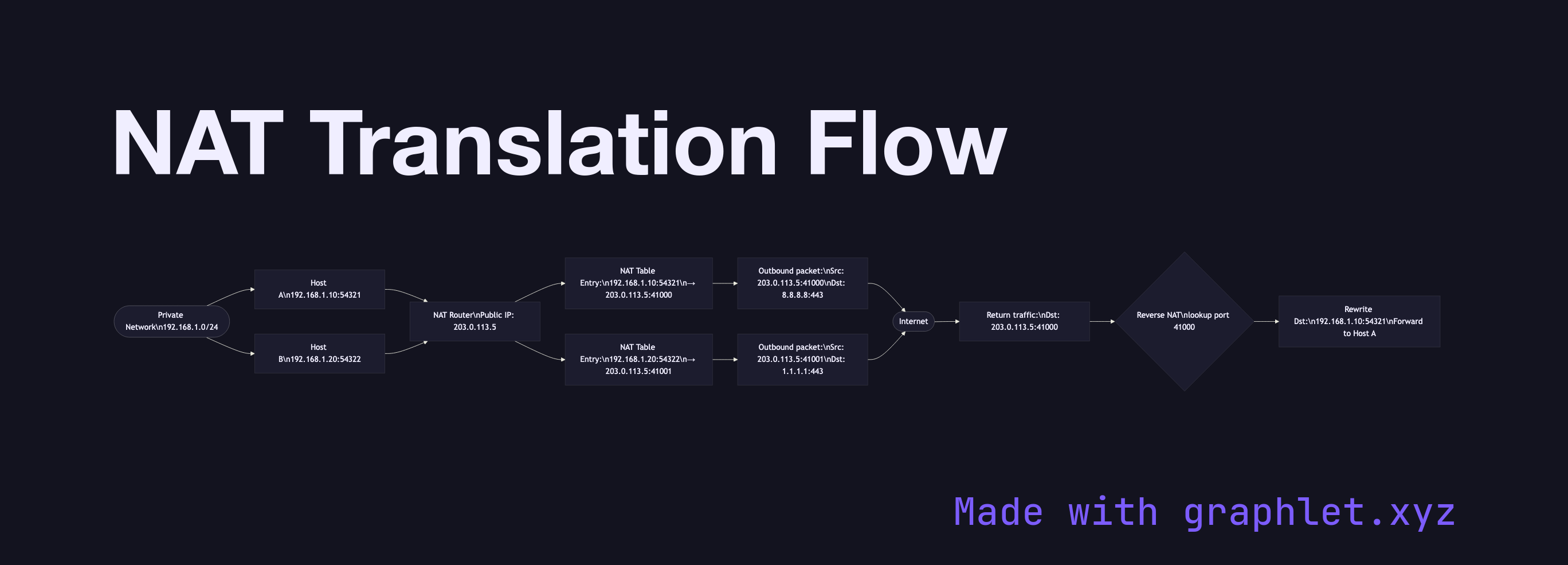
NAT Translation Flow
NAT (Network Address Translation) is the process by which a router or firewall rewrites IP address and port information in packet headers to allow multiple devices on a private network to share a single public IP address for internet communication.
NAT (Network Address Translation) is the process by which a router or firewall rewrites IP address and port information in packet headers to allow multiple devices on a private network to share a single public IP address for internet communication.
IPv4 address exhaustion is the primary driver for NAT. RFC 1918 reserves private address ranges (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) that are not routable on the public internet. NAT bridges private and public address spaces.
NAPT (Network Address and Port Translation): The most common form is "masquerade" NAT, also called NAPT. The NAT device maintains a translation table mapping (private IP, private port) → (public IP, public port). When a private host initiates a connection, the NAT device: 1. Assigns an available public-side port 2. Rewrites the source IP and port in the outbound packet 3. Stores the mapping in the NAT table 4. On return traffic, performs the reverse translation — rewriting the destination IP and port back to the private host's address
Connection Tracking: The NAT table entry is created on the first outbound packet and kept alive as long as traffic flows. Entries time out after inactivity (UDP: typically 30s, TCP: up to hours).
Implications for Developers: NAT is why peer-to-peer connectivity is complex — neither peer can initiate a connection to the other's private IP. Techniques like STUN (for discovering public IP:port), TURN (relaying), and ICE (the combination used by WebRTC) exist to traverse NAT. VPN tunnel setup also involves NAT traversal. Port forwarding explicitly maps an inbound public port to a private host, enabling server operation behind NAT.