Password Reset Flow
A password reset flow allows users to regain access to their account when they've forgotten their password. Implementing it securely is critical: a poorly designed reset flow can become a backdoor into user accounts.
A password reset flow allows users to regain access to their account when they've forgotten their password. Implementing it securely is critical: a poorly designed reset flow can become a backdoor into user accounts.
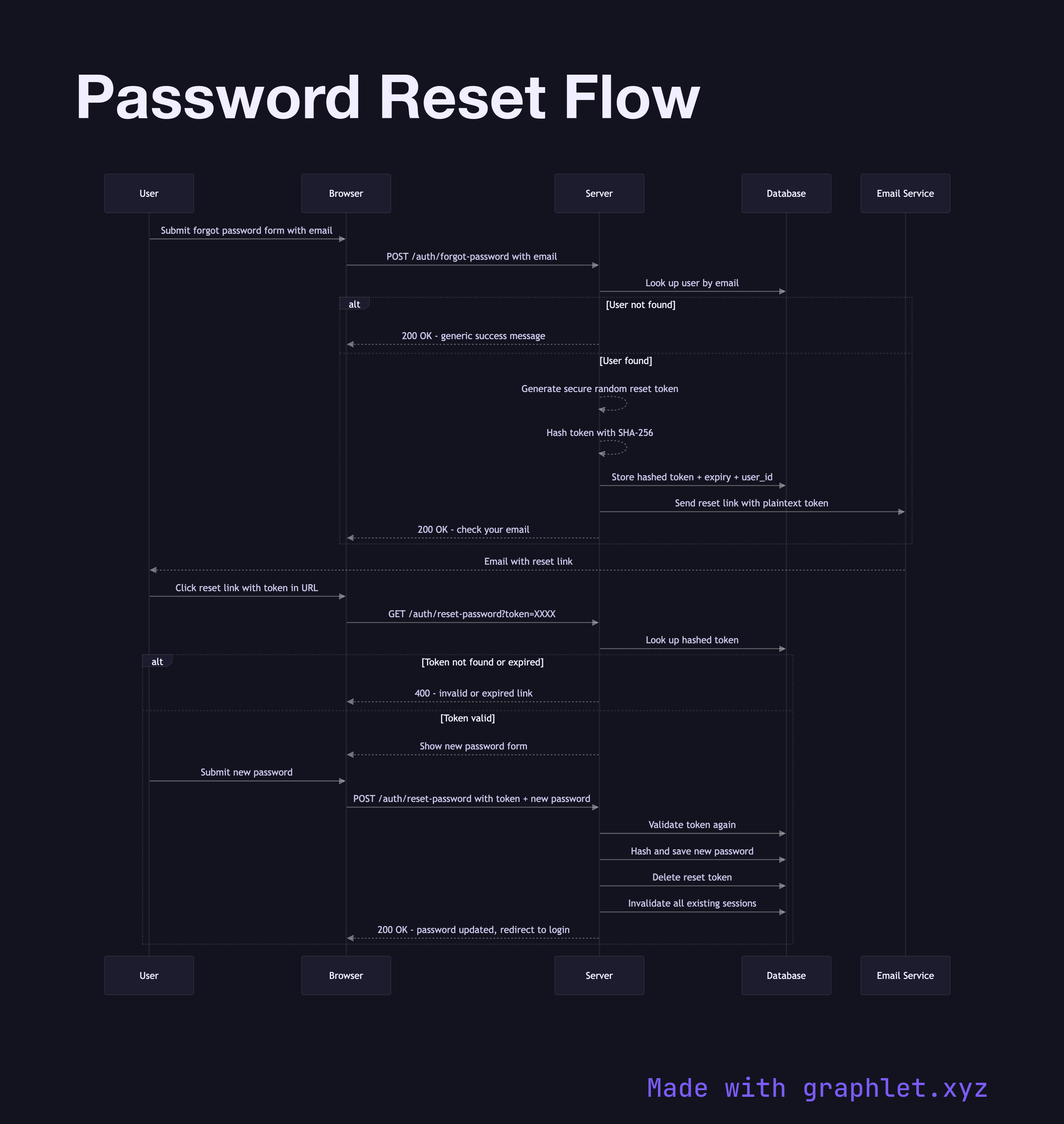
The flow begins when a user clicks "Forgot Password" and submits their email address. To prevent user enumeration — leaking whether an account exists — the server responds with the same message regardless of whether the email is registered: "If an account with that email exists, a reset link has been sent." This prevents attackers from probing which emails are registered.
Internally, if the email matches an account, the server generates a cryptographically random reset token — typically 32 bytes from a secure random source, encoded as hex or Base64. The token is hashed (using a fast hash like SHA-256) and stored in the database alongside the user ID and an expiry timestamp (15–60 minutes is common). The plaintext token is embedded in a reset URL and sent by email.
When the user clicks the link, the server extracts the token from the URL, hashes it, looks up the hash in the database, and checks the expiry. If valid, the user is presented with a form to enter a new password. On submission, the server validates the token again (preventing race conditions), hashes the new password using a proper password hashing algorithm (bcrypt, Argon2, or scrypt), updates the user's password, and immediately invalidates the reset token — as well as all existing sessions for that user. This last step is critical: if an attacker triggered the reset, forcing all sessions to expire blocks any unauthorized access already in progress.
For passwordless alternatives that eliminate the reset problem entirely, compare Magic Link Login. Adding Two Factor Authentication alongside passwords is a complementary security layer.