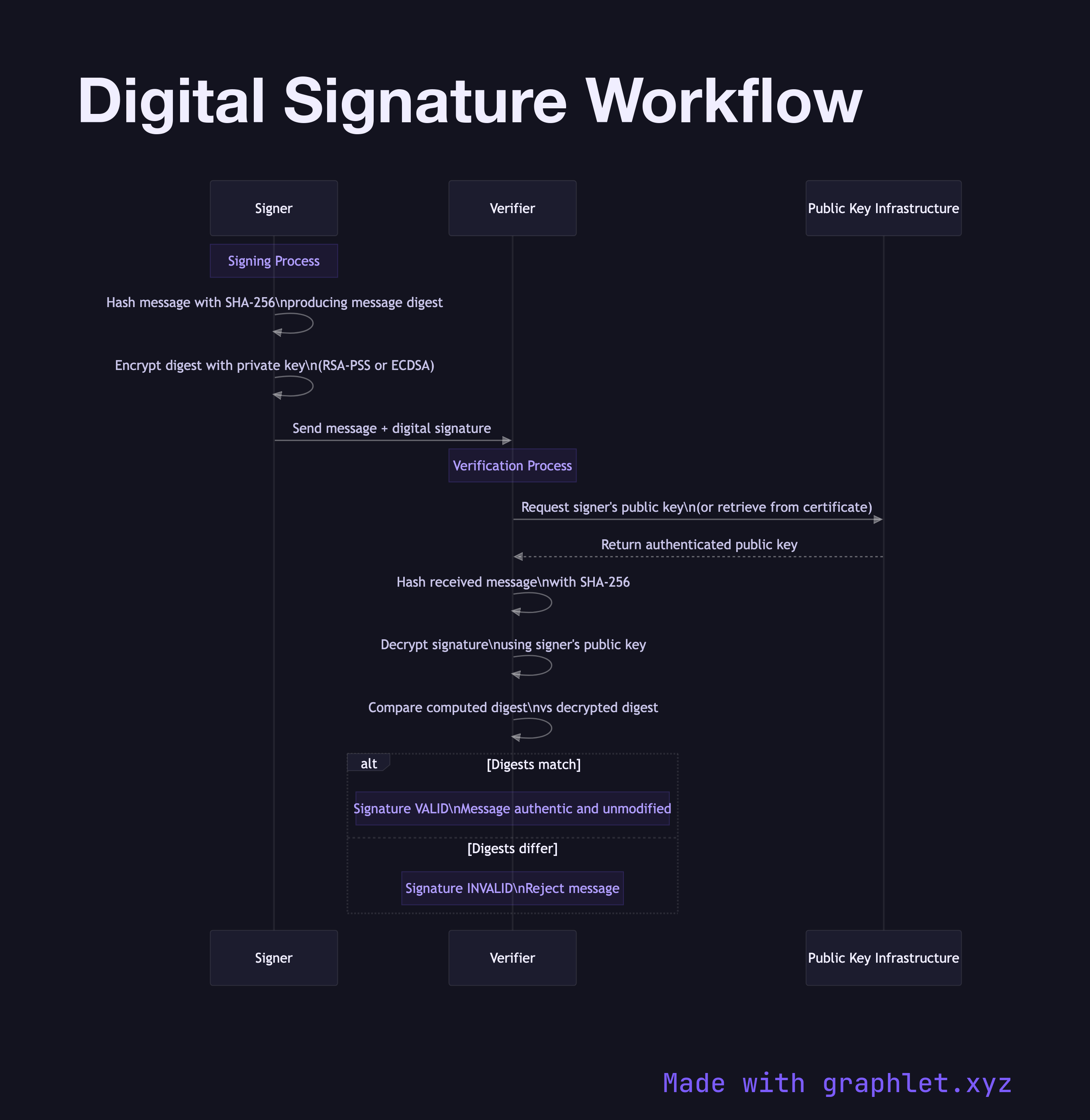
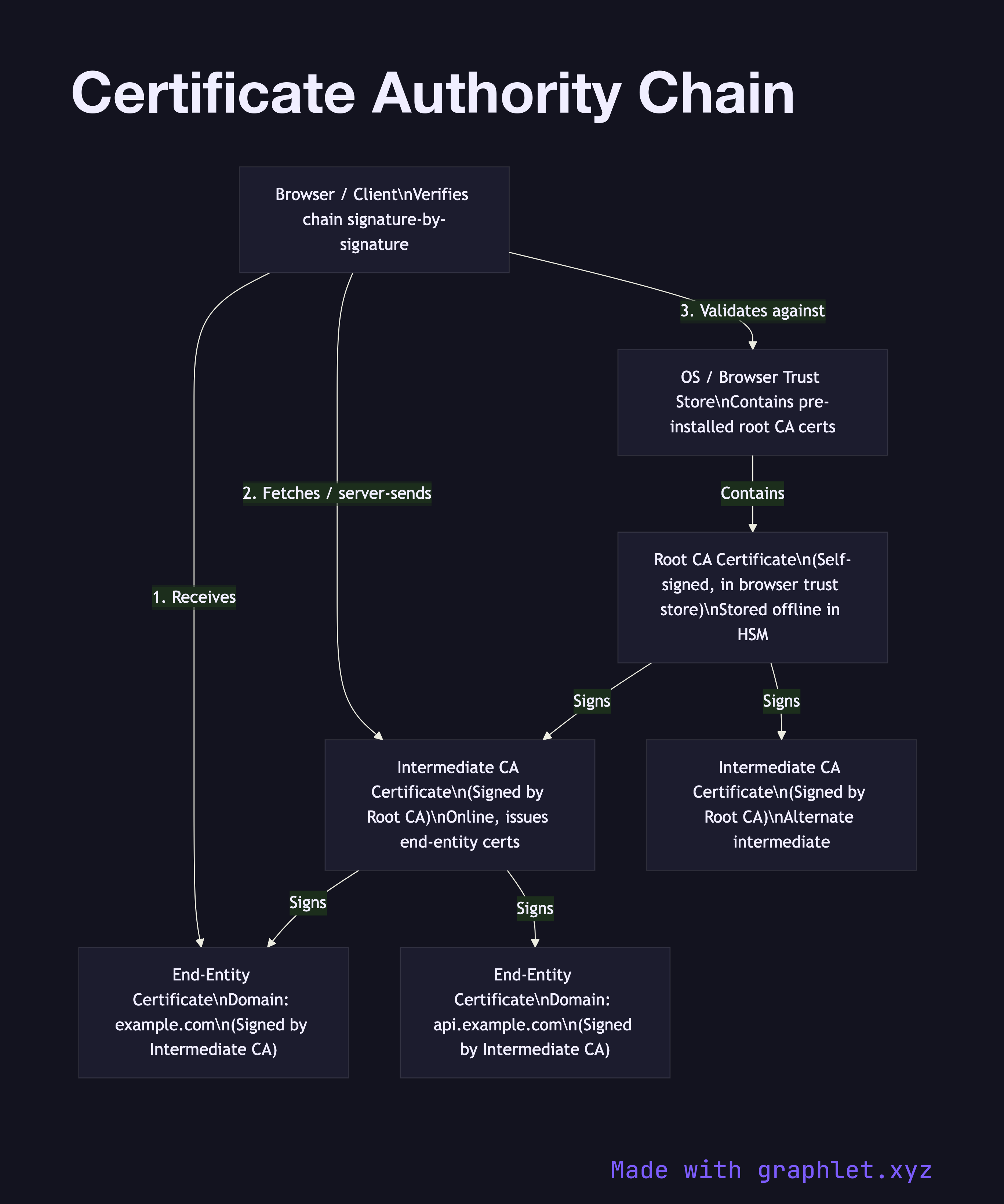
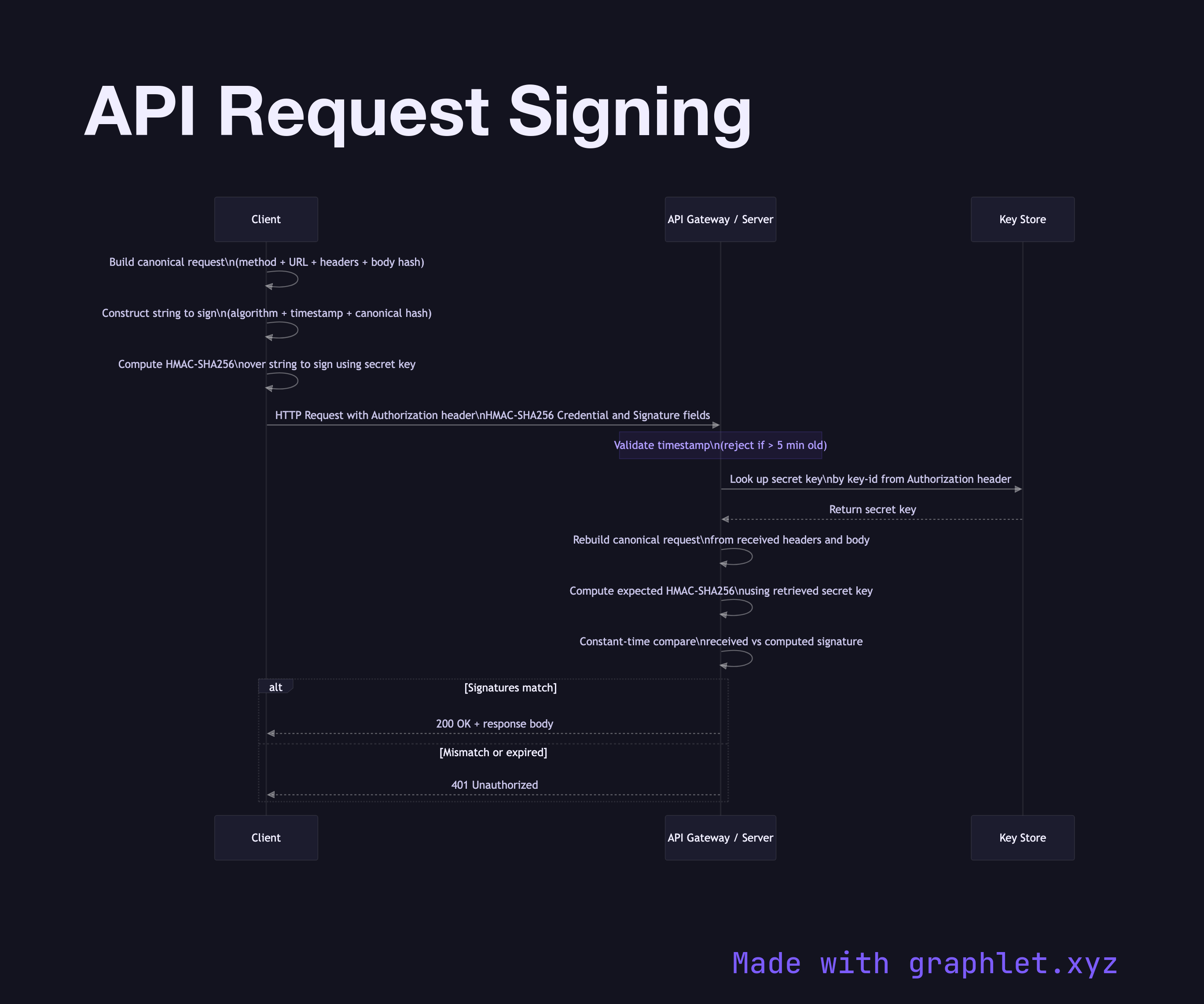
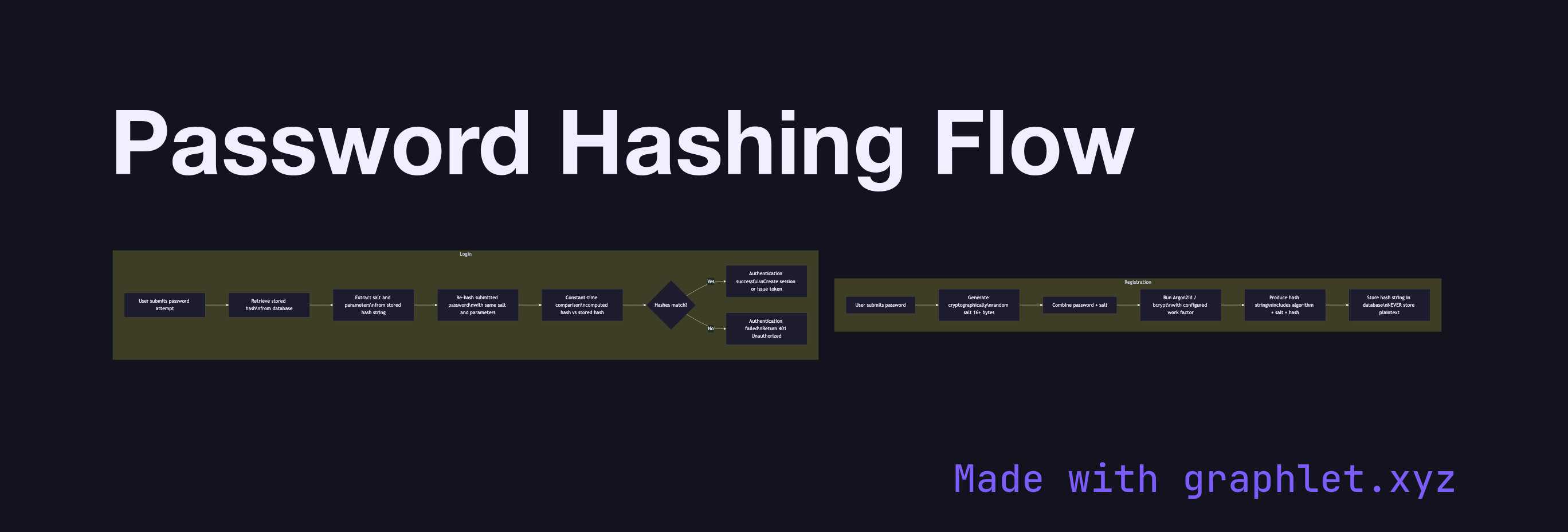
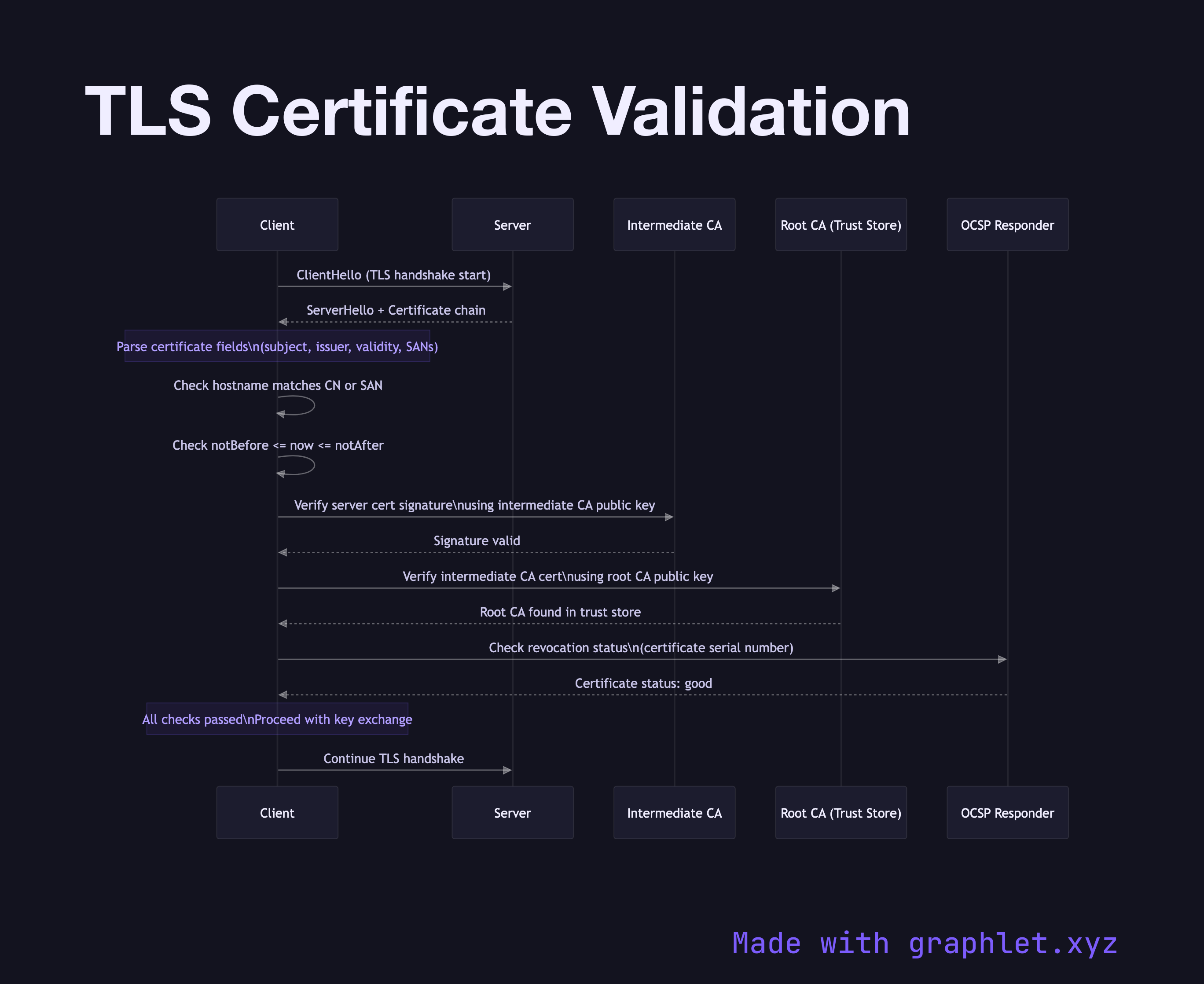
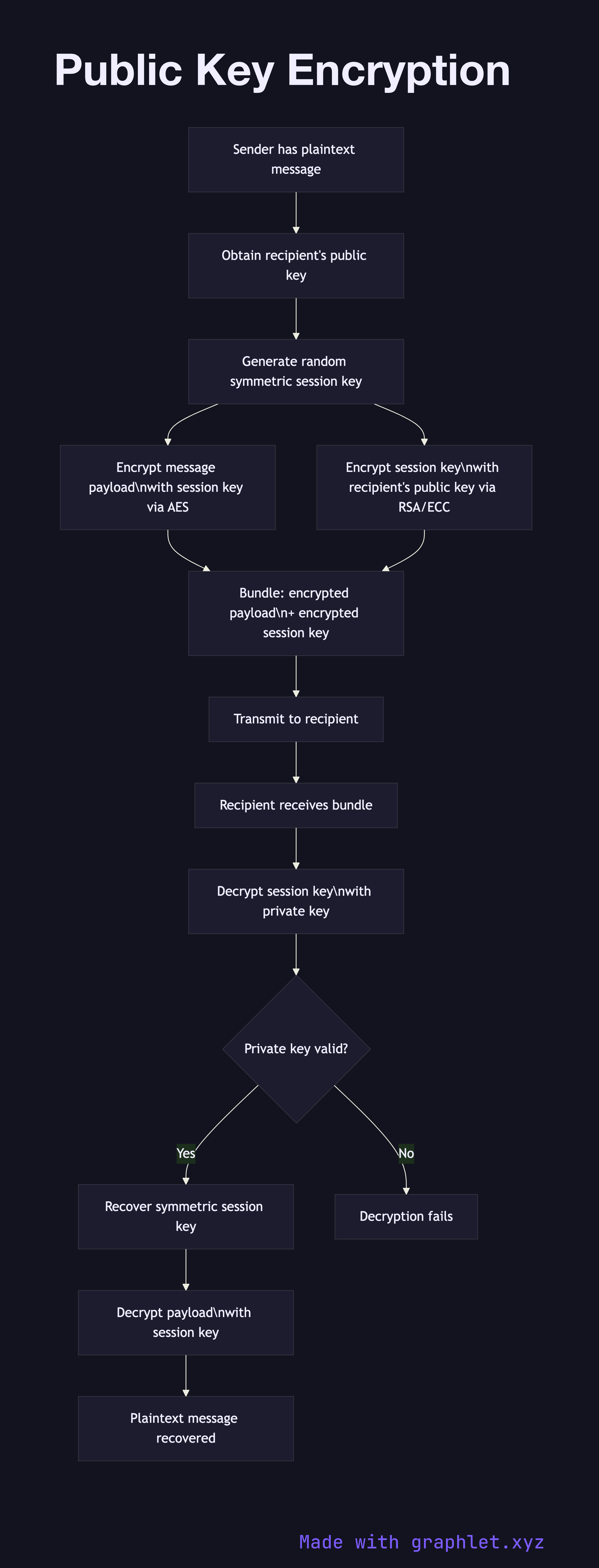
