OAuth2 Authorization Code Flow
The OAuth2 Authorization Code Flow is the most secure and widely used OAuth2 grant type, designed for applications that can keep a client secret confidential — typically server-side web apps and backend services acting on behalf of a user.
The OAuth2 Authorization Code Flow is the most secure and widely used OAuth2 grant type, designed for applications that can keep a client secret confidential — typically server-side web apps and backend services acting on behalf of a user.
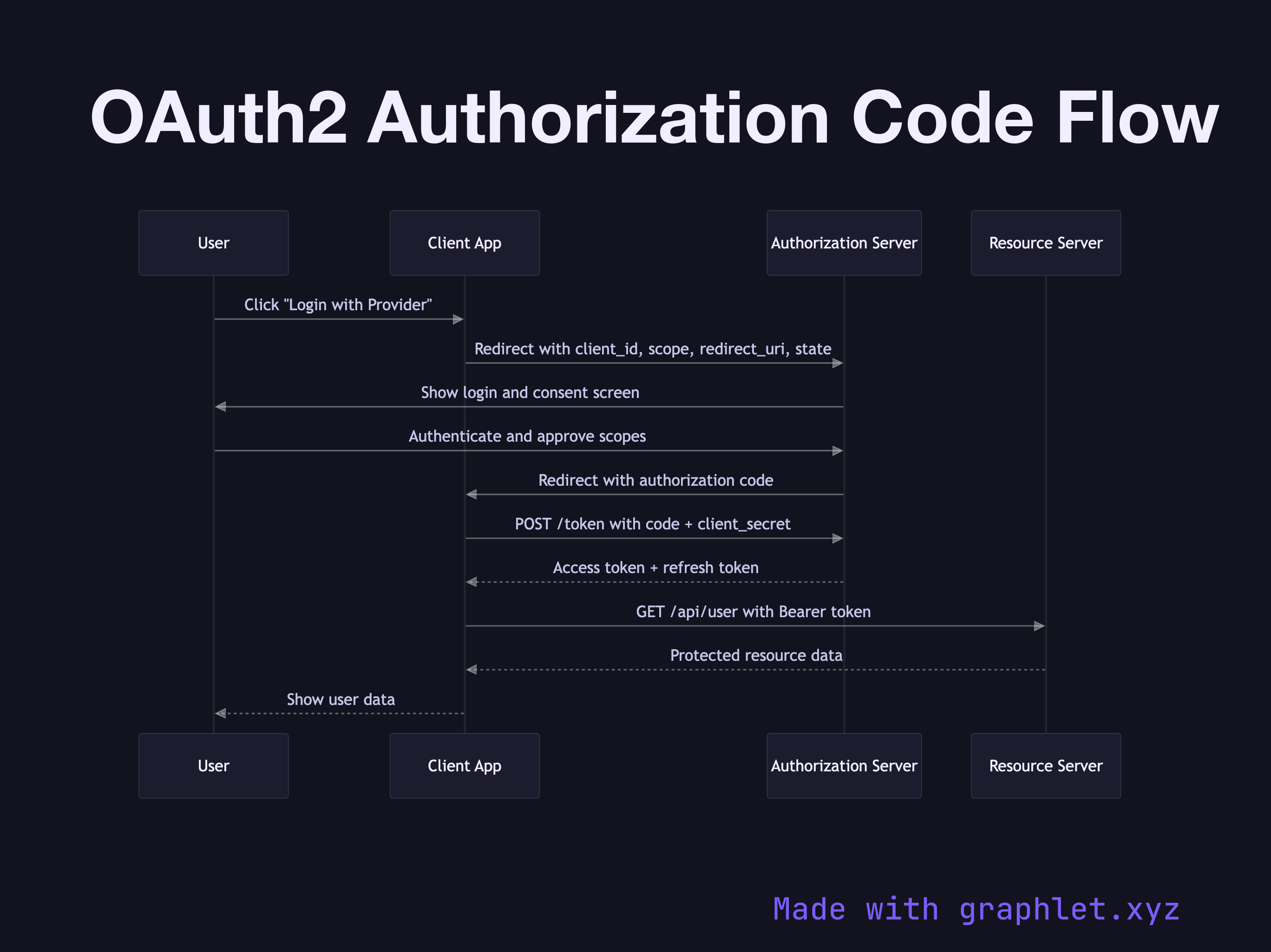
The flow begins when a user initiates login. The client application redirects the browser to the authorization server with several query parameters: client_id to identify the app, redirect_uri specifying where to send the user after authorization, scope listing the requested permissions, state (a random nonce to prevent CSRF attacks), and response_type=code. The authorization server presents a login form and a consent screen describing what the app wants to access.
Once the user authenticates and approves, the authorization server redirects back to the client's redirect_uri with a short-lived authorization code in the query string. This code is single-use and typically expires in 60–600 seconds. Critically, the code is passed through the browser, so it is visible in browser history and logs — but it is useless without the client secret.
The client immediately exchanges the authorization code for tokens by making a back-channel POST to the /token endpoint, sending the code along with its client_id and client_secret. This server-to-server call is never visible to the browser. The authorization server validates the code and issues an access token (short-lived, used to call APIs) and a refresh token (long-lived, used to obtain new access tokens without re-prompting the user).
The client stores the tokens, then calls the resource server (your API) using the access token as a Bearer header. The resource server validates the token — either by introspection or by verifying its JWT signature — and returns the protected data.
This flow is the foundation for OpenID Connect Flow, which adds an id_token to carry user identity. For background services without user interaction, see OAuth2 Client Credentials Flow. Managing token lifetimes in production requires Refresh Token Rotation. The full access token lifecycle, including validation, is covered in JWT Authentication Flow.