Service Mesh Architecture
A service mesh is a dedicated infrastructure layer that handles service-to-service communication in a microservices deployment, providing traffic management, observability, and security without requiring changes to application code.
A service mesh is a dedicated infrastructure layer that handles service-to-service communication in a microservices deployment, providing traffic management, observability, and security without requiring changes to application code.
What the diagram shows
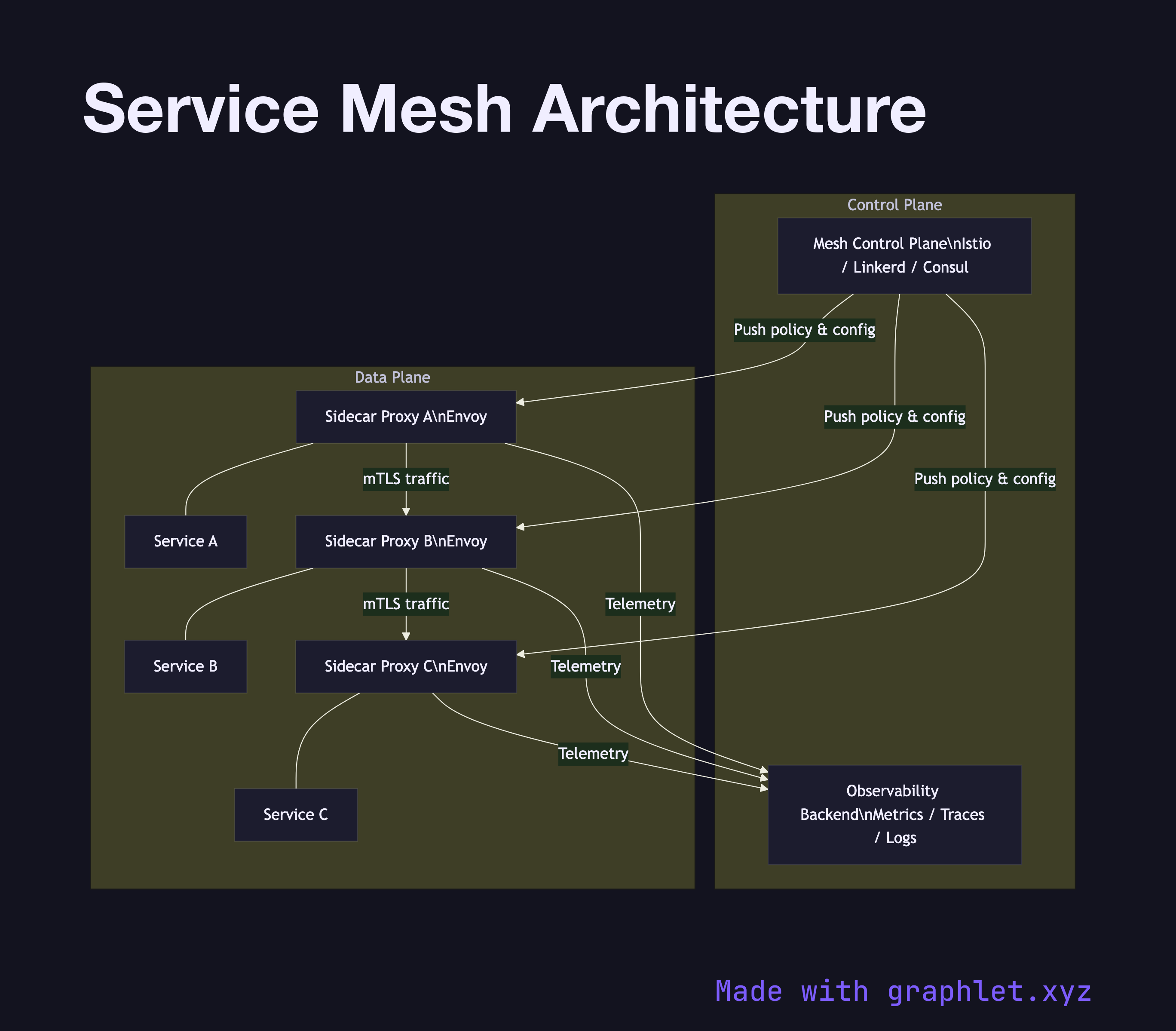
The diagram is split into two planes: the Data Plane and the Control Plane. In the data plane, each microservice — Service A, Service B, and Service C — is paired with a Sidecar Proxy (typically Envoy). All network traffic between services flows through these proxies rather than directly between the application containers. The sidecar handles TLS termination, load balancing, retries, and circuit breaking transparently.
The Control Plane (represented here as a single Mesh Control Plane node, e.g. Istio, Linkerd, or Consul) pushes policy and configuration down to every sidecar. It also collects telemetry — metrics, traces, and access logs — and feeds them to an Observability Backend for dashboards and alerting.
Why this matters
Before service meshes, every team had to implement retries, timeouts, and mutual TLS inside their own service. A mesh externalizes that logic into the infrastructure layer, making it consistent across all services regardless of programming language. The trade-off is added latency (one extra network hop per call through the sidecar) and operational overhead running the control plane.
For the entry-point layer above the mesh, see API Gateway Architecture. For the resilience pattern the sidecar enforces, see Circuit Breaker Architecture. Service discovery within the mesh is covered in Service Discovery Flow.