Multi Cloud Architecture
Multi-cloud architecture is the practice of distributing workloads, data, and services across two or more cloud providers — reducing vendor lock-in, improving resilience against provider outages, and enabling workload placement based on each provider's unique strengths.
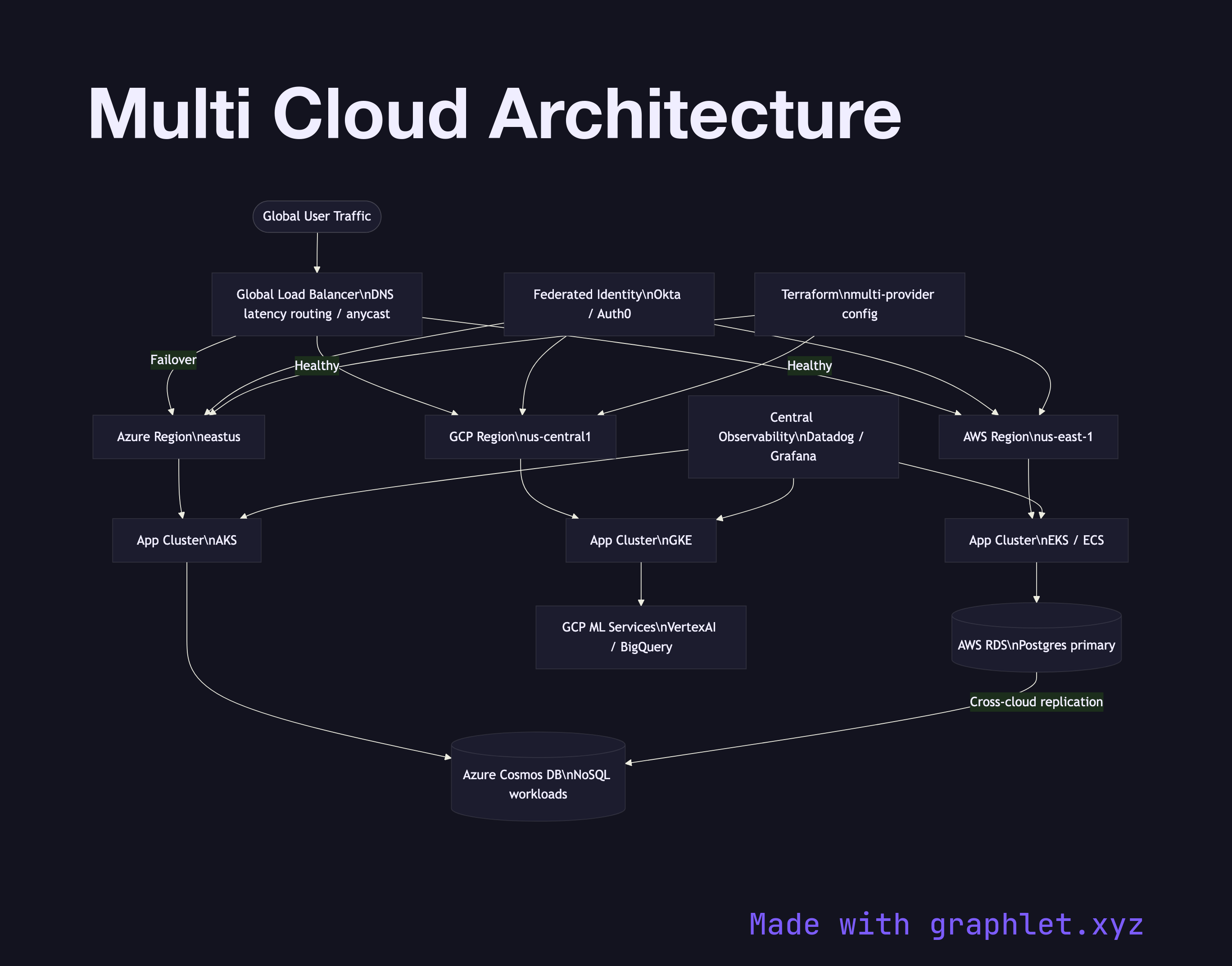
Multi-cloud architecture is the practice of distributing workloads, data, and services across two or more cloud providers — reducing vendor lock-in, improving resilience against provider outages, and enabling workload placement based on each provider's unique strengths.
A multi-cloud strategy is distinct from a simple DR (disaster recovery) setup. In active-active multi-cloud, workloads run simultaneously on multiple clouds and traffic is balanced across them. This requires solving several hard problems:
Traffic routing: A global DNS-based or anycast load balancer (Cloudflare, AWS Route 53 latency routing, or a dedicated multi-cloud networking layer like Aviatrix) directs user requests to the lowest-latency or healthiest cloud region. Health checks monitor each cloud endpoint and failover traffic within seconds if one provider's API or a whole region becomes unavailable.
Data synchronization: The hardest part of multi-cloud. Databases must be replicated or sharded across providers. Managed databases (CockroachDB, Spanner, PlanetScale) offer multi-region replication. Object storage uses CRR (Cross-Region Replication) extended across clouds. Eventual consistency trade-offs must be explicit.
Identity federation: A federated identity provider (Okta, Auth0) issues tokens that are trusted by all cloud providers, avoiding the need to manage separate IAM users in each cloud.
Infrastructure as Code: Terraform with provider configurations for AWS, GCP, and Azure enables consistent provisioning across clouds. See Infrastructure as Code Pipeline for the deployment workflow.
Observability: Centralised logging and monitoring aggregates signals from all clouds into a single pane of glass. See Cloud Monitoring Pipeline.