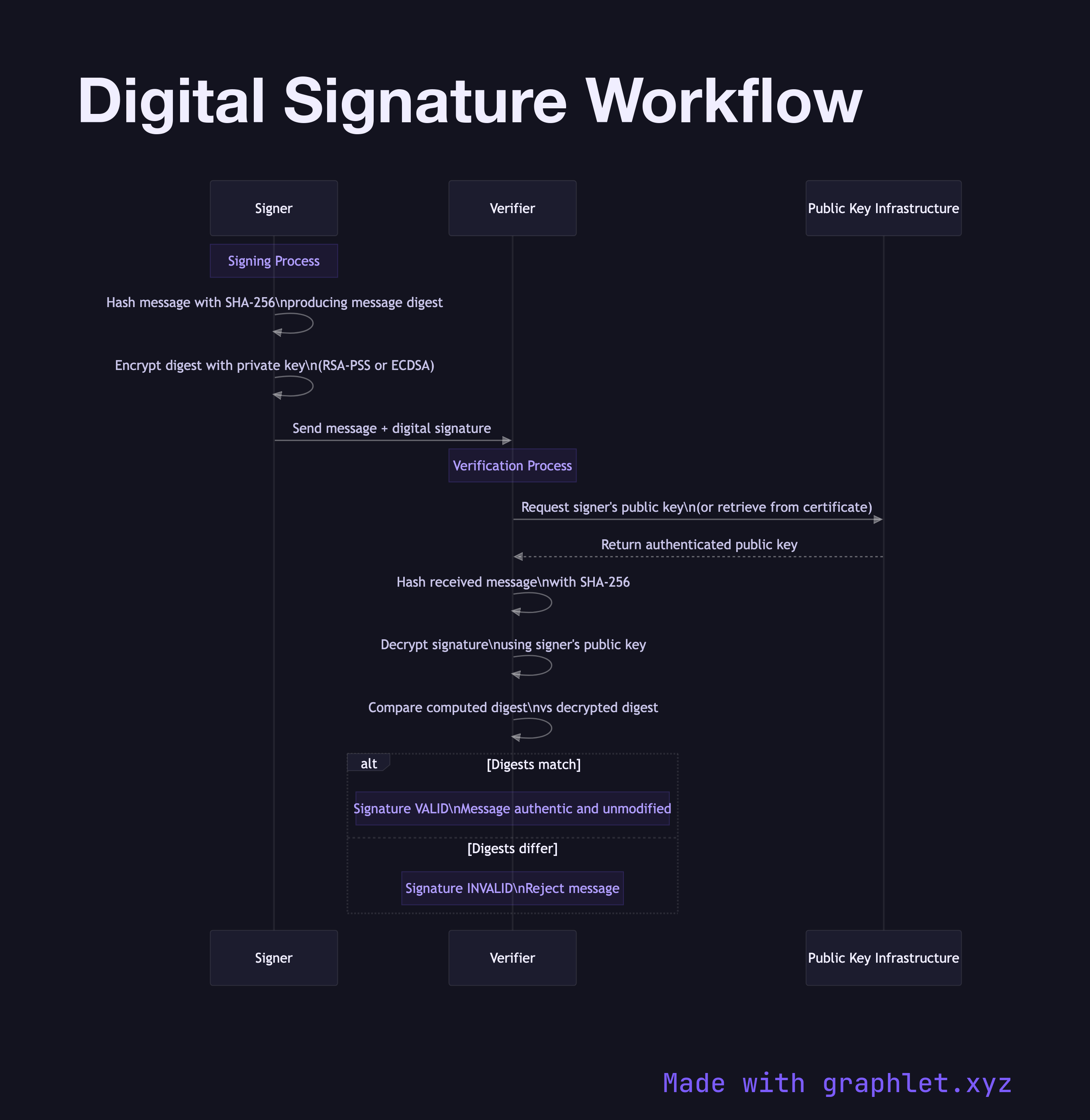
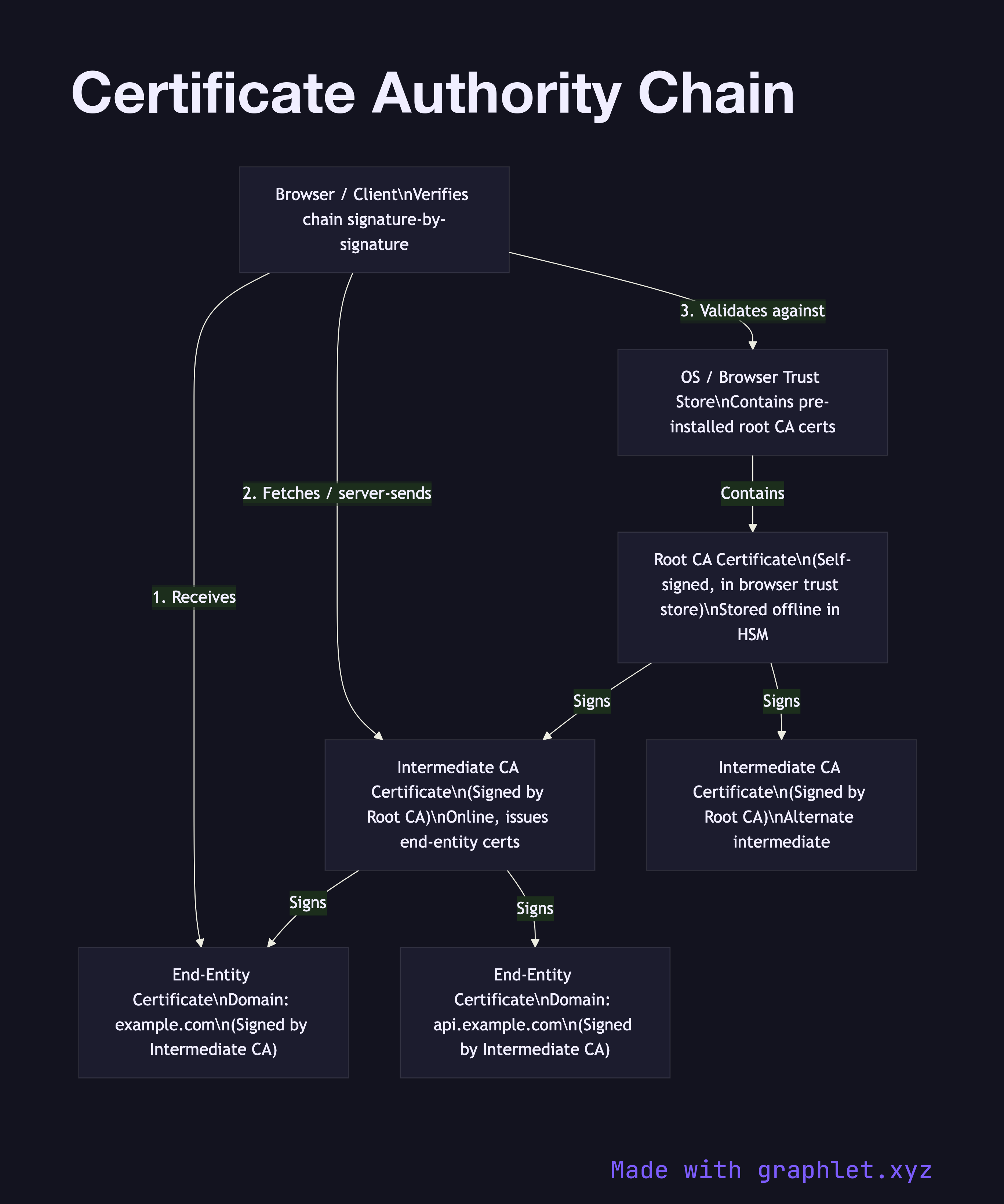
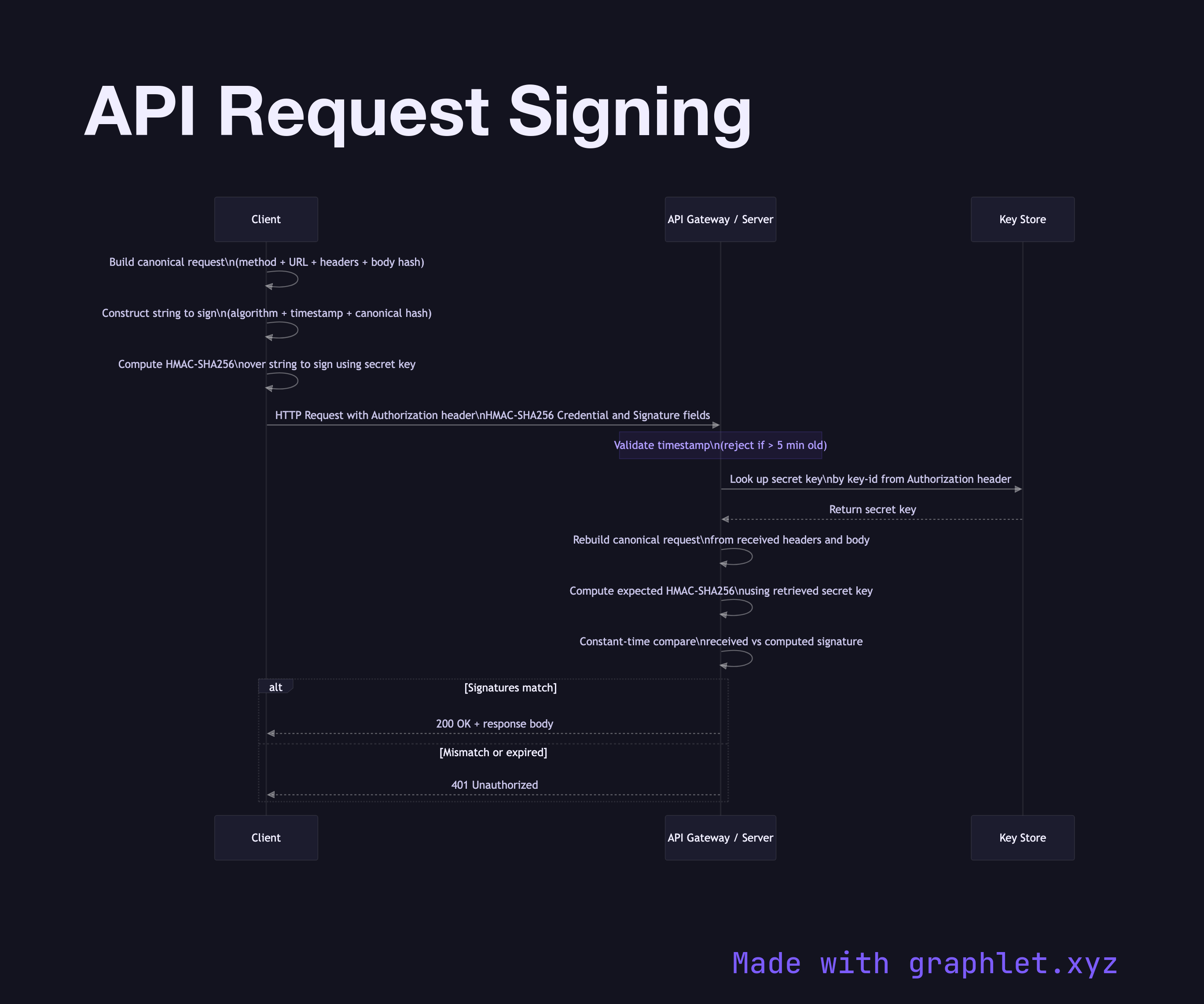
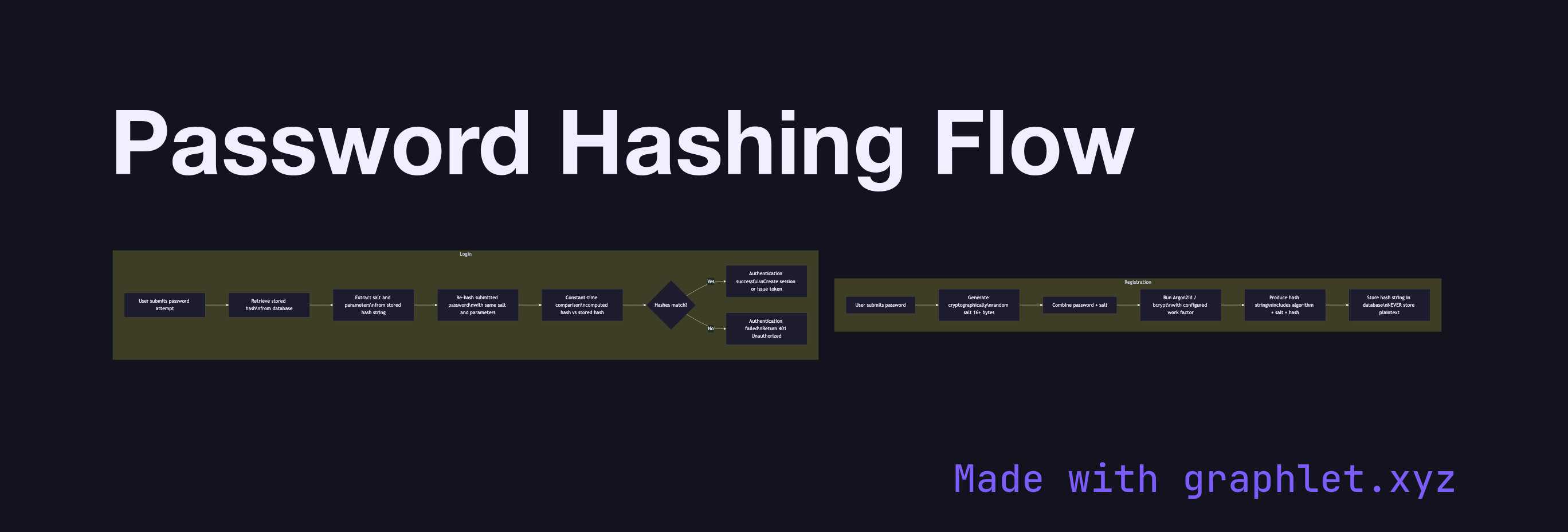
This collection covers the core security concepts you encounter building modern web applications and APIs. Start with the cryptographic foundations: TLS Certificate Validation and Certificate Authority Chain show how trust is established over HTTPS, while Public Key Encryption and Digital Signature Workflow explain the asymmetric cryptography that underpins it. For data integrity, HMAC Signing Process and API Request Signing demonstrate how requests are authenticated at the message level.
