SAML Authentication Flow
Security Assertion Markup Language (SAML) 2.0 is an XML-based standard for federated identity and single sign-on, widely used in enterprise environments to allow employees to access multiple applications using their corporate credentials.
Security Assertion Markup Language (SAML) 2.0 is an XML-based standard for federated identity and single sign-on, widely used in enterprise environments to allow employees to access multiple applications using their corporate credentials.
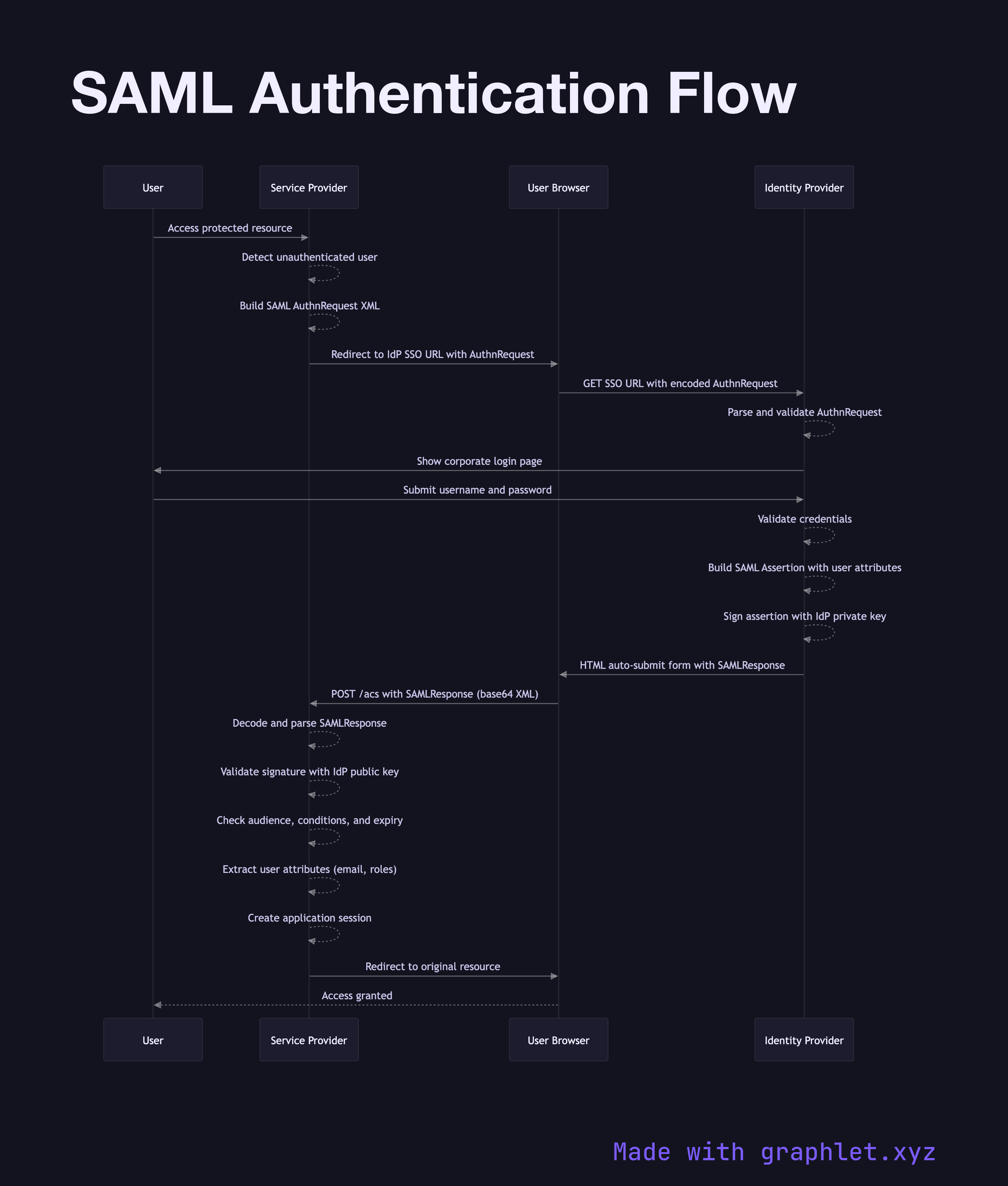
SAML defines three roles: the User (the human logging in), the Service Provider (SP — the application being accessed), and the Identity Provider (IdP — the corporate identity system, such as Okta, Azure AD, or ADFS). The trust relationship between SP and IdP is established in advance by exchanging metadata: the SP registers its entityID, ACS URL (Assertion Consumer Service), and accepted signing certificates with the IdP; the IdP registers its entityID, SSO URL, and public key with the SP.
The SP-initiated flow begins when a user attempts to access a protected resource. The SP detects that the user is not authenticated and constructs a SAML AuthnRequest — an XML document identifying the SP and the requested resource. This request is typically encoded, compressed, and embedded in a redirect URL that sends the user's browser to the IdP's SSO endpoint.
The IdP presents a login page (or transparently authenticates the user if they have an active SSO session). After successful authentication, the IdP constructs a SAML Assertion — an XML document containing the user's identity attributes (email, name, roles), the authentication event details, and conditions (valid time window, intended audience). The IdP signs the assertion with its private key and sends it back to the SP's ACS URL via an HTTP POST from the browser (the assertion travels through the user's browser, not directly between servers).
The SP validates the assertion signature using the IdP's public key, checks the audience and time conditions, extracts the user attributes, and creates an application session. This pattern is the basis for enterprise SSO Architecture. Modern greenfield projects tend to favor OpenID Connect Flow over SAML, but SAML remains dominant in legacy enterprise environments.