DNS over TLS Flow
DNS over TLS (DoT, RFC 7858) is a protocol that encrypts DNS queries and responses by establishing a TLS session on a dedicated port (853), preventing eavesdropping and modification of DNS traffic while maintaining the standard DNS wire format.
DNS over TLS (DoT, RFC 7858) is a protocol that encrypts DNS queries and responses by establishing a TLS session on a dedicated port (853), preventing eavesdropping and modification of DNS traffic while maintaining the standard DNS wire format.
Like DNS over HTTPS, DoT solves the fundamental privacy problem with traditional DNS: plaintext queries on port 53 reveal every hostname you look up to anyone observing the network. DoT and DoH achieve similar privacy guarantees but differ in implementation.
Port 853: DoT operates on TCP port 853, which is dedicated exclusively to encrypted DNS. This makes DoT easy to identify and either allow or block at the network level — an advantage for enterprise administrators who want to enforce specific DoT resolver usage, and a disadvantage in environments where encrypted DNS is actively blocked.
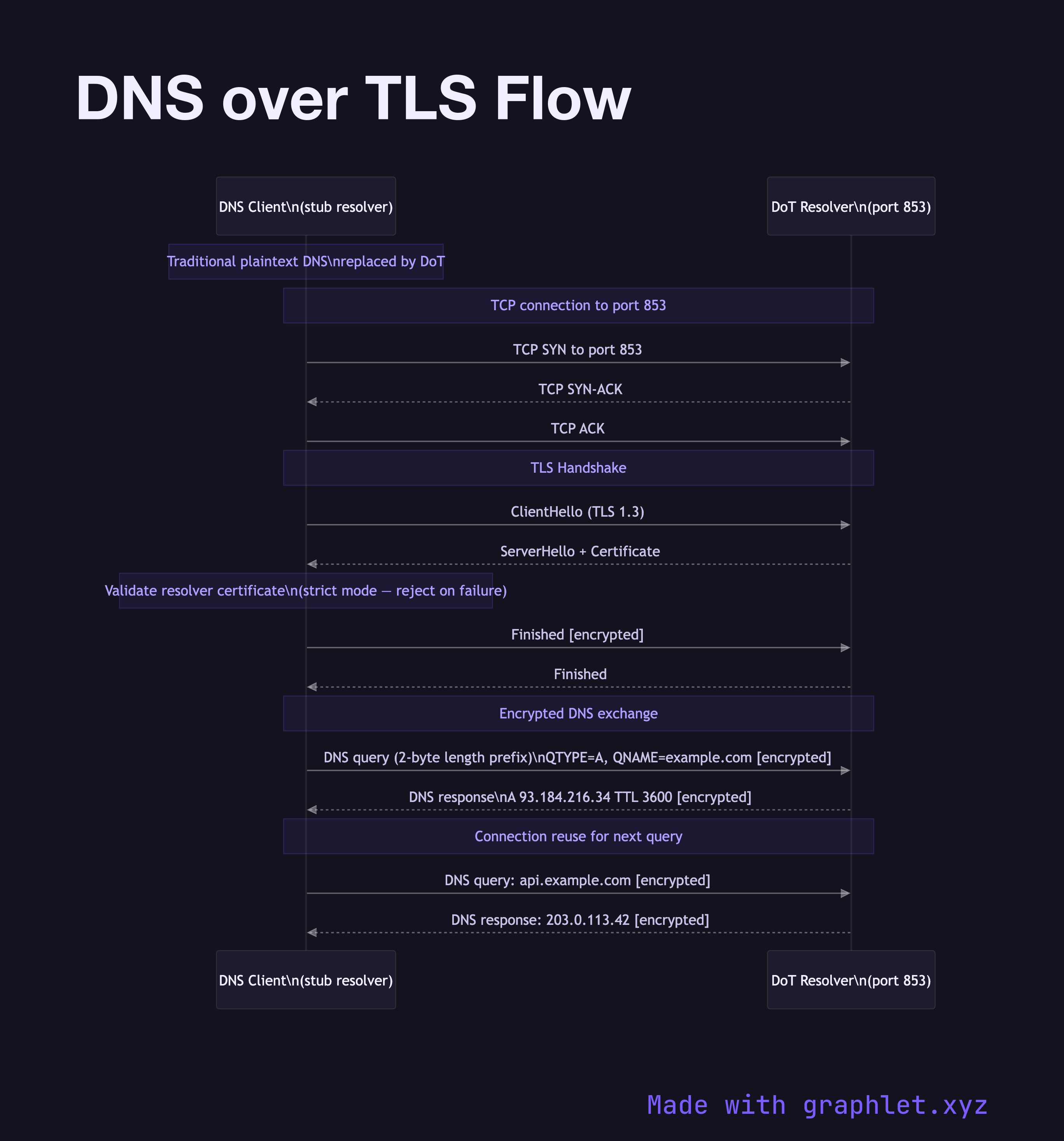
Protocol Flow: The client opens a TCP connection to the DoT resolver on port 853, then performs a standard TLS handshake to authenticate the resolver (via X.509 certificate) and establish an encrypted channel. DNS queries are then sent in the standard DNS wire format (RFC 1035), with a 2-byte length prefix added (since DNS over TCP requires length framing, unlike UDP).
Connection Reuse: DoT explicitly encourages connection reuse. After authentication, multiple DNS queries can be sent over the same TLS connection, amortizing the connection setup cost. This is analogous to how HTTP keep-alive works.
Strict vs. Opportunistic Mode: In strict mode, the client validates the DoT server's certificate against a pinned or system-trusted CA — if validation fails, DNS resolution fails entirely. In opportunistic mode, encryption is used if available but falls back to plaintext on failure, providing weaker privacy guarantees.
Comparison with DoH: DoH sends DNS queries disguised as HTTPS traffic on port 443, making it harder to block without affecting regular web browsing. DoT uses a distinct port, making it more transparent and manageable in enterprise environments.