Chord Protocol
Chord is a scalable distributed lookup protocol that maps keys to responsible nodes in an N-node ring using consistent hashing, guaranteeing that any key can be resolved in O(log N) hops by each node maintaining a routing table (finger table) of only O(log N) entries.
Chord is a scalable distributed lookup protocol that maps keys to responsible nodes in an N-node ring using consistent hashing, guaranteeing that any key can be resolved in O(log N) hops by each node maintaining a routing table (finger table) of only O(log N) entries.
Chord assigns both nodes and keys an m-bit identifier (typically m = 160 using SHA-1). Nodes are arranged in a logical ring ordered by their identifiers. Each key is stored on the first node whose identifier is greater than or equal to the key's hash — called the key's successor.
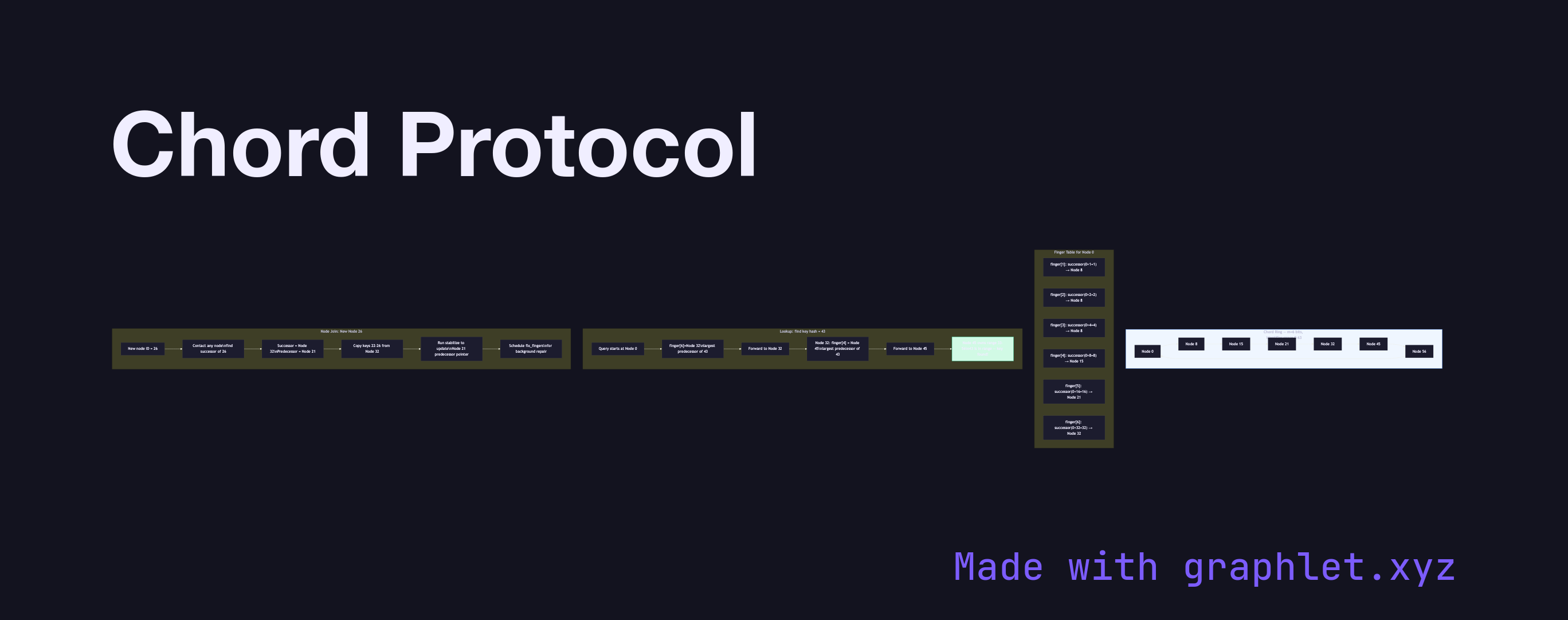
Finger Table: Each node n maintains m finger table entries. The i-th finger of node n is the first node that succeeds n + 2^(i−1) in the ring. This table allows each routing step to skip roughly half the remaining arc, converging in O(log N) hops rather than the O(N) hops of a simple predecessor/successor chain.
Lookup: To find the node responsible for key k, a node checks its finger table for the largest predecessor of k and forwards the query there. The receiving node repeats the process until a node's successor owns k.
Stabilization: Chord uses a periodic stabilization protocol to maintain correct successor and predecessor pointers as nodes join and leave. A joining node locates its successor, copies the relevant key range, and notifies its neighbors. The fix_fingers routine repairs stale finger table entries in the background.
Replication and Failure: Chord itself is a lookup layer; replication is handled at the application level by storing keys on the successor list (the next r nodes in the ring). If a node fails, its successor takes over its key range. See Distributed Hash Table for the general DHT model, and Gossip Protocol for how membership changes propagate efficiently across the ring.