Proxy Server Flow
A forward proxy server is an intermediary that sits between client devices and the internet, forwarding outbound requests on behalf of clients, enabling centralized access control, traffic inspection, caching, and anonymization.
A forward proxy server is an intermediary that sits between client devices and the internet, forwarding outbound requests on behalf of clients, enabling centralized access control, traffic inspection, caching, and anonymization.
The key distinction: a forward proxy acts on behalf of clients (hiding client identities from servers), while a reverse proxy acts on behalf of servers (hiding server details from clients). See Reverse Proxy Request Flow for the contrast.
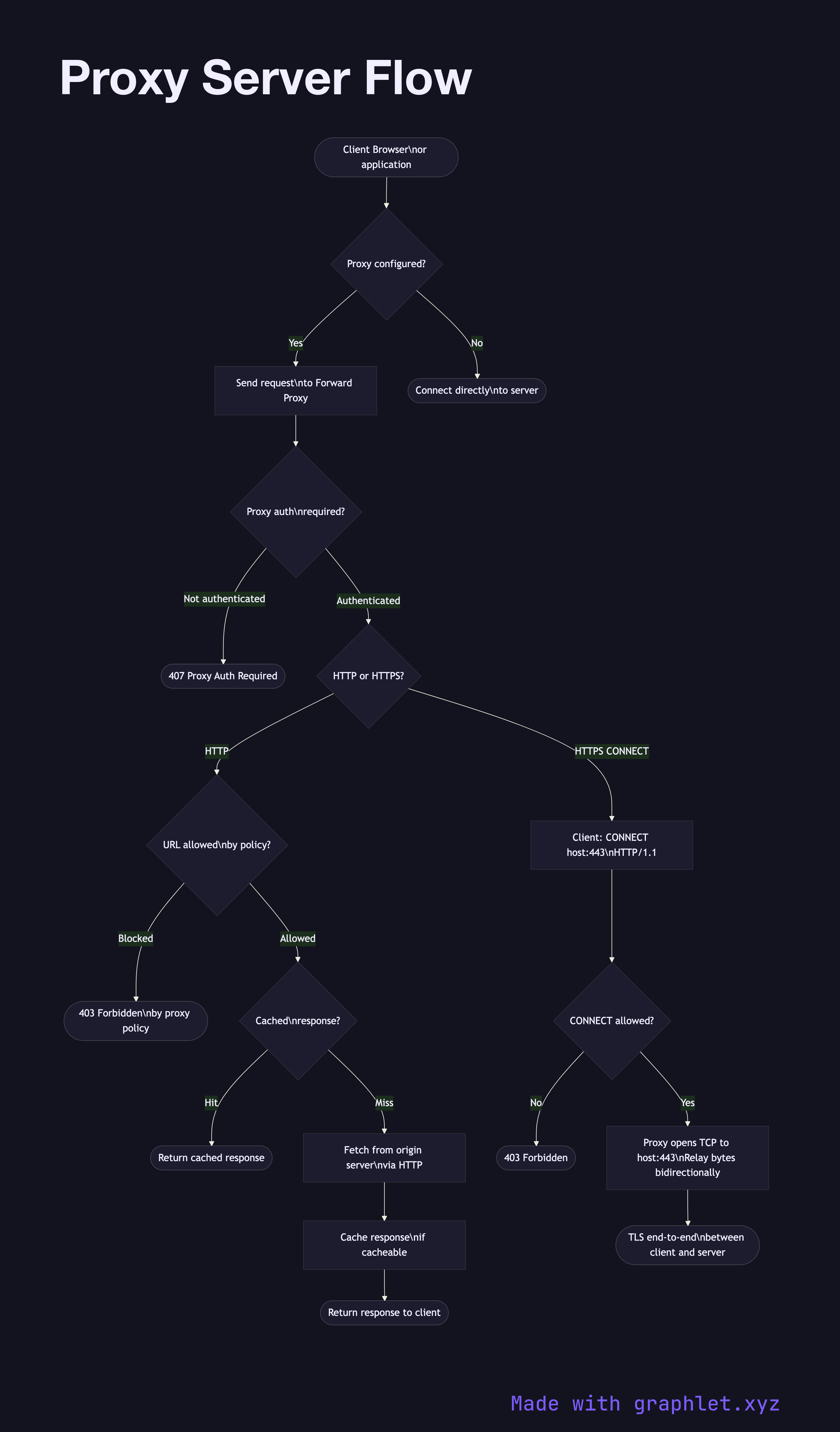
Explicit Proxy Configuration: Clients are configured (manually or via WPAD/PAC files) to send all HTTP requests to the proxy instead of directly to the destination. The proxy reads the Host header (HTTP) or CONNECT method (HTTPS) to determine the actual destination.
HTTP Proxying: For plain HTTP, the client sends the full URL (GET http://example.com/path HTTP/1.1) rather than just the path. The proxy fetches the resource and can cache it, transforming or filtering responses as configured.
HTTPS CONNECT Tunneling: For HTTPS, the proxy cannot decrypt the traffic (it doesn't have the server's private key). The client sends CONNECT example.com:443 HTTP/1.1 to establish a TCP tunnel through the proxy. The proxy opens a TCP connection to the target and relays bytes in both directions. TLS is negotiated end-to-end through this tunnel.
Access Control: Organizations use forward proxies to enforce URL filtering policies — blocking categories of sites, logging traffic for compliance, or enforcing authentication before internet access.
Caching: Forward proxies can cache HTTP responses, reducing bandwidth usage for commonly accessed resources. This is less valuable today with widespread HTTPS (proxies can't cache encrypted responses without certificate interception).