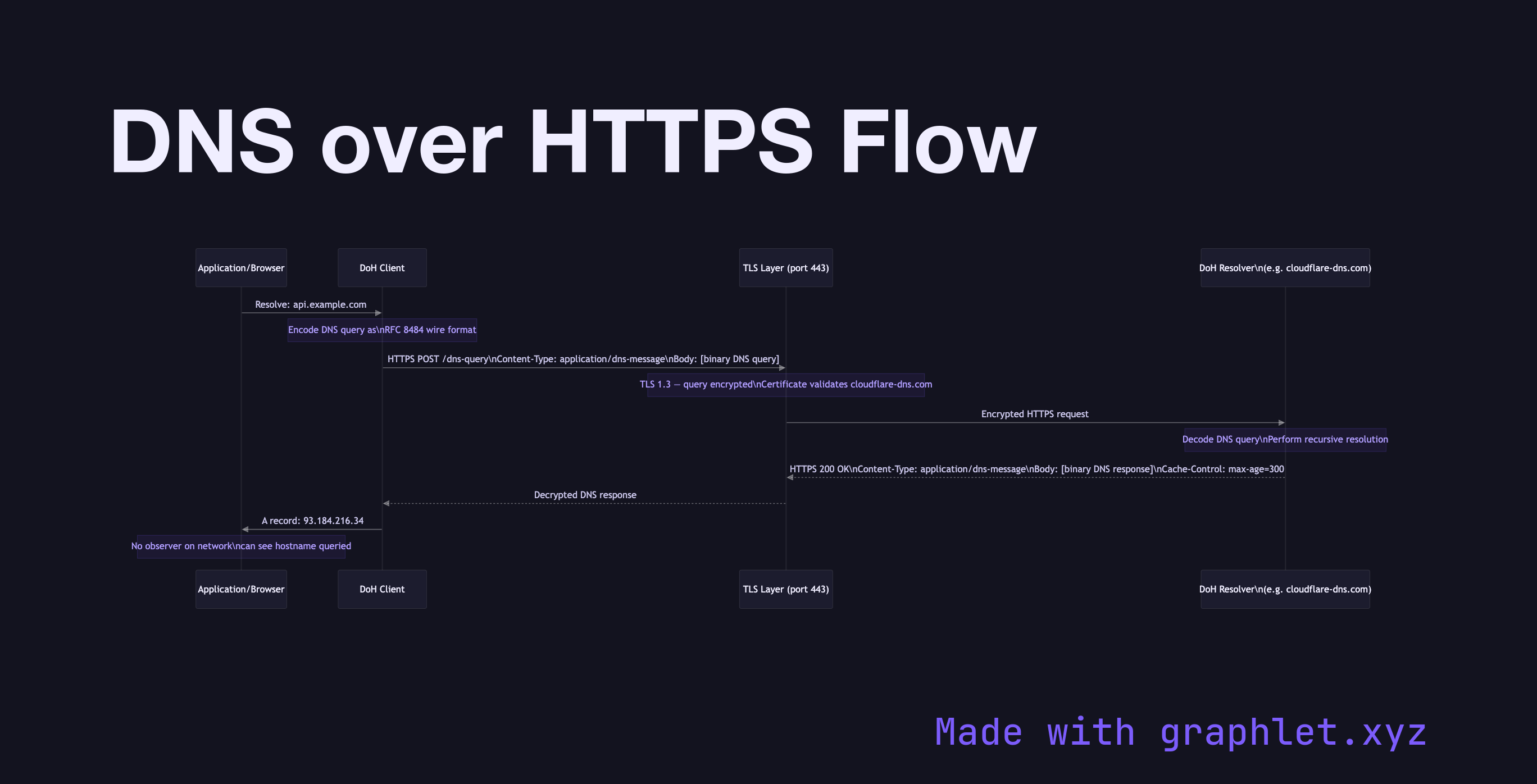
DNS over HTTPS Flow
DNS over HTTPS (DoH, RFC 8484) is a protocol that encrypts DNS queries and responses by encapsulating them inside HTTPS requests, preventing eavesdropping and manipulation of DNS traffic by network intermediaries.
DNS over HTTPS (DoH, RFC 8484) is a protocol that encrypts DNS queries and responses by encapsulating them inside HTTPS requests, preventing eavesdropping and manipulation of DNS traffic by network intermediaries.
Traditional DNS uses plaintext UDP or TCP on port 53. This means every DNS query you make — every hostname you look up — is visible to your ISP, network operator, or anyone who can observe your traffic. DoH addresses this privacy gap.
How DoH Works: Instead of sending a DNS query to a resolver on port 53, the client sends an HTTPS request to a DoH-capable resolver (e.g., https://cloudflare-dns.com/dns-query or https://dns.google/dns-query). The DNS query is encoded in binary DNS message format (wire format) and sent as the body of an HTTP POST request (or base64url-encoded as a GET parameter).
Transport: DoH uses standard HTTPS over TLS 1.3. This means the DNS query is encrypted, authenticated, and protected by TLS certificate validation — identical security properties to any other HTTPS request. No special ports are needed; DoH traffic is indistinguishable from regular HTTPS.
Browser Implementation: Firefox and Chrome support DoH natively, allowing browsers to use a trusted DoH resolver regardless of the OS-configured DNS server. This can bypass ISP DNS hijacking but also bypasses enterprise DNS policies (a point of contention in corporate environments).
Comparison with DoT: DNS over TLS (DoT, port 853) achieves similar privacy but uses a dedicated port that's easier to block or monitor. DoH's use of port 443 makes it harder to selectively block while avoiding performance drawbacks.
Caching and Performance: DoH responses include standard HTTP caching headers. HTTP/2 multiplexing (see HTTP/2 Multiplexing) allows multiple DNS queries over a single HTTPS connection.