Password Hashing Flow
Password hashing is the process of converting a plaintext password into a fixed-length derived value that can be stored safely, such that the original password cannot be recovered from the stored value even if the database is compromised.
Password hashing is the process of converting a plaintext password into a fixed-length derived value that can be stored safely, such that the original password cannot be recovered from the stored value even if the database is compromised.
Storing plaintext passwords is never acceptable. Even storing passwords with a simple hash like MD5 or SHA-256 is dangerous because these functions are designed to be fast, which means an attacker with the hash can test billions of guesses per second using a GPU. Password hashing algorithms solve this by being deliberately slow and memory-intensive.
Modern password hashing uses adaptive algorithms specifically designed for this purpose: bcrypt, scrypt, Argon2id, and PBKDF2. Argon2id is the current recommendation from OWASP and the Password Hashing Competition winner. These algorithms accept a configurable work factor (cost parameter) that you increase over time as hardware gets faster, keeping brute-force attacks expensive.
A critical component is the salt: a cryptographically random value (typically 16+ bytes) that is generated uniquely for each password and prepended to the password before hashing. The salt is stored alongside the hash in the database. Salts prevent precomputed dictionary attacks (rainbow tables) by ensuring that identical passwords hash to different values.
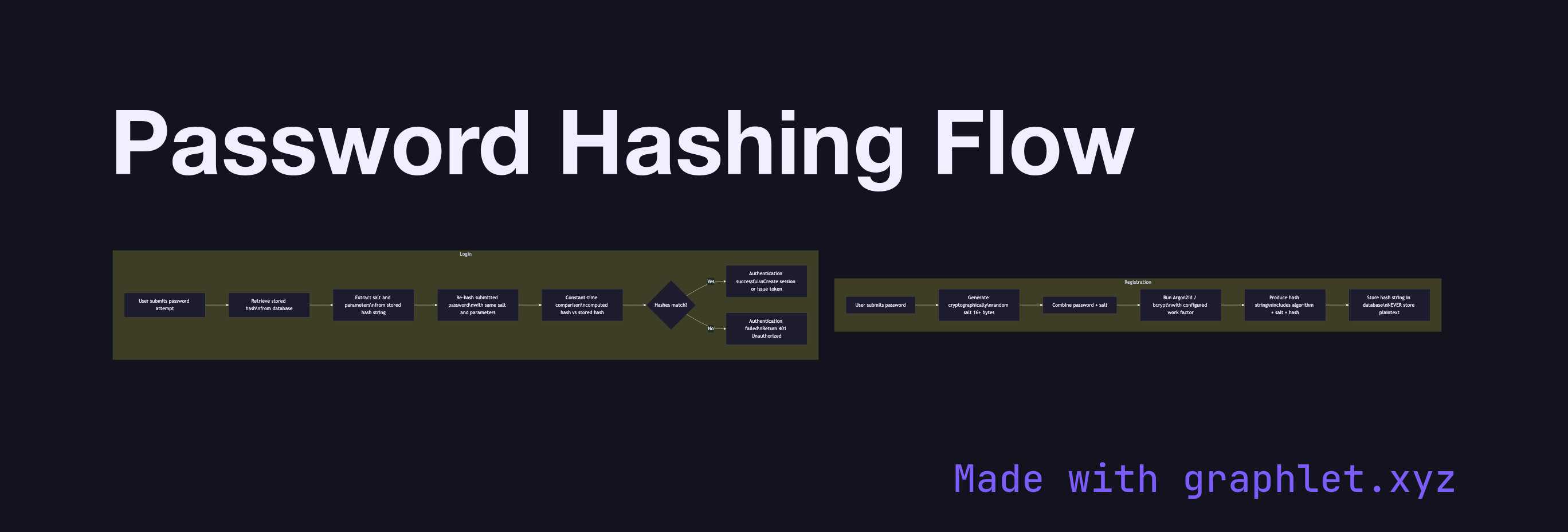
During registration, the server generates a random salt, combines it with the password, runs the result through the chosen algorithm at the configured work factor, and stores the salt and hash together (the algorithm encodes both in a single string in modern implementations like $argon2id$v=19$m=65536...). The plaintext password is never stored.
During login, the server retrieves the stored hash, extracts the salt and parameters, re-hashes the submitted password with the same parameters, and compares the result to the stored hash using a constant-time comparison. See Secure Session Storage for what happens after a successful login.