VPN Tunnel Setup
A VPN (Virtual Private Network) tunnel is an encrypted, authenticated network connection that creates a private communications channel over a public network, allowing a client to securely access resources as if directly connected to a private network.
A VPN (Virtual Private Network) tunnel is an encrypted, authenticated network connection that creates a private communications channel over a public network, allowing a client to securely access resources as if directly connected to a private network.
VPNs serve two primary use cases: remote access (employees connecting to corporate networks) and site-to-site (connecting two networks, e.g., branch offices or cloud VPCs to on-premises).
IKEv2/IPsec is the most common enterprise VPN protocol stack. WireGuard is a modern alternative with a significantly simpler codebase and faster performance. OpenVPN uses TLS-based tunneling.
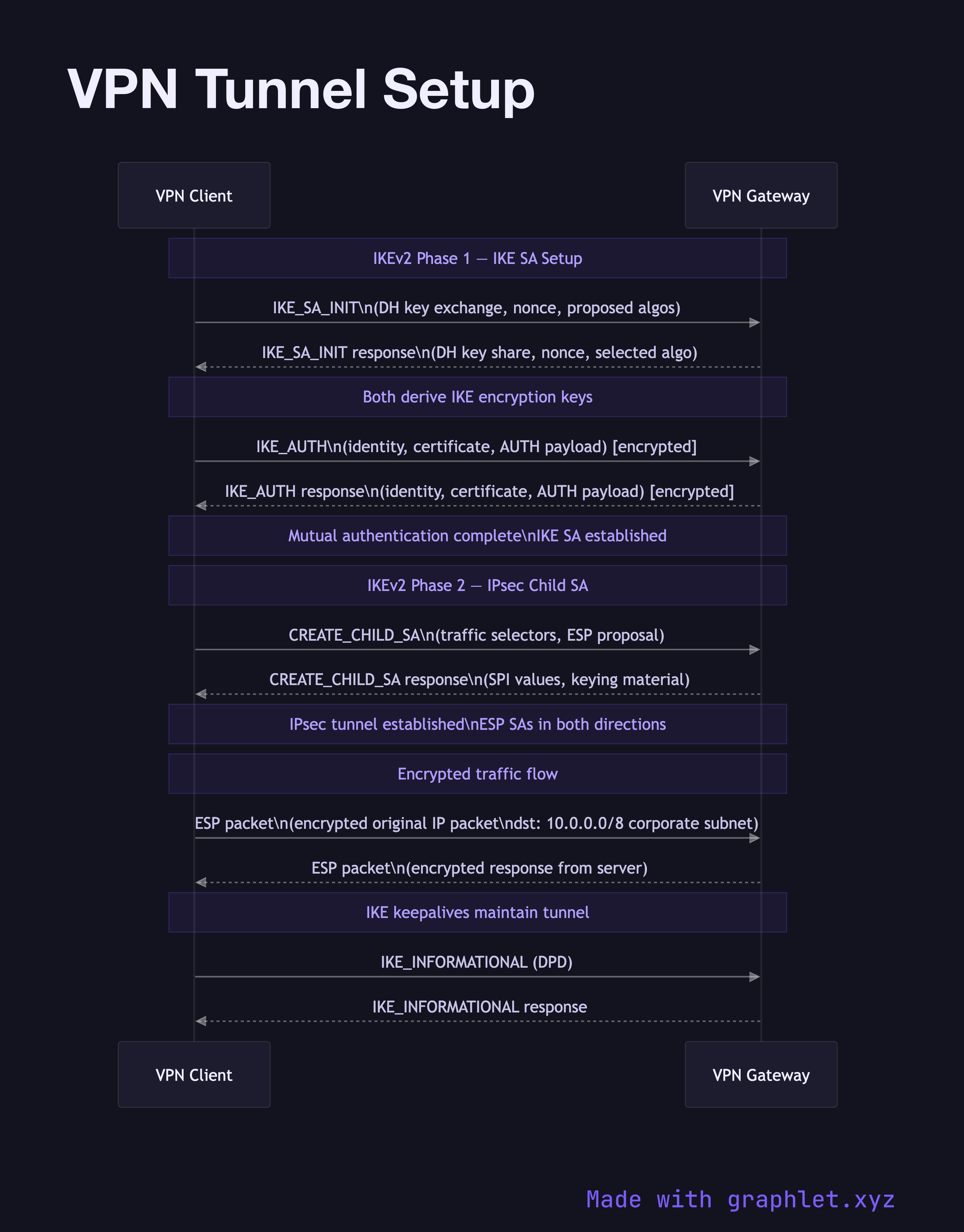
IKE Phase 1 (SA Negotiation): The client and VPN gateway negotiate a secure channel (the IKE Security Association) for key exchange. They authenticate each other using certificates or pre-shared keys and agree on encryption parameters (cipher, hash algorithm, DH group).
IKE Phase 2 (IPsec Tunnel): Using the Phase 1 channel, the two sides negotiate the IPsec Security Associations (SAs) — one for each direction of traffic. The SAs define how traffic is encrypted (ESP: Encapsulating Security Payload) and authenticated.
Traffic Flow: Once the tunnel is established, traffic from the client destined for the corporate network is encapsulated in ESP packets. The ESP header includes a Security Parameter Index (SPI) that identifies the SA, and the payload (the original IP packet) is encrypted.
Split Tunneling: Many VPN configurations use split tunneling, where only traffic to corporate subnets goes through the VPN; internet traffic goes directly. Full-tunnel VPNs route all traffic through the VPN gateway.
NAT Traversal: IPsec has issues traversing NAT because NAT changes the IP header that IPsec integrity-protects. NAT-T (RFC 3947) addresses this by encapsulating ESP inside UDP port 4500.