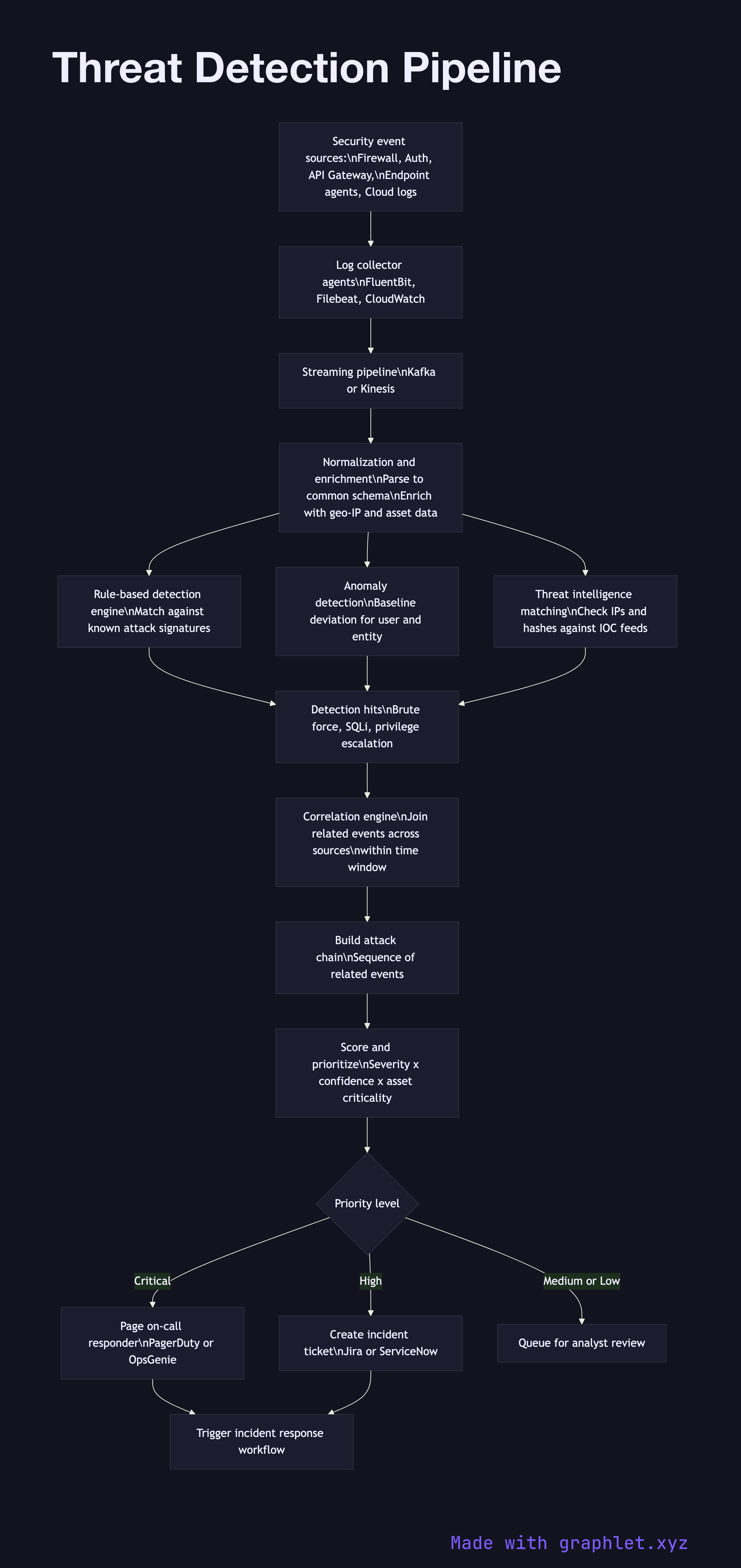
Threat Detection Pipeline
A threat detection pipeline is a real-time data processing system that ingests security events from multiple sources, applies detection rules and machine learning models, correlates signals across sources, and generates prioritized alerts for security teams.
A threat detection pipeline is a real-time data processing system that ingests security events from multiple sources, applies detection rules and machine learning models, correlates signals across sources, and generates prioritized alerts for security teams.
The pipeline begins with data ingestion. Security events flow in from diverse sources: firewall logs, authentication logs, API gateway access logs, endpoint detection agents, network flow data (NetFlow/IPFIX), cloud provider CloudTrail or Audit Logs, and application security logs. Each source has a different format and schema — the pipeline normalizes all events to a common format, typically a schema like OCSF (Open Cybersecurity Schema Framework) or a SIEM-specific format.
The normalized event stream passes through detection engines. Rule-based detection matches events against known attack signatures and behavioral rules — for example: "more than 10 failed login attempts from the same IP in 60 seconds" (brute force), "login from a new country immediately after a domestic login" (credential stuffing with impossible travel), or "API key used from 50 different IPs in 1 minute" (API key compromise). Threshold-based and anomaly-based rules cover different attack classes.
Correlation is where individual events are linked into attack chains. A single failed login is noise; 50 failed logins followed by a successful login followed by a privilege escalation is a high-confidence incident. The correlation engine maintains state across a time window and joins events by shared identifiers (user ID, IP, session ID).
Correlated detections are scored and prioritized by severity, confidence, and asset criticality. High-severity alerts are routed to on-call responders via PagerDuty, Slack, or ticketing systems. All alerts feed the Security Incident Response workflow. Raw events are also forwarded to long-term storage for forensic investigation and threat hunting.