Infrastructure as Code Pipeline
Infrastructure as Code (IaC) is the practice of defining cloud resources — networks, compute instances, databases, IAM roles — in version-controlled configuration files, then applying those definitions through an automated pipeline rather than through manual console clicks.
Infrastructure as Code (IaC) is the practice of defining cloud resources — networks, compute instances, databases, IAM roles — in version-controlled configuration files, then applying those definitions through an automated pipeline rather than through manual console clicks.
Terraform is the dominant IaC tool, using a declarative HCL (HashiCorp Configuration Language) syntax. Pulumi, AWS CDK, and Crossplane are alternatives. All follow the same core workflow: write → plan → review → apply.
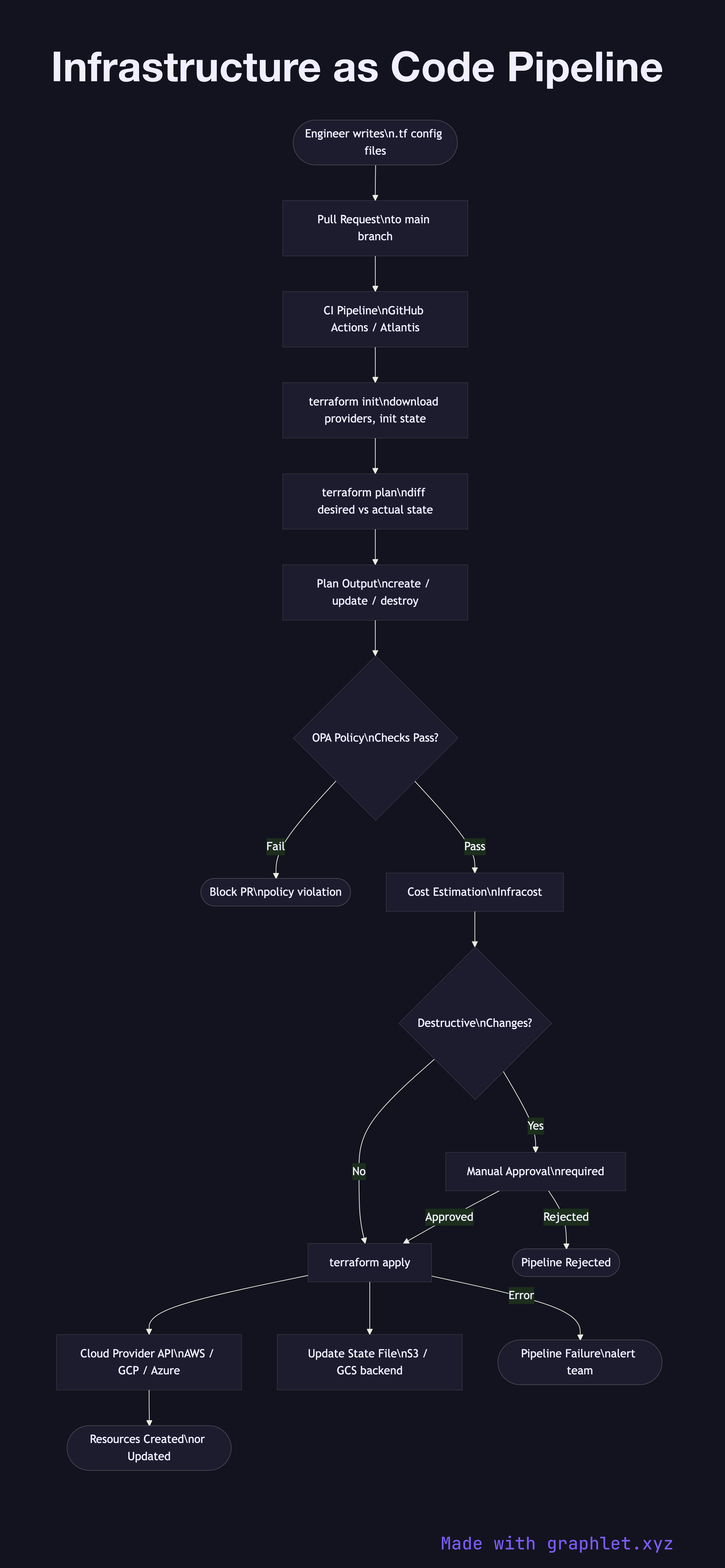
Source control trigger: Engineers write or modify .tf files in a Git repository. A pull request triggers the IaC pipeline in CI.
Terraform init: Downloads required provider plugins and initializes the remote state backend (S3, GCS, or Terraform Cloud).
Terraform plan: Compares the desired state in code against the actual state recorded in the state file and the live cloud API. Produces a human-readable diff: resources to create, update, or destroy.
Policy checks: Before apply, plan output is evaluated by policy-as-code tools — OPA (Open Policy Agent) with Conftest, or HashiCorp Sentinel — enforcing rules like "no public S3 buckets", "all EC2 instances must use approved AMIs", or "production changes require a cost estimate under $500/month".
Approval gate: Destructive changes (resource deletion, IAM policy modifications) require explicit human approval via the pull request or a dedicated approval step.
Terraform apply: Executes the plan, calling cloud provider APIs to create, update, or delete resources. The state file is updated atomically. Apply failures are surfaced as pipeline failures triggering rollback analysis.
See Cloud IAM Permission Model for provisioning IAM resources via IaC, and Cloud Secret Management for handling secrets referenced in Terraform configurations.