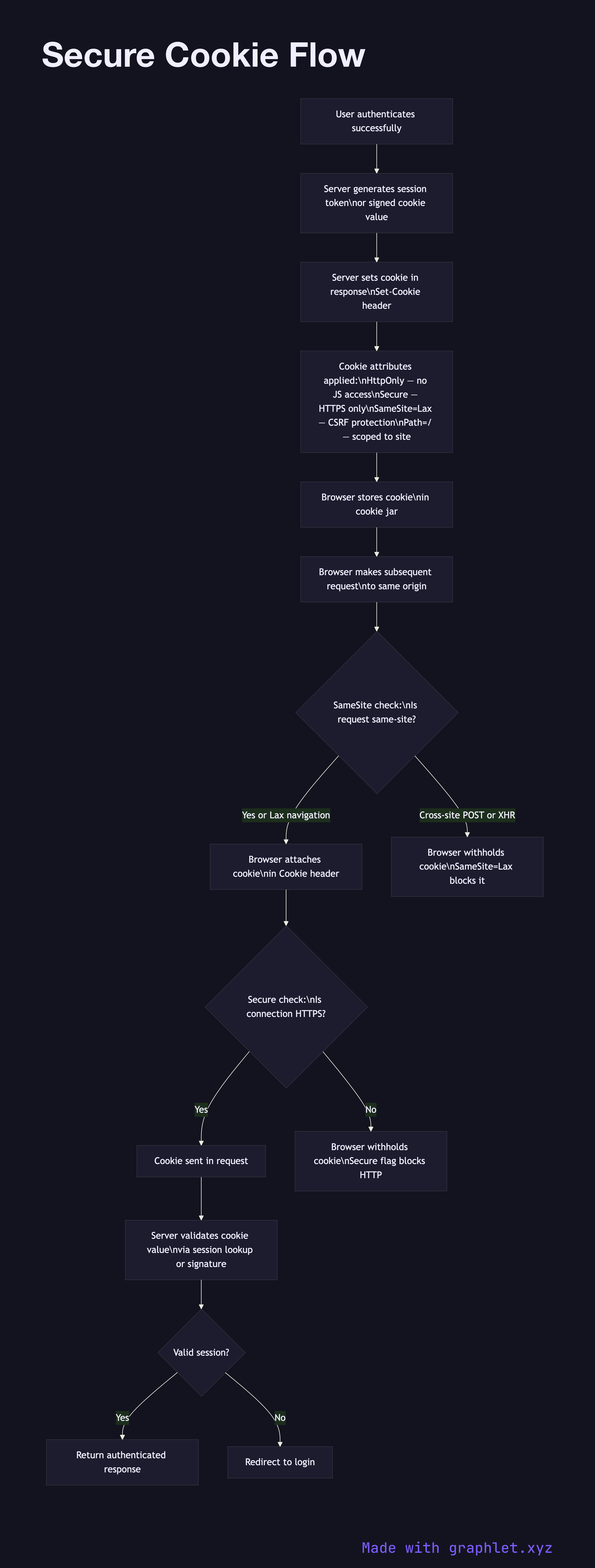
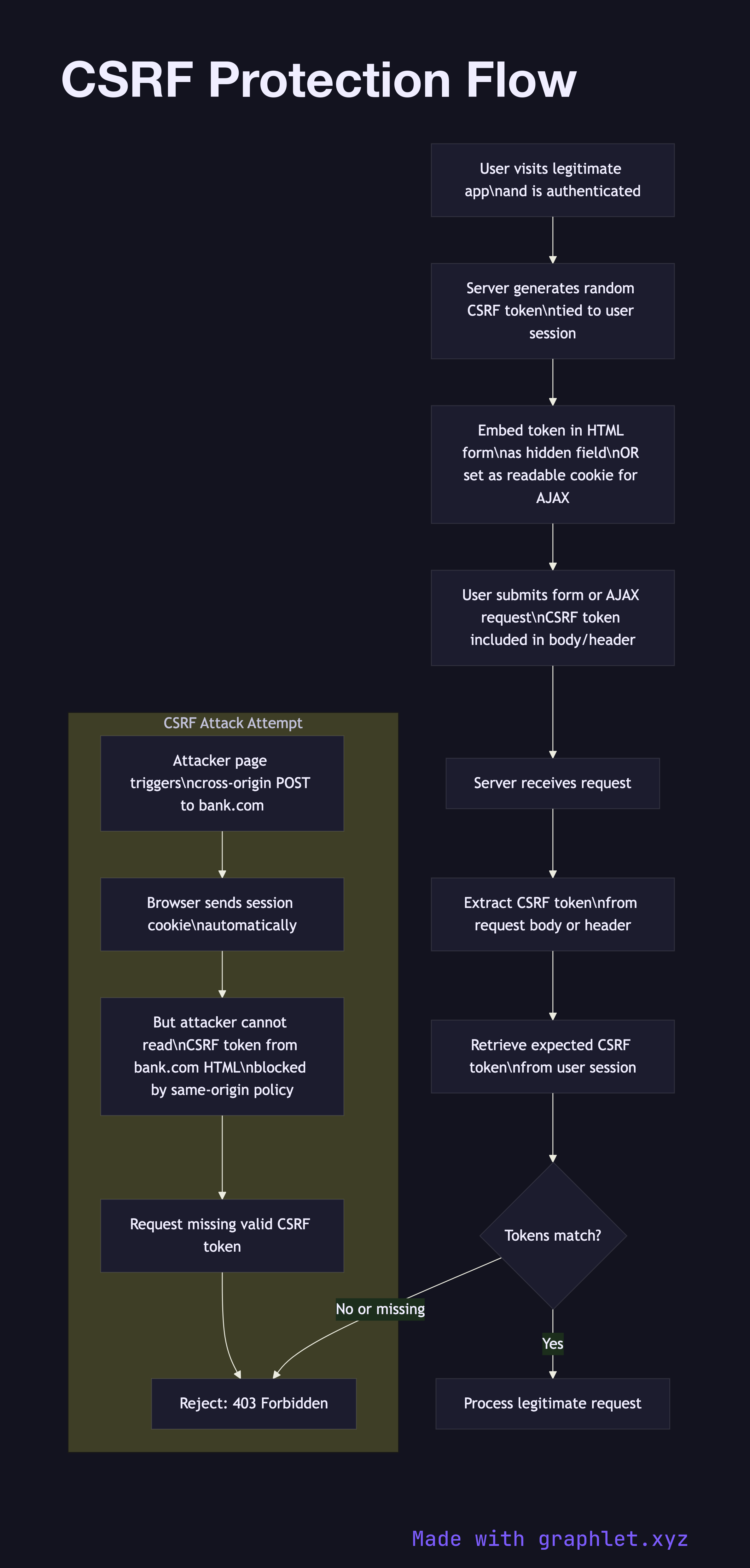
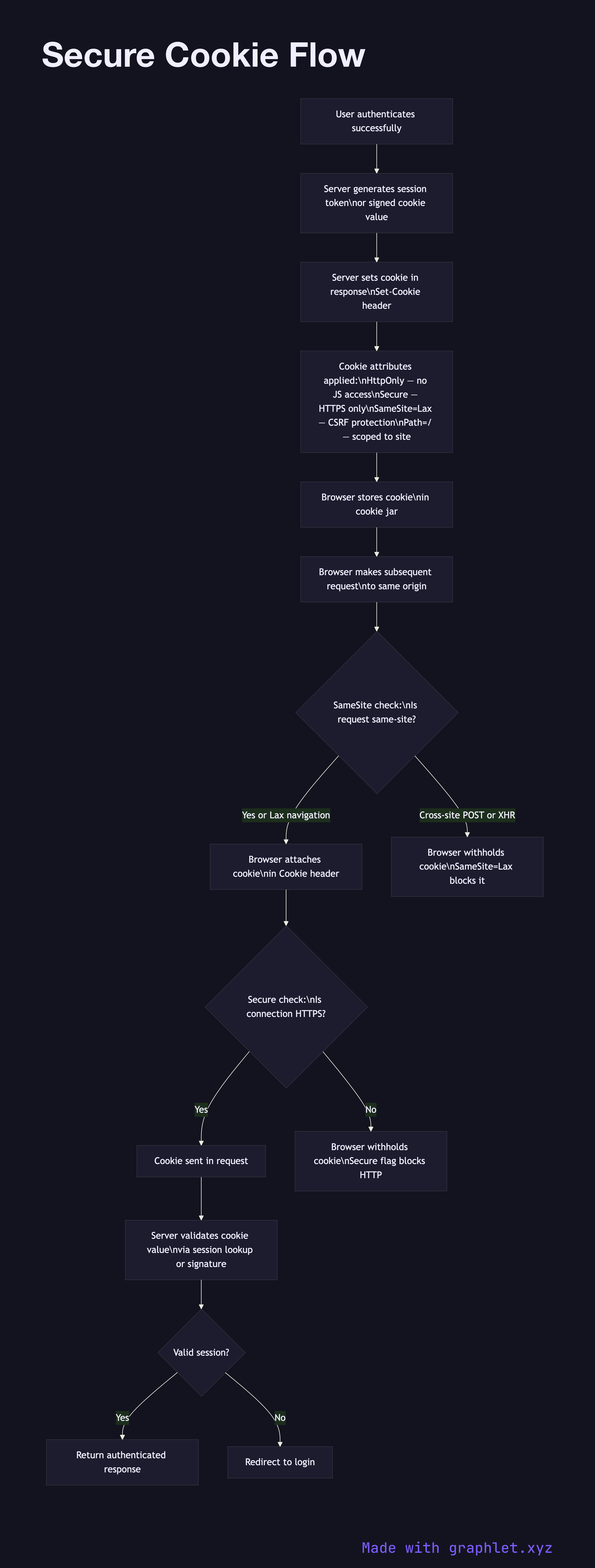
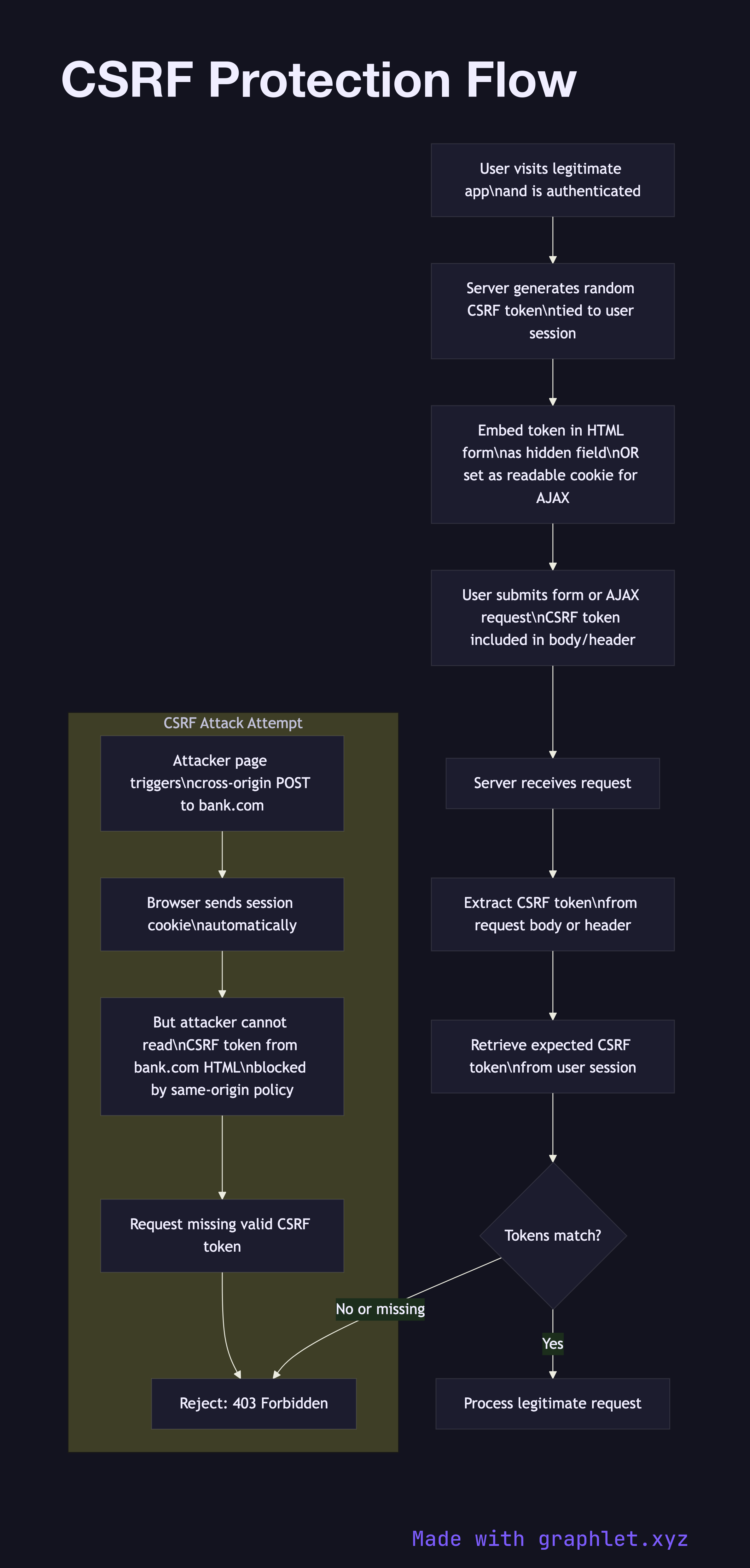
Defensive patterns for web applications are covered in depth: CSRF Protection Flow, CORS Request Flow, and Content Security Policy Flow address the browser-level controls that prevent cross-origin attacks. Attack vectors including XSS Attack Flow and SQL Injection Attack illustrate how common exploits work so you can design effective mitigations.
