Digital Signature Workflow
A digital signature is a cryptographic mechanism that proves a message was created by a specific private key holder (authentication) and has not been modified since it was signed (integrity). Unlike encryption, signing does not conceal the message — it creates verifiable proof of origin.
A digital signature is a cryptographic mechanism that proves a message was created by a specific private key holder (authentication) and has not been modified since it was signed (integrity). Unlike encryption, signing does not conceal the message — it creates verifiable proof of origin.
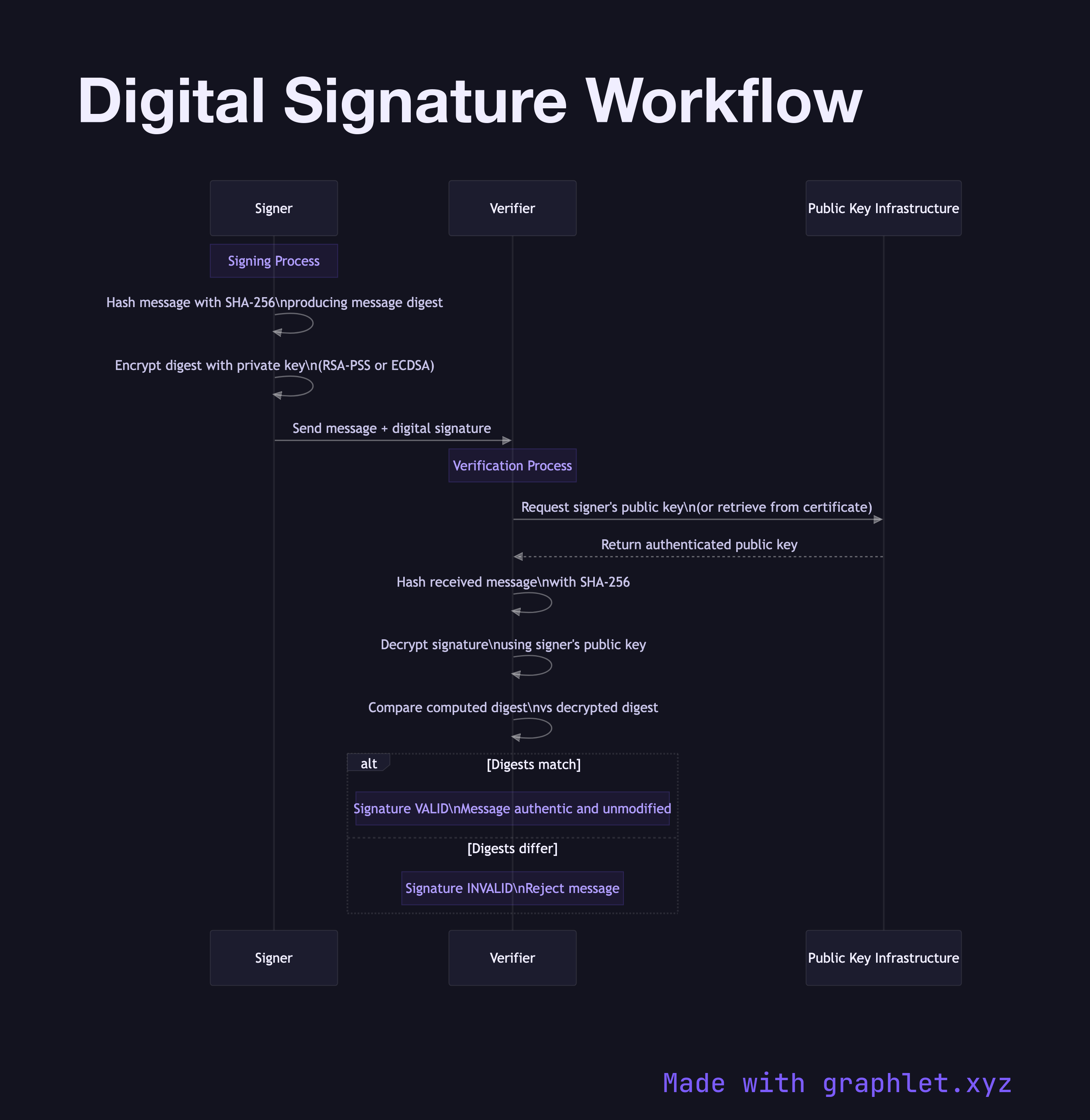
The signing process starts with hashing. The signer runs the message through a cryptographic hash function (SHA-256 or SHA-3) to produce a fixed-size digest. Hashing is deterministic — the same input always produces the same output — and collision-resistant, meaning it is computationally infeasible to find two different inputs that produce the same hash.
The signer then encrypts this hash with their private key using an asymmetric algorithm like RSA-PKCS1v15, RSA-PSS, or ECDSA. This encrypted hash is the digital signature. It is typically appended to the message or transmitted alongside it. The message itself is sent in the clear.
On the verification side, the verifier obtains the signer's public key — from a certificate, a public key server, or out-of-band trust. They run the same hash function on the received message to produce their own digest. They then decrypt the signature using the signer's public key to recover the original digest. If the two digests match, the signature is valid: the message was signed by the private key holder and has not been tampered with since.
This workflow is foundational in TLS certificates (CAs sign certificates with their private keys), JWT tokens (issuers sign the header and payload), code signing (publishers sign software packages), and git commit signing. See HMAC Signing Process for a symmetric alternative that is faster but requires a shared secret, and Certificate Authority Chain for how CAs use signatures to establish a chain of trust.