Public Key Encryption
Public key encryption (asymmetric encryption) is a cryptographic system that uses a mathematically linked key pair — a public key that anyone can use to encrypt data, and a private key that only the owner can use to decrypt it.
Public key encryption (asymmetric encryption) is a cryptographic system that uses a mathematically linked key pair — a public key that anyone can use to encrypt data, and a private key that only the owner can use to decrypt it.
Unlike symmetric encryption where both parties share the same secret key, asymmetric encryption solves the key distribution problem: you can publish your public key openly without any security risk, because data encrypted with it can only be decrypted by the corresponding private key, which never leaves your possession.
The mathematical foundation relies on trapdoor functions — operations that are easy to compute in one direction but computationally infeasible to reverse without specific information. RSA uses the difficulty of factoring large integers; elliptic-curve cryptography (ECC) uses the discrete logarithm problem on elliptic curves. In practice, RSA-2048 and RSA-4096 are common for legacy systems, while ECDSA and ECDH with P-256 or Curve25519 are preferred in modern protocols like TLS 1.3 for their smaller key sizes and faster operations.
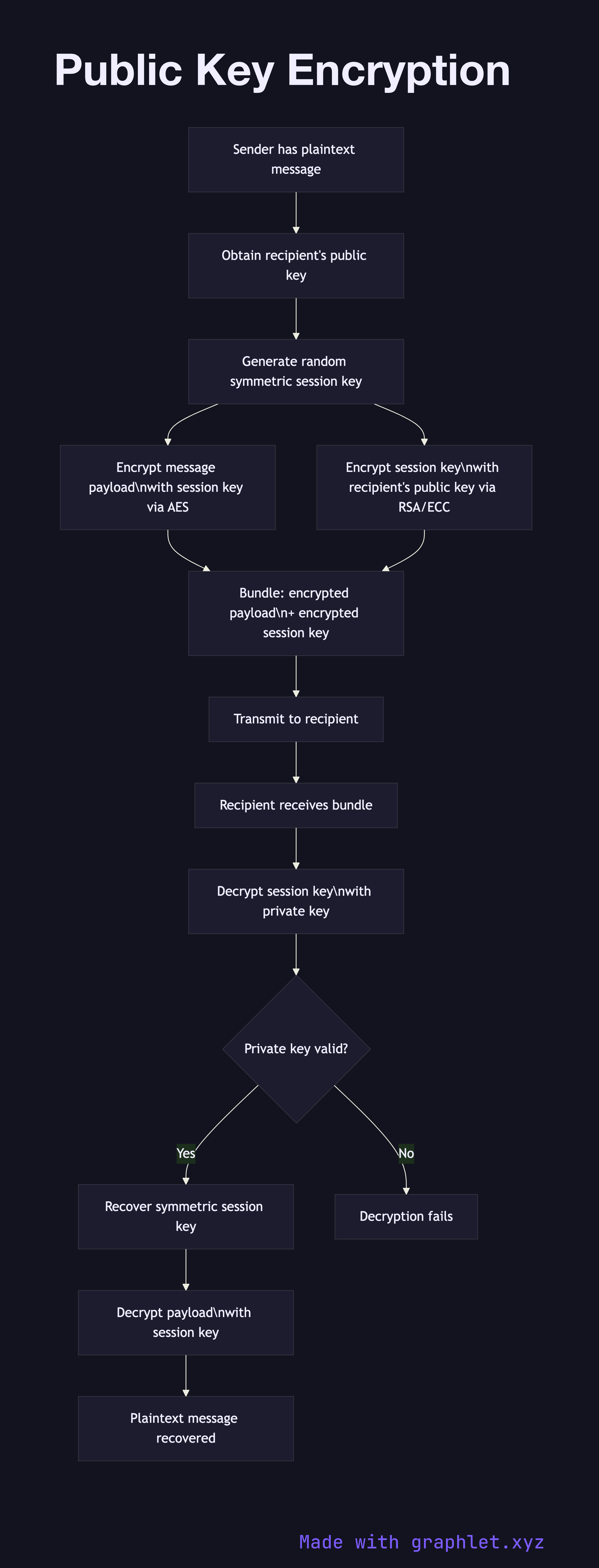
The encryption workflow begins with the sender obtaining the recipient's authentic public key — typically from a TLS certificate or a key server. The sender generates a random symmetric session key, encrypts the actual message payload with this session key using AES (a symmetric cipher), then encrypts the session key itself with the recipient's public key. This hybrid approach is used because asymmetric encryption is orders of magnitude slower than symmetric encryption and cannot efficiently handle large payloads.
The recipient uses their private key to decrypt the session key, then uses the session key to decrypt the message. This is exactly how TLS key exchange works: the client and server use asymmetric cryptography to establish a shared symmetric session key, then all subsequent data is encrypted symmetrically.
Public key encryption also underpins digital signatures — see Digital Signature Workflow for how private keys sign data that anyone with the public key can verify. The role of public keys in TLS is covered in TLS Certificate Validation.