TLS Certificate Validation
TLS certificate validation is the process by which a client verifies that a server's digital certificate is authentic, unexpired, and issued by a trusted authority before establishing an encrypted connection.
TLS certificate validation is the process by which a client verifies that a server's digital certificate is authentic, unexpired, and issued by a trusted authority before establishing an encrypted connection.
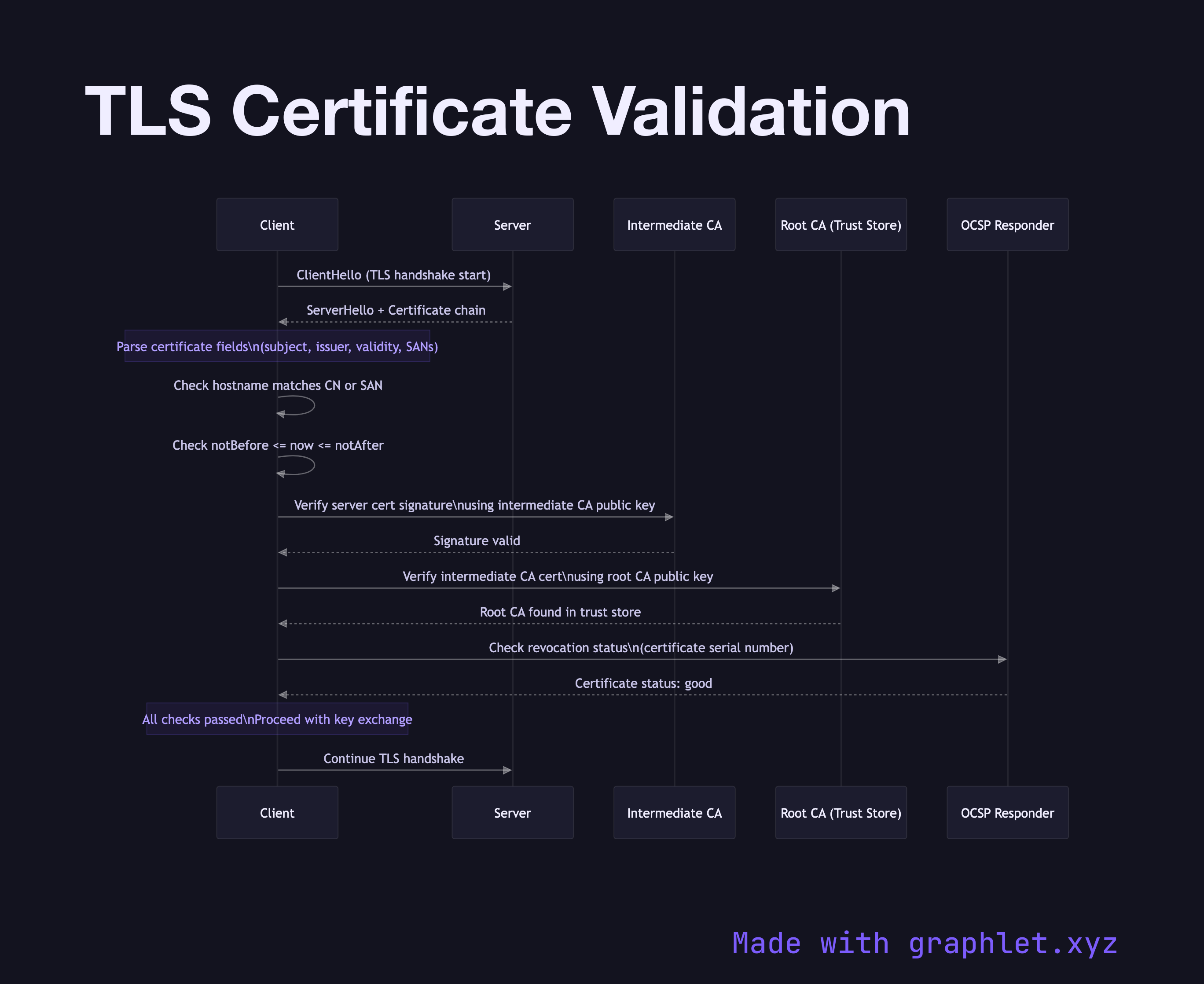
When a browser or API client connects to an HTTPS endpoint, the server presents its TLS certificate during the handshake. The client must perform several checks before trusting this certificate. First, it parses the certificate to extract the subject (the domain name the certificate was issued for), the issuer (the Certificate Authority that signed it), the validity period (not-before and not-after timestamps), and the digital signature.
The client checks that the certificate's Common Name or Subject Alternative Names match the hostname it is connecting to. A mismatch results in an immediate rejection regardless of other validity checks — this prevents a valid certificate for one domain from being used to impersonate another.
Next, the client validates the certificate chain. The server certificate is signed by an intermediate CA, which is itself signed by a root CA. The client walks this chain, verifying each signature using the public key of the issuing CA, until it reaches a root CA that is present in its local trust store. If any link in the chain cannot be verified, the connection is rejected.
The client also checks the certificate's validity period. Certificates include explicit not-before and not-after fields; if the current time falls outside this window, validation fails. Additionally, the client may check revocation status using either OCSP (Online Certificate Status Protocol) or a CRL (Certificate Revocation List) to ensure the certificate has not been revoked by its issuer before expiry.
Only after all these checks pass does the client proceed with the TLS handshake, generating session keys using the server's public key from the validated certificate. This entire validation process is what makes HTTPS resistant to man-in-the-middle attacks.
For the broader context of how this fits into connection setup, see TLS Handshake and HTTPS Handshake. The chain of CAs involved is explored in Certificate Authority Chain, and the underlying asymmetric cryptography is explained in Public Key Encryption.