OpenID Connect Flow
OpenID Connect (OIDC) is an identity layer built on top of OAuth2 that lets applications verify the identity of a user and obtain basic profile information. While OAuth2 alone answers "is this user authorized to access this resource?", OIDC adds the answer to "who is this user?"
OpenID Connect (OIDC) is an identity layer built on top of OAuth2 that lets applications verify the identity of a user and obtain basic profile information. While OAuth2 alone answers "is this user authorized to access this resource?", OIDC adds the answer to "who is this user?"
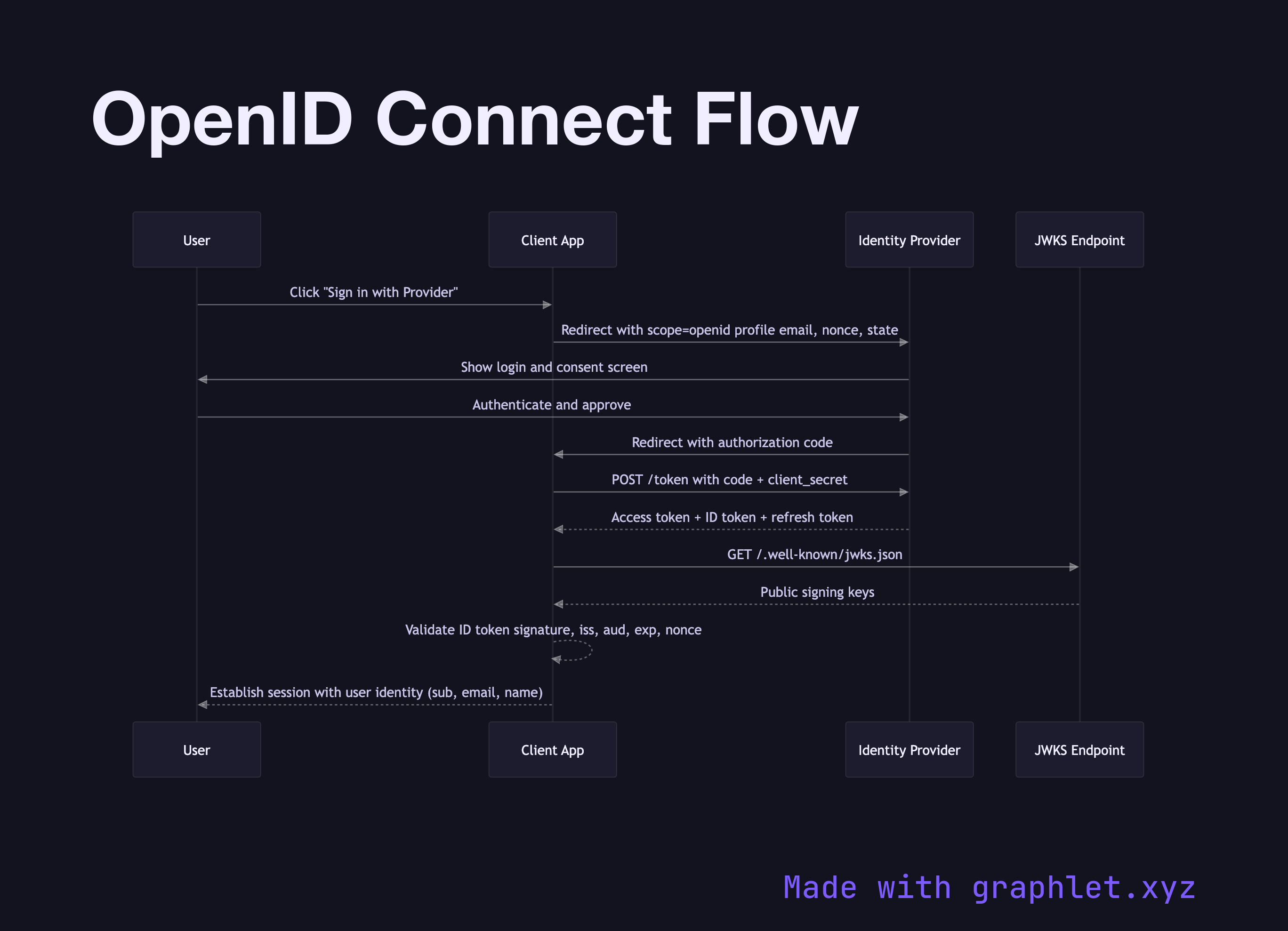
The OIDC flow looks nearly identical to the OAuth2 Authorization Code Flow, with one key addition: the client requests the openid scope, which instructs the authorization server to include an ID token alongside the access token.
The flow begins with a browser redirect to the identity provider (IdP). The client includes scope=openid profile email (and optionally other standard scopes) plus a nonce — a random value embedded in the authorization request and later verified inside the ID token to prevent replay attacks. After the user authenticates and consents, the IdP redirects back with an authorization code.
The client exchanges the code for three tokens: an access token (for calling APIs), a refresh token (for long-lived sessions), and an ID token. The ID token is a JWT whose payload contains claims about the user: sub (a stable unique user identifier), iss (the issuer URL), aud (the client_id), exp (expiry), iat (issued at), nonce, plus any requested profile claims like name, email, and picture.
The client validates the ID token's signature against the IdP's public keys (fetched from the JWKS endpoint), verifies iss, aud, exp, and nonce, and then trusts the sub claim as the user's identity. This eliminates the need for a separate /userinfo call in most cases.
OIDC is the standard powering Social Login Flow via Google, GitHub, and Apple, and it underpins most modern SSO Architecture implementations. Enterprise deployments often compare it against SAML Authentication Flow, which solves the same problem with XML-based assertions.