Magic Link Login
Magic link login is a passwordless authentication pattern where users log in by clicking a one-time URL sent to their email address. Possession of the email account serves as the proof of identity, eliminating the need for users to remember and manage passwords.
Magic link login is a passwordless authentication pattern where users log in by clicking a one-time URL sent to their email address. Possession of the email account serves as the proof of identity, eliminating the need for users to remember and manage passwords.
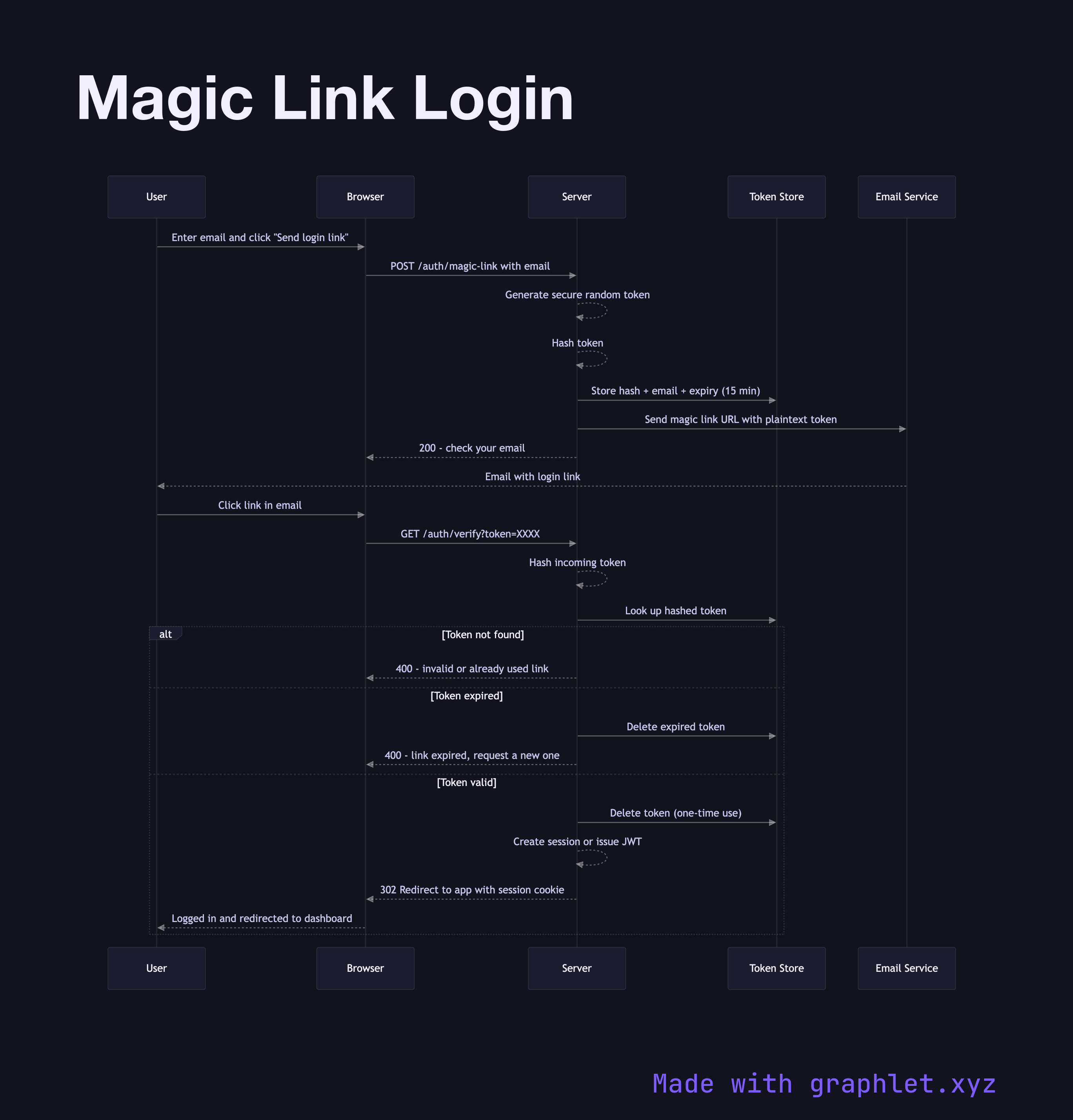
The flow begins when a user enters their email and requests a login link. The server generates a cryptographically random single-use token, hashes it for storage, and stores the hash alongside the user's email and an expiry timestamp (typically 10–30 minutes). The server embeds the plaintext token in a login URL and sends it via email. The user's browser is held at a "check your email" screen.
When the user clicks the link in their email client, the browser sends the token to the server. The server hashes the incoming token, looks it up in the store, checks the expiry, and — crucially — deletes the token record immediately upon successful lookup. This one-time-use property means that even if someone later intercepts the email, the link is already spent. After validation, the server creates a new session or issues a JWT and redirects the user into the application.
Security considerations are important. The magic link flow relies entirely on email security as its authentication factor — if the user's email is compromised, so is their app account. Links must expire quickly, and clicking the link from a different browser or device than expected is a potential phishing signal (some implementations display a warning or require a secondary confirm). Rate limiting on the link request endpoint prevents email flooding.
Magic links trade password management complexity for dependency on reliable email delivery. They work especially well for B2B SaaS apps and developer tools where users check email frequently. Compare the Password Reset Flow, which follows essentially the same token mechanics. Social Login Flow is another passwordless option.