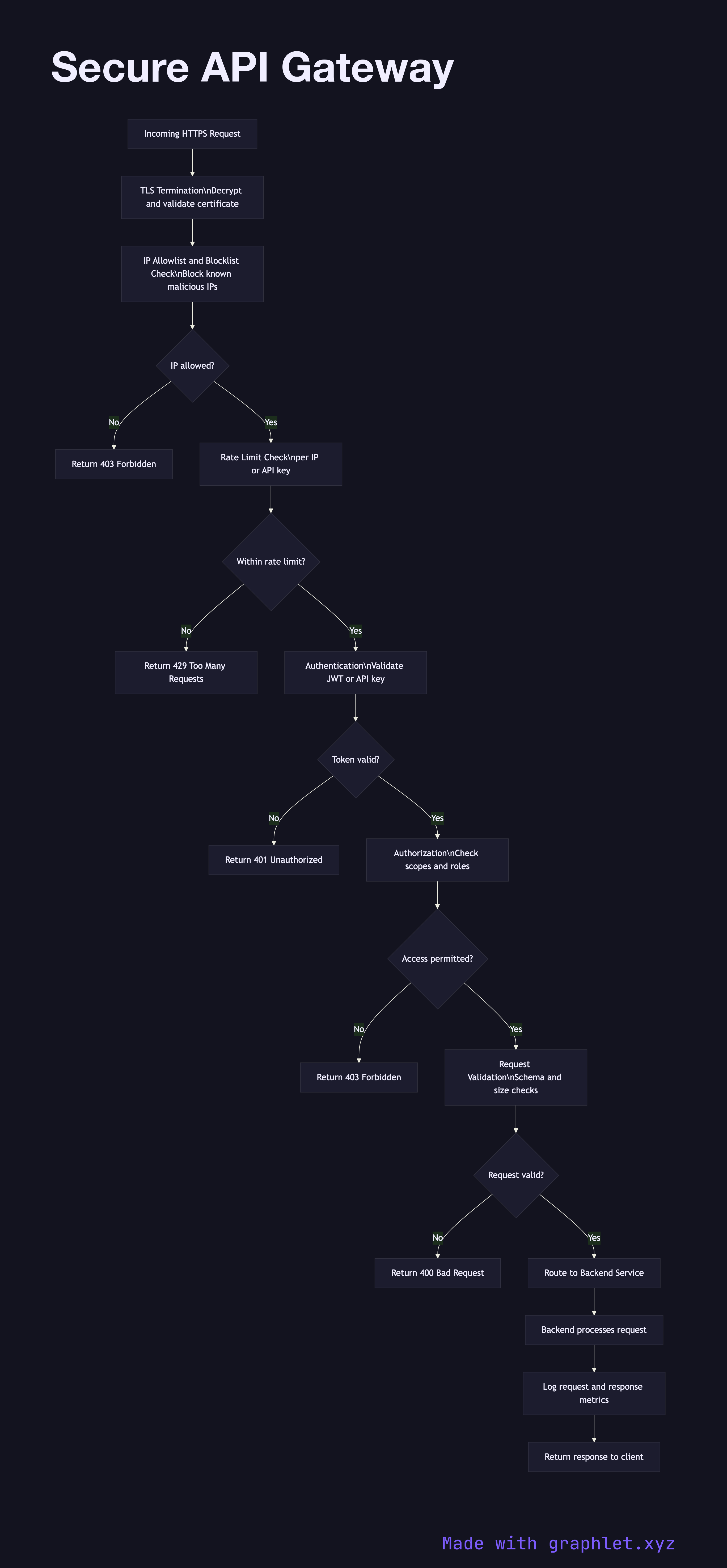
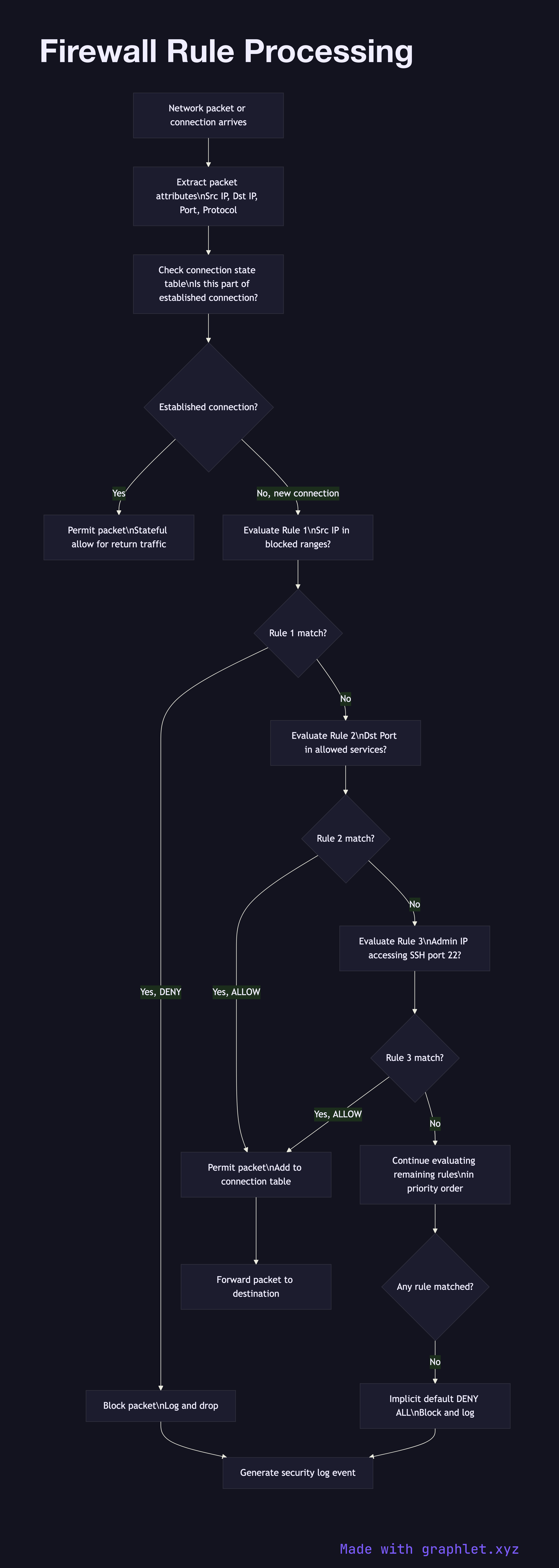
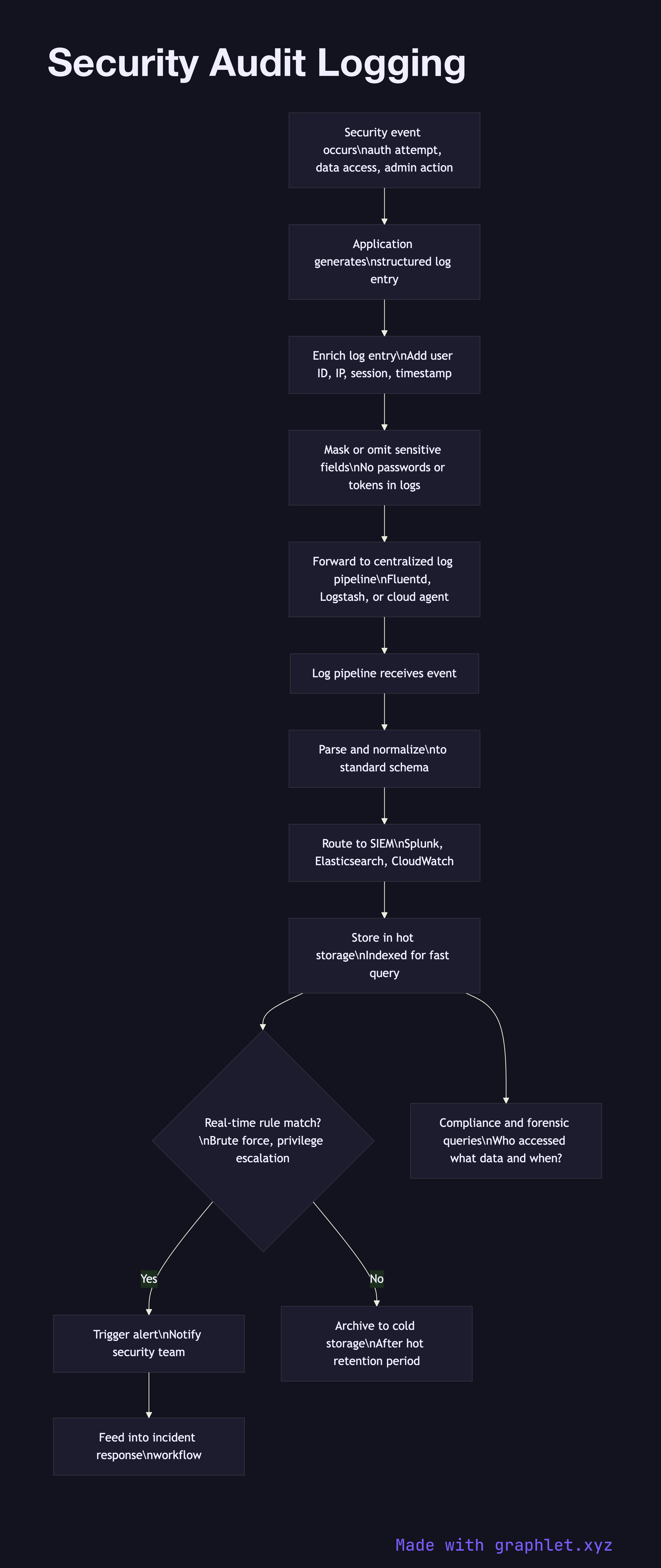
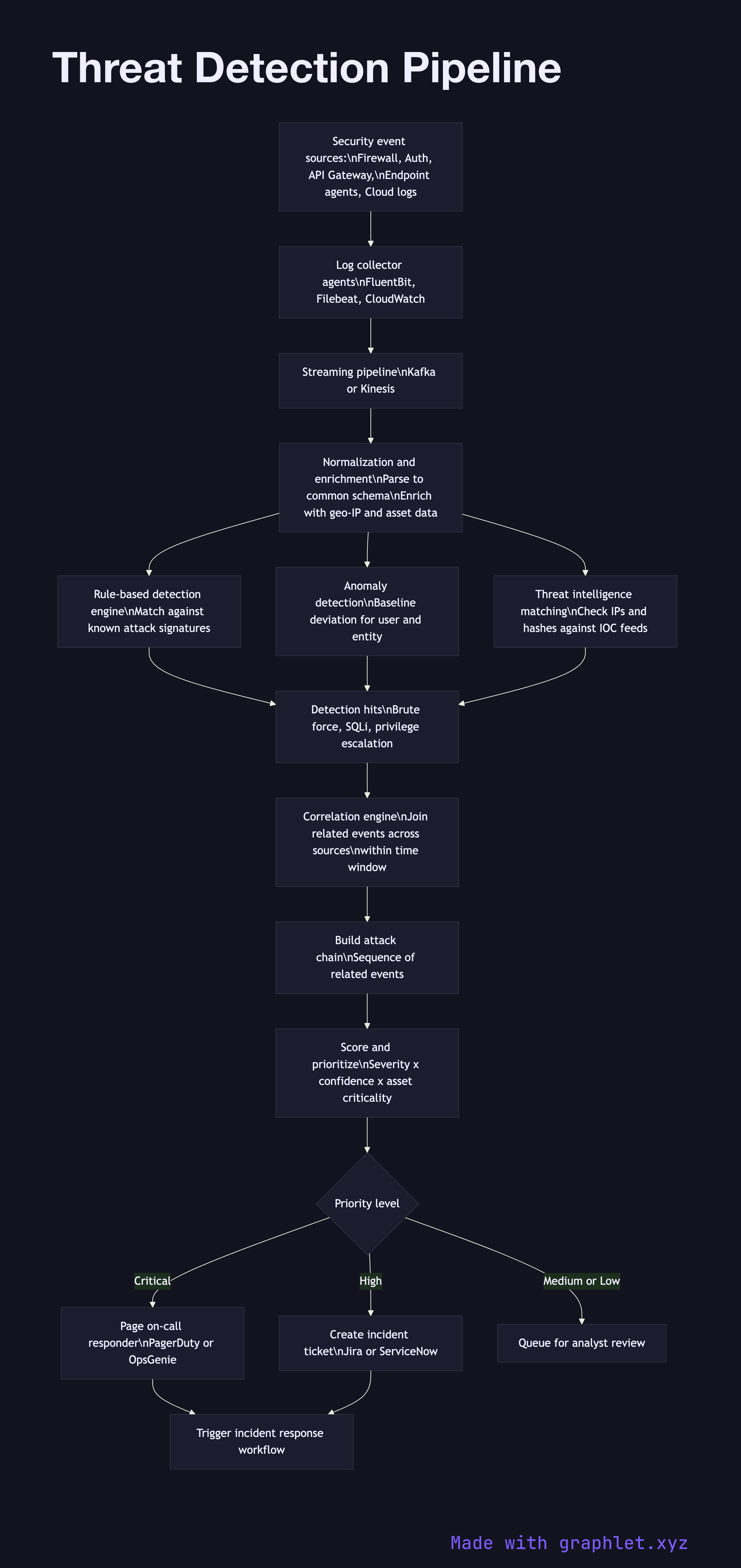
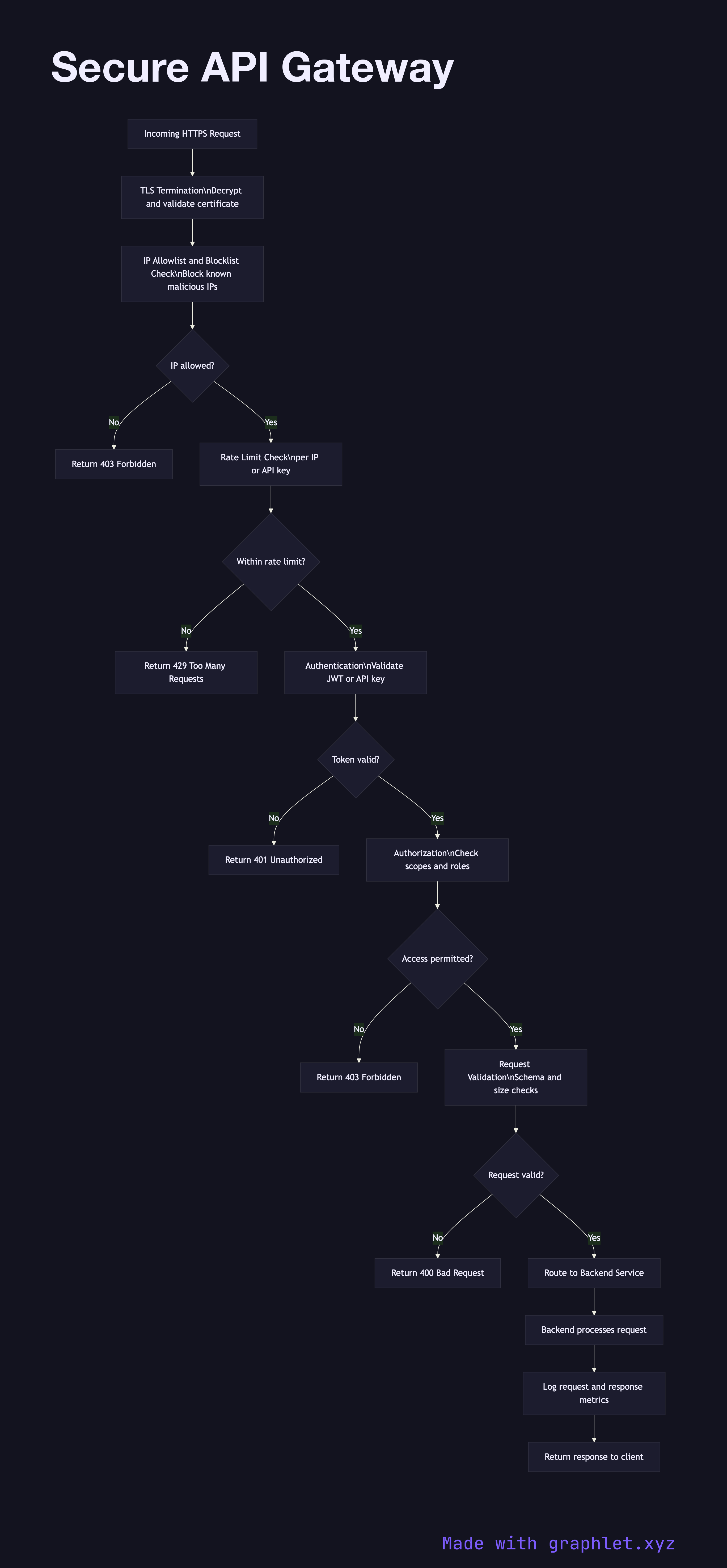
