Security
Content Security Policy Flow
Content Security Policy (CSP) is an HTTP response header that instructs the browser to only load resources (scripts, styles, images, fonts, frames) from sources you explicitly allowlist, providing a strong second line of defense against XSS attacks.
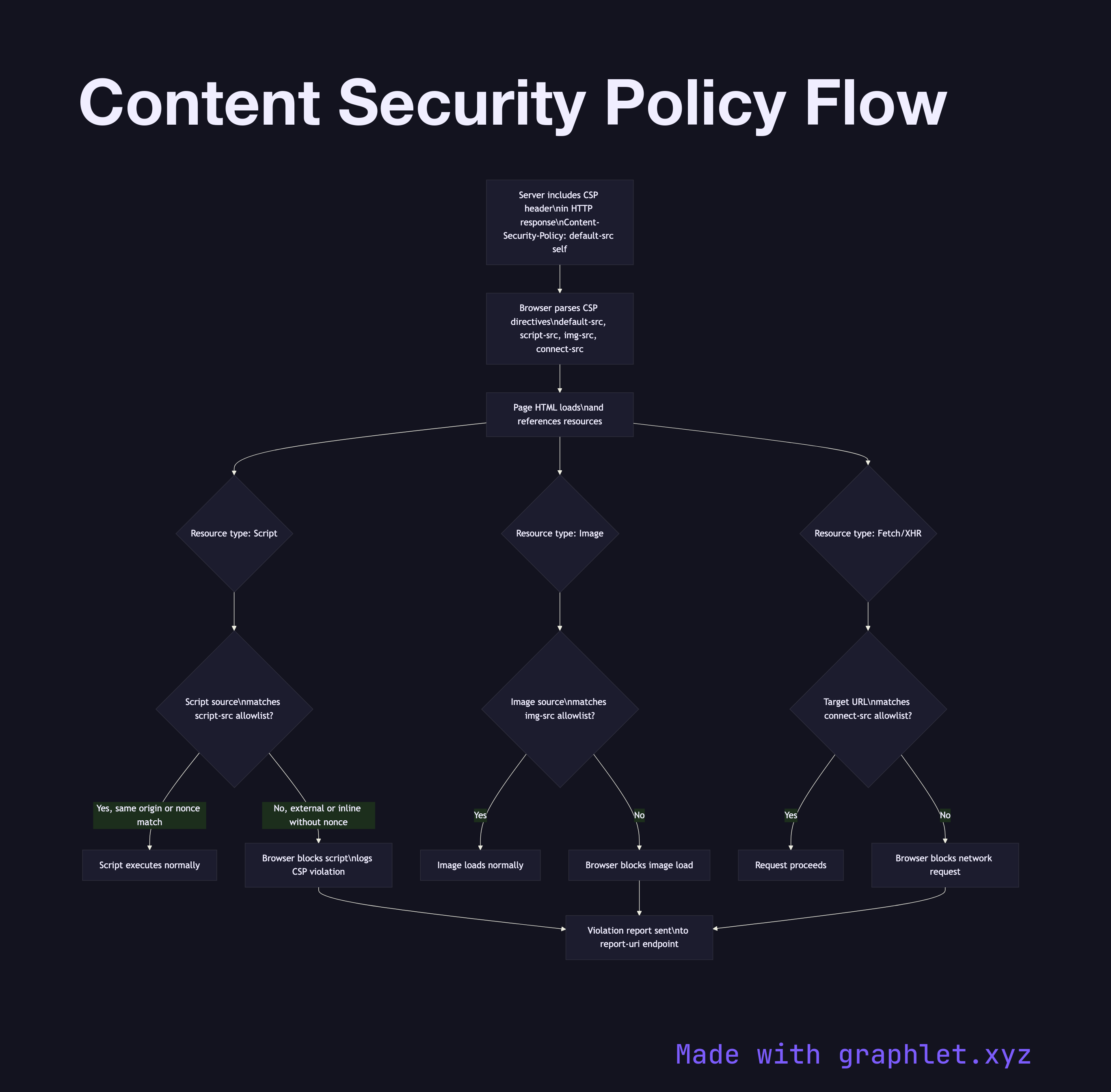
Content Security Policy (CSP) is an HTTP response header that instructs the browser to only load resources (scripts, styles, images, fonts, frames) from sources you explicitly allowlist, providing a strong second line of defense against XSS attacks.
Even if an attacker successfully injects a