Refresh Token Rotation
Refresh token rotation is a security pattern that extends the lifespan of a user's authenticated session without requiring them to log in again, while significantly reducing the risk of refresh token theft.
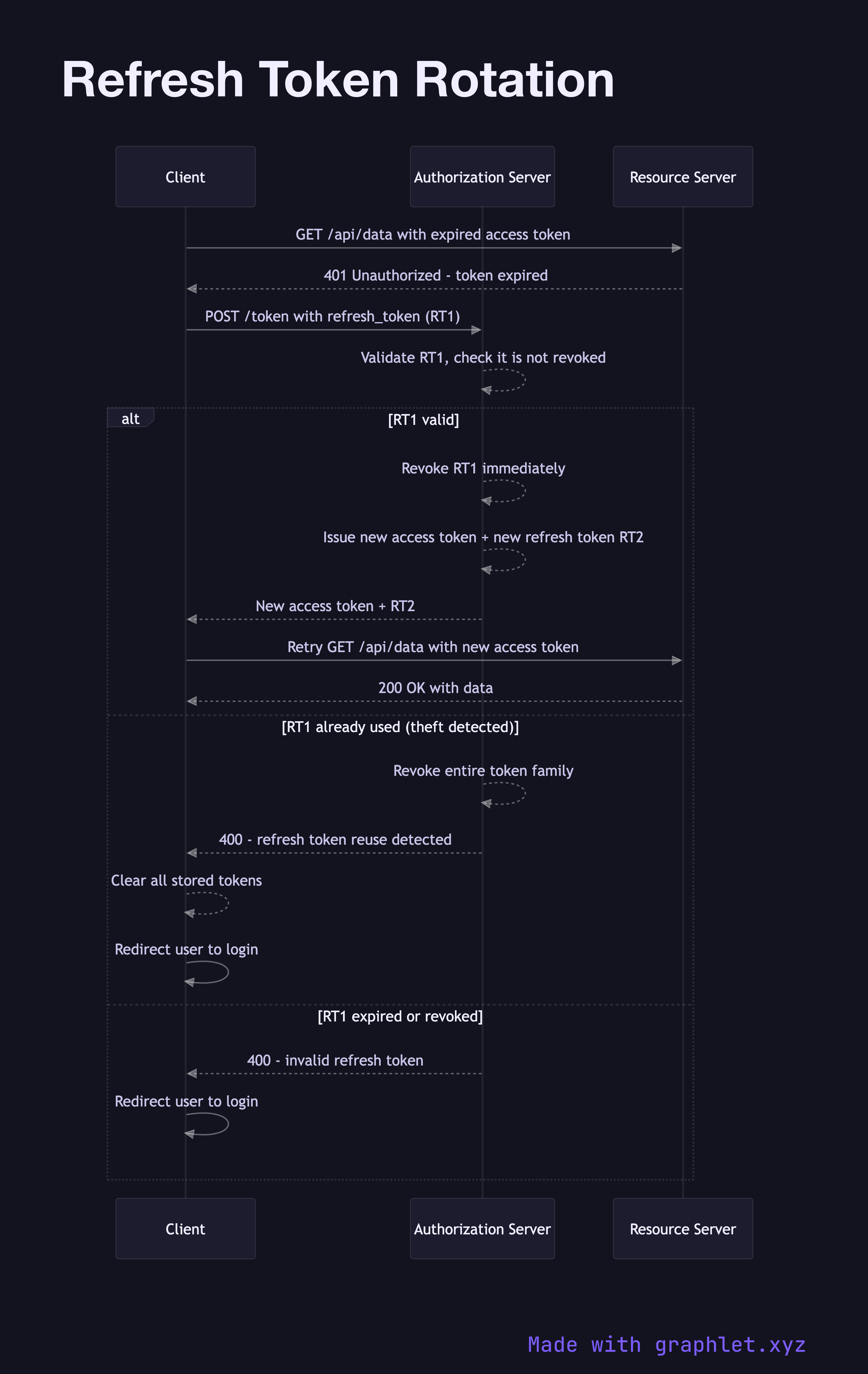
Refresh token rotation is a security pattern that extends the lifespan of a user's authenticated session without requiring them to log in again, while significantly reducing the risk of refresh token theft.
Access tokens are kept intentionally short-lived — typically 5 to 60 minutes — to limit the damage window if one is intercepted. When an access token expires, the client uses a refresh token (a long-lived, opaque credential stored securely) to request a new access token without re-prompting the user for credentials.
In simple refresh (without rotation), the same refresh token can be reused indefinitely until it expires. This creates a long-lived secret that, if stolen, gives an attacker persistent access until the token is explicitly revoked. Refresh token rotation eliminates this risk: every time the client exchanges a refresh token for new tokens, the authorization server issues a brand-new refresh token and immediately invalidates the old one.
The critical security property of rotation is automatic theft detection: if an attacker steals a refresh token and uses it after the legitimate client has already rotated it, the authorization server detects a reuse of an already-invalidated token. The server responds by revoking the entire token family — forcing re-authentication. This means the legitimate user loses their session, but the attack is contained.
Clients must handle the rotation carefully: if a network failure causes the token response to be lost after the server has already invalidated the old token, the client may get into a broken state. Robust implementations include retry logic and fallback to re-authentication. Refresh tokens are typically stored in httpOnly cookies or secure storage (never localStorage) to prevent XSS theft.
For managing token invalidation explicitly, see Token Revocation Flow. The full lifecycle of access tokens is covered in JWT Authentication Flow.