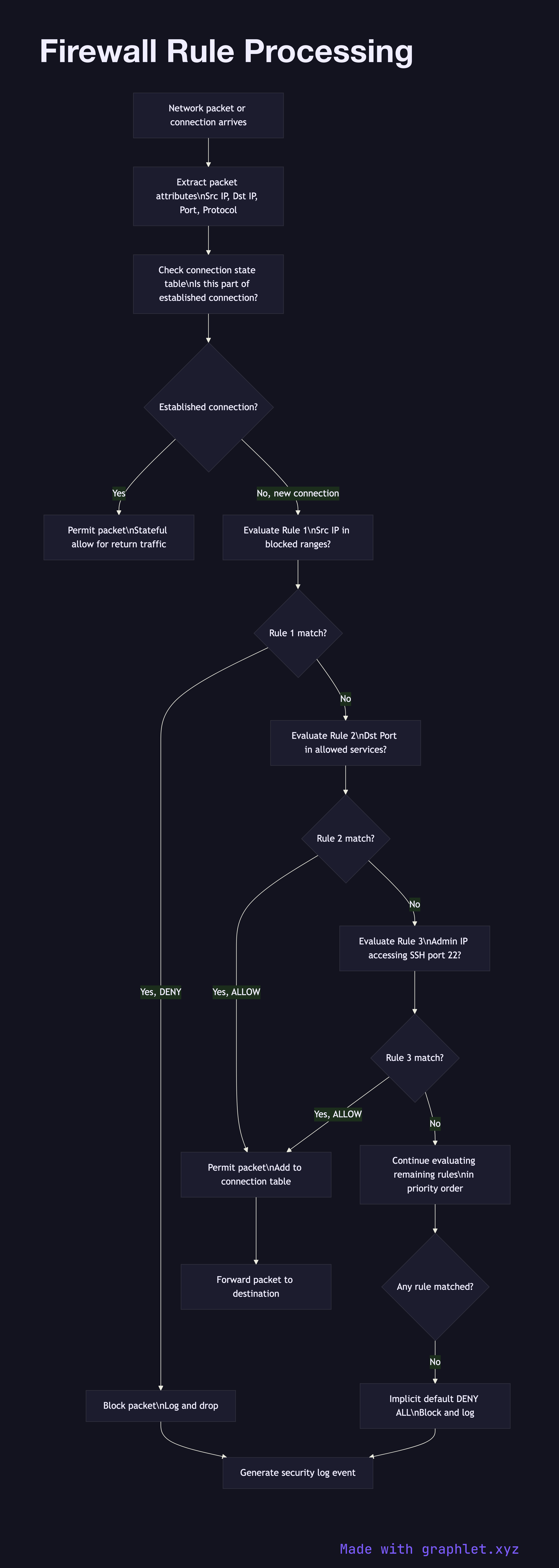
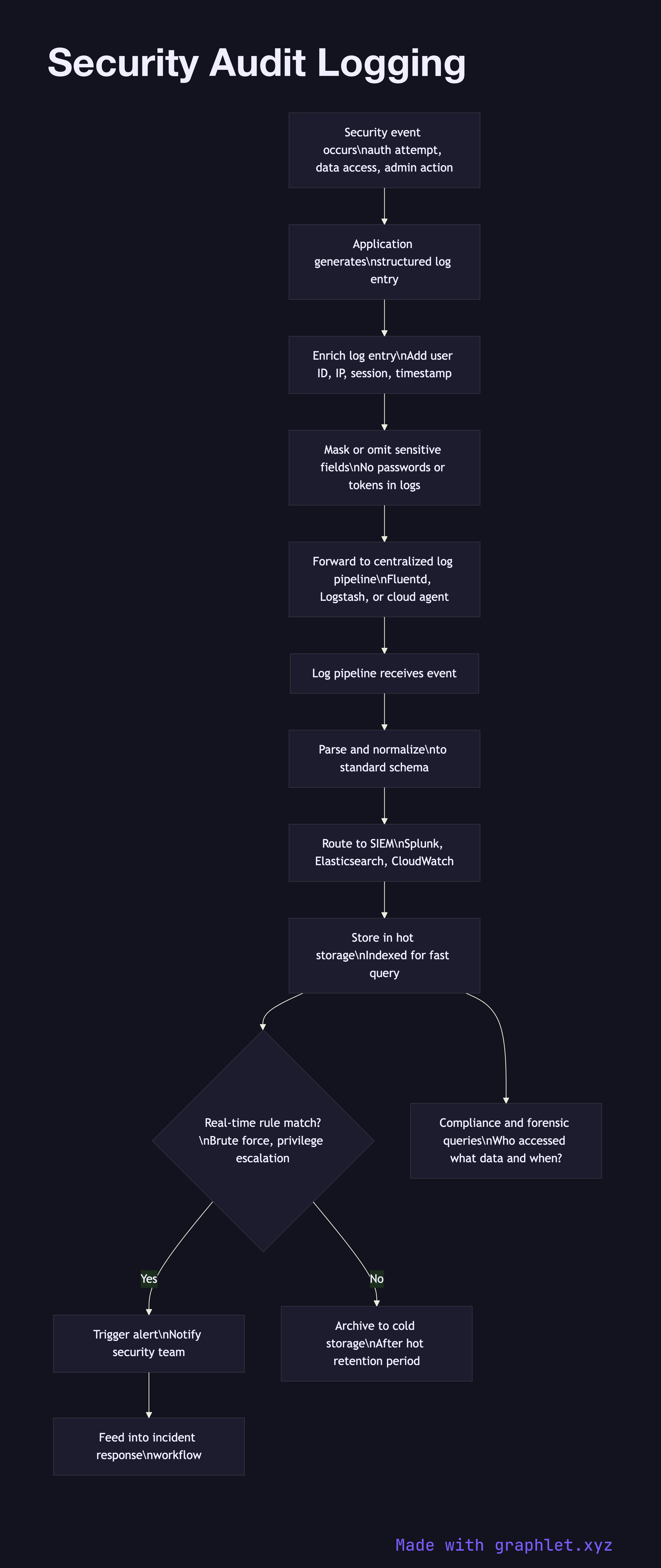
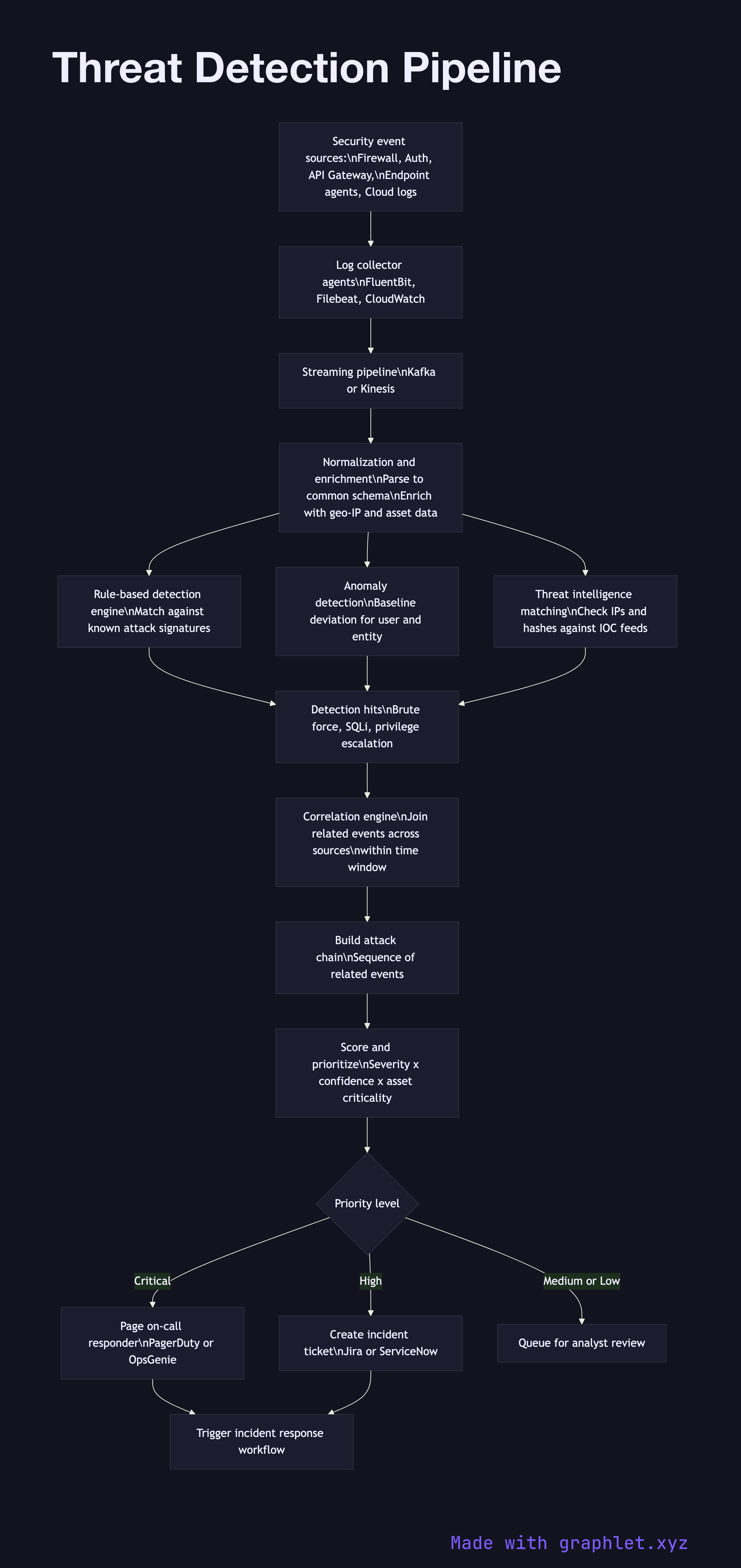
Infrastructure security is represented by Secure API Gateway, Firewall Rule Processing, Security Audit Logging, Threat Detection Pipeline, and Security Incident Response. Every diagram is free to edit and export directly in Graphlet.