Infrastructure Drift Detection
Infrastructure drift detection is the automated process of comparing the actual state of cloud infrastructure against the desired state declared in Infrastructure as Code — identifying unauthorized changes, configuration mutations, and resource deletions before they cause incidents.
Infrastructure drift detection is the automated process of comparing the actual state of cloud infrastructure against the desired state declared in Infrastructure as Code — identifying unauthorized changes, configuration mutations, and resource deletions before they cause incidents.
How drift detection works
Drift occurs when the real state of a resource diverges from what is declared in IaC configuration. This can happen through manual console changes (an engineer tweaks a security group rule), automated scaling adjustments that persist beyond their intended scope, or resource changes made by cloud provider maintenance operations.
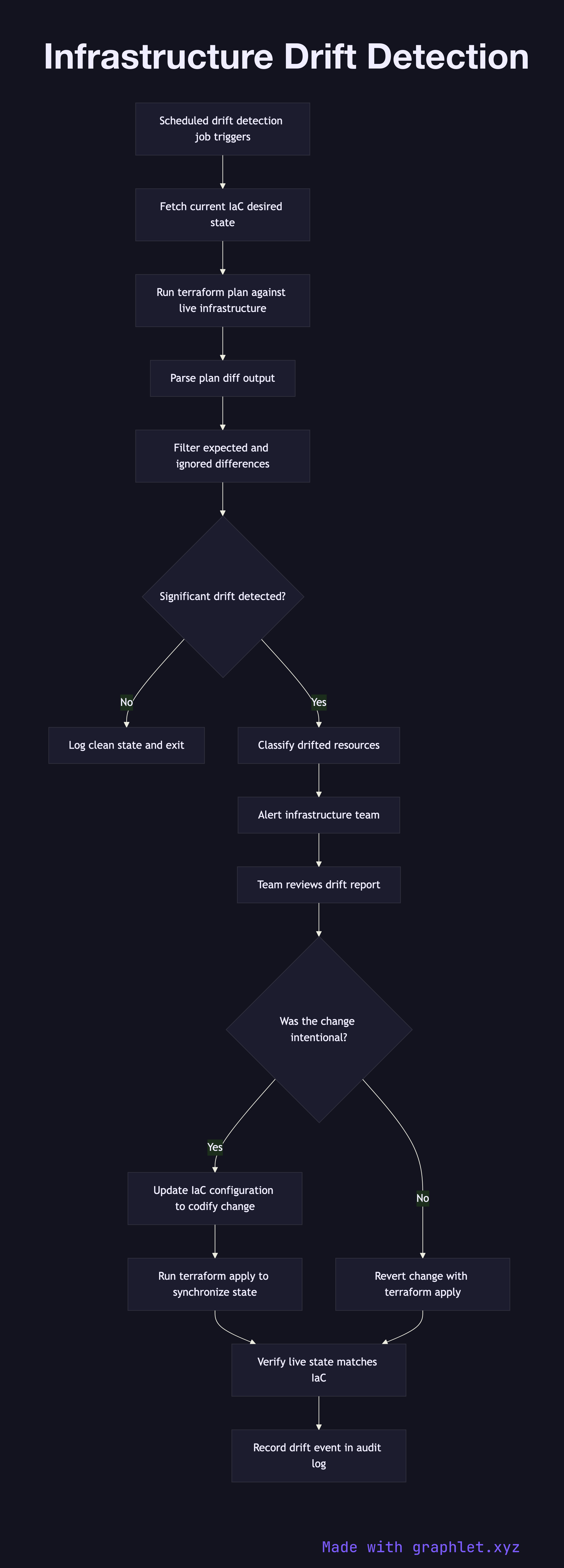
A scheduled drift detection job runs terraform plan (or the equivalent IaC tool command) against the live infrastructure without applying any changes. The plan output is a diff: resources where the live state matches the declared state are reported as no-change; resources where they differ are reported as needing updates. Resources that exist in the real environment but not in the IaC configuration (orphaned resources) are flagged as unmanaged.
The diff output is parsed and evaluated for significance. Minor, expected differences (like auto-generated resource IDs) are filtered by ignore rules. Significant drift — a changed security group ingress rule, a modified IAM policy, a deleted monitoring alarm — triggers an alert to the infrastructure team.
The team reviews the drift report. If the change was intentional (perhaps an emergency hotfix was applied manually), the IaC configuration is updated to codify the change and a normal Infrastructure Provisioning run brings the IaC back in sync. If the change was unauthorized or accidental, it is reverted by running terraform apply to restore the declared state. All drift events are logged for compliance